Endpoint Detection And Response (EDR) Market Size and Share
Endpoint Detection And Response (EDR) Market Analysis by Mordor Intelligence
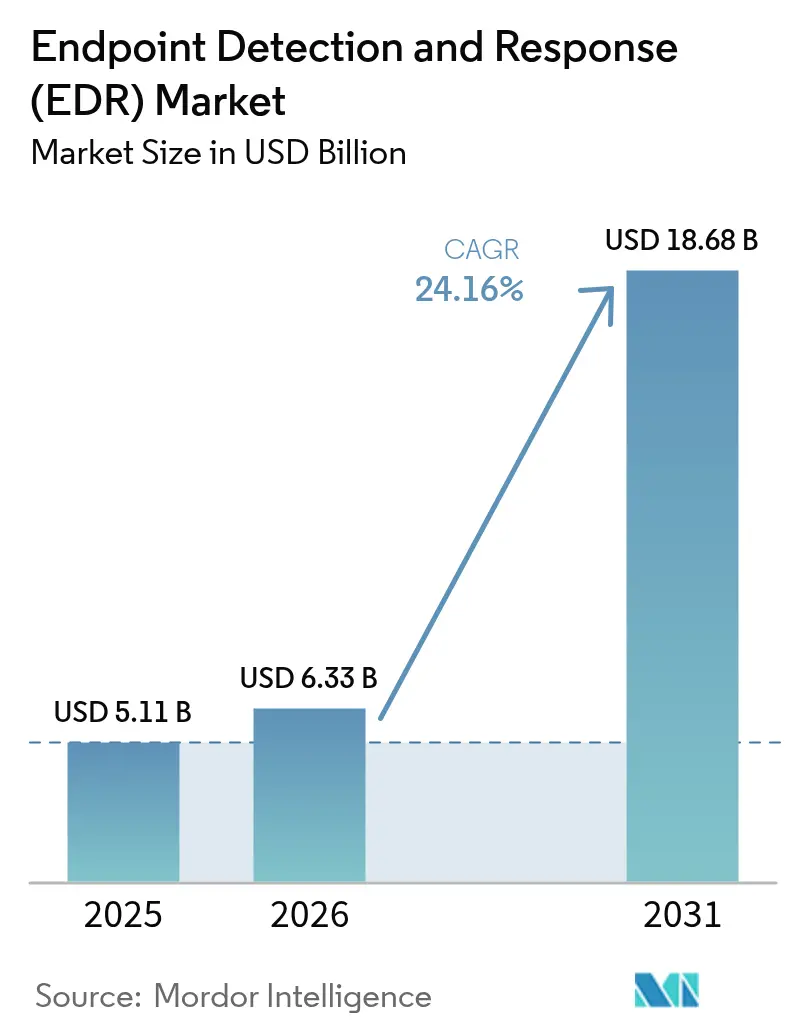
The endpoint detection and response market size is projected to expand from USD 5.11 billion in 2025 and USD 6.33 billion in 2026 to USD 18.68 billion by 2031, registering a CAGR of 24.16% between 2026 and 2031. Heightened federal procurement rules, the commercialization of ransomware toolkits, and a steady pivot to cloud-delivered security all accelerated refresh cycles, turning EDR from an optional upgrade into a line-item requirement. Vendors added identity analytics, kernel-level telemetry, and cloud workload coverage, while managed service providers lowered the entry cost for small businesses. At the same time, the July 2024 global outage linked to a faulty agent update underscored the operational risk of single-vendor dependence, motivating buyers to favor phased rollouts and, in some cases, multi-agent strategies. As the endpoint detection and response market advances, suppliers that marry zero-trust identity signals with endpoint behavior and container visibility gain a defensible edge.
Key Report Takeaways
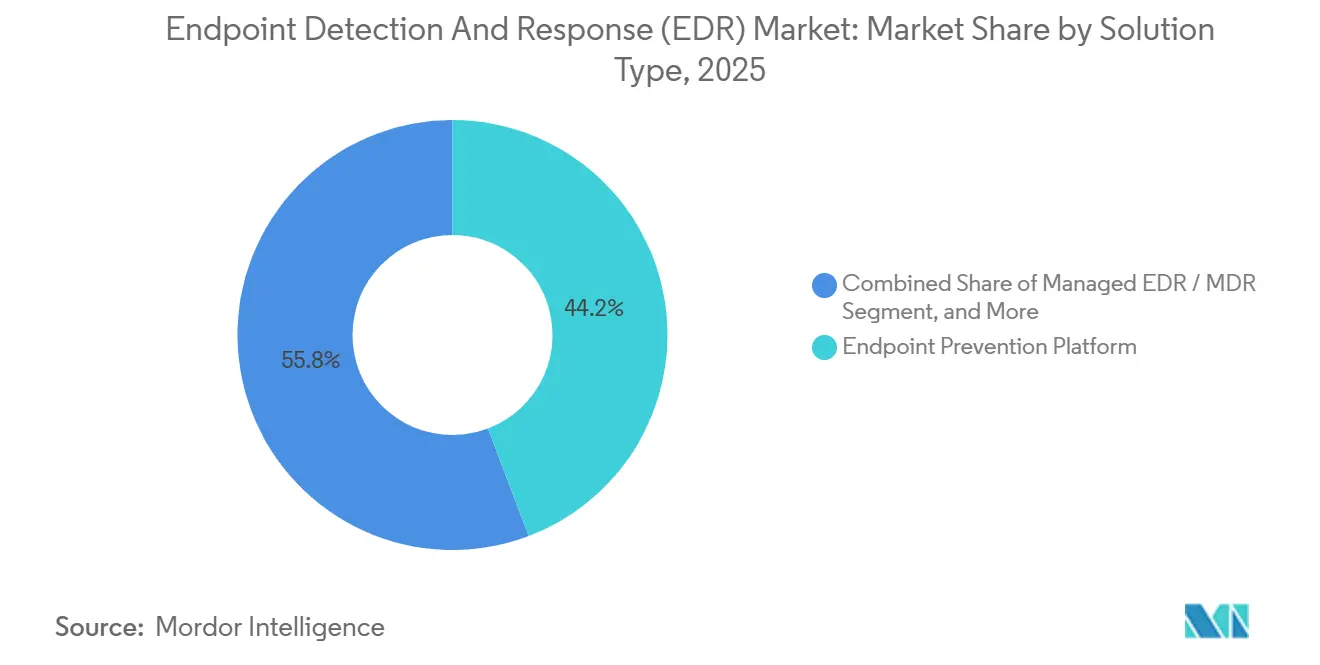
- By solution type, endpoint prevention platforms led with 44.23% of endpoint detection and response market share in 2025, while identity-threat detection and response is forecast to record the fastest 24.83% CAGR through 2031.
- By deployment model, cloud-delivered agents commanded 68.12% share of the endpoint detection and response market size in 2025, and are projected to expand at a 24.93% CAGR over 2026-2031.
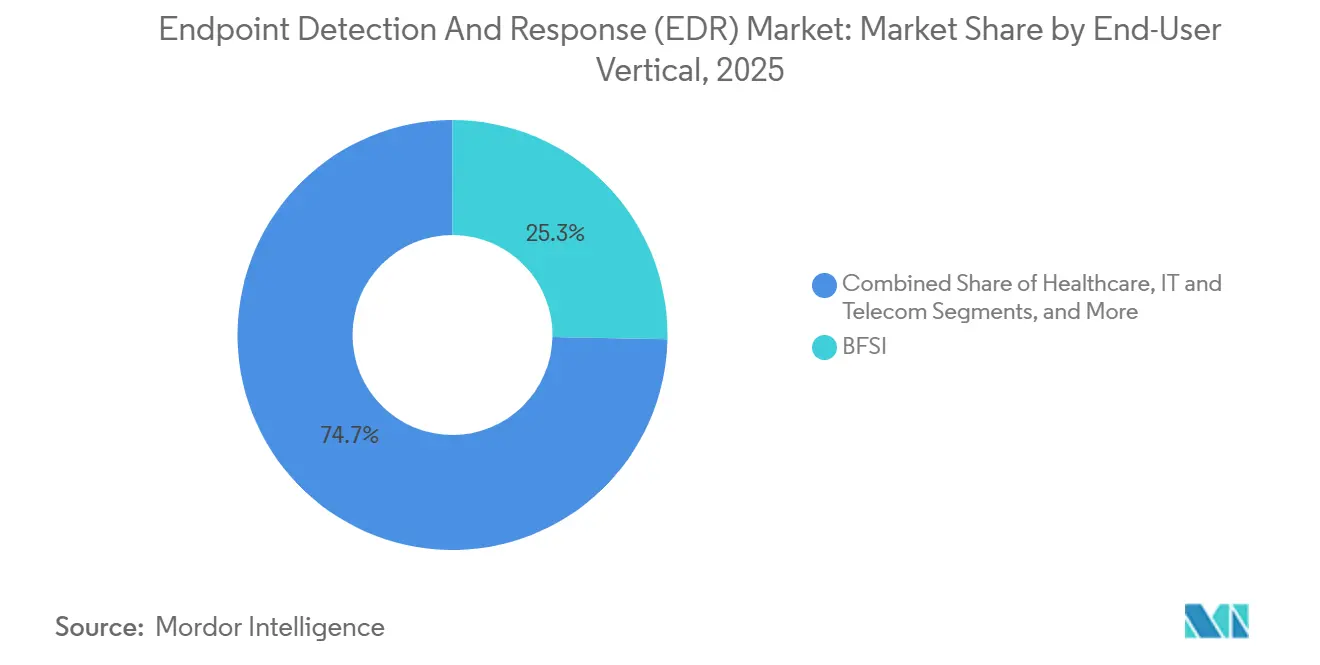
- By end-user vertical, banking, financial services, and insurance dominated spending with 25.31% in 2025; healthcare is on track to grow at a 25.23% CAGR to 2031.
- By enterprise size, large organizations accounted for 63.38% of deployments in 2025, yet the small- and medium-enterprise cohort is expected to post a 25.03% CAGR through 2031.
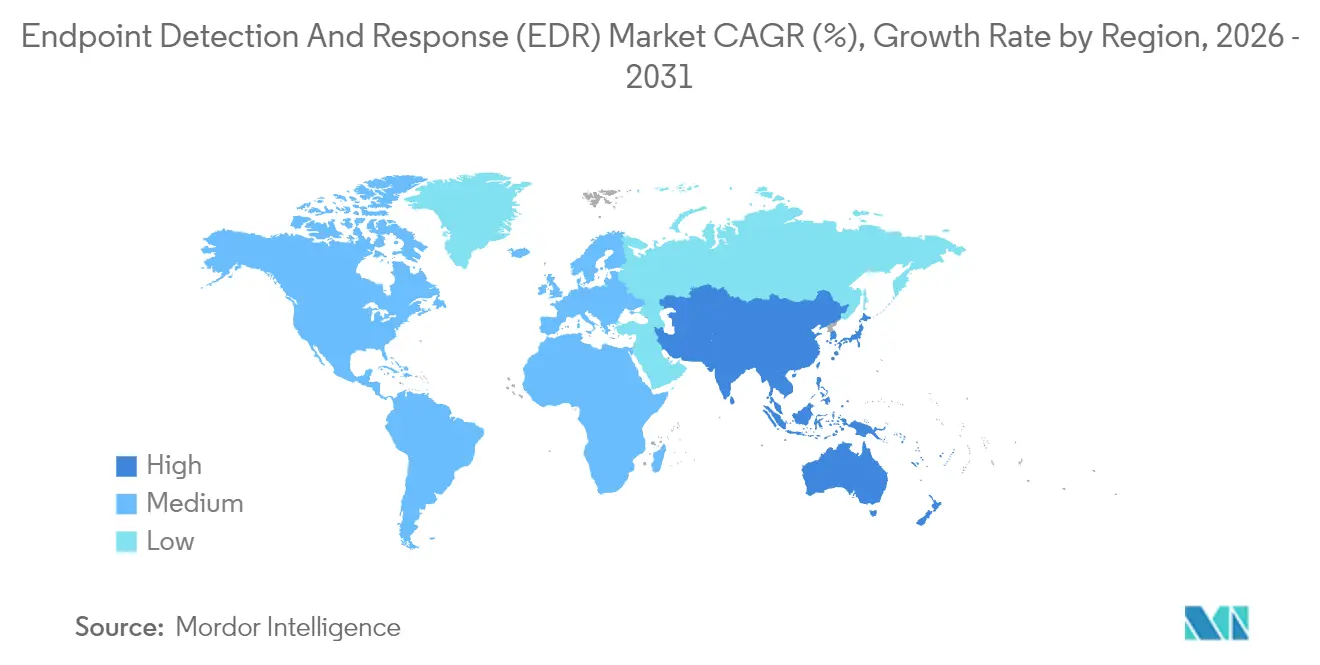
- By geography, North America generated 39.51% of global revenue in 2025, whereas the Middle East is poised to be the fastest-growing region with a 24.73% CAGR to 2031.
Note: Market size and forecast figures in this report are generated using Mordor Intelligence’s proprietary estimation framework, updated with the latest available data and insights as of 2026.
Global Endpoint Detection And Response (EDR) Market Trends and Insights
Drivers Impact Analysis*
| Driver | (~) % Impact on CAGR Forecast | Geographic Relevance | Impact Timeline |
|---|---|---|---|
| Soaring Federal EDR Mandates (EO 14028) | +4.2% | North America and allied defense contractors in Europe and Asia-Pacific | Short term (≤ 2 years) |
| Ransomware-as-a-Service Explosion | +5.8% | Global, highest in North America, Europe, and healthcare-dense locations | Medium term (2-4 years) |
| Shift to Identity-Centered Zero-Trust SOC | +3.9% | North America and Europe core, spreading to Asia-Pacific financial hubs | Medium term (2-4 years) |
| Surge in Cloud Workload Protection Integration | +4.6% | Global, led by North America and Europe, gaining traction in Middle Eastern sovereign-cloud projects | Medium term (2-4 years) |
| Demand for Unified Agent Platforms | +3.1% | Global, strongest among SME-rich economies in North America, Europe, and Asia-Pacific | Long term (≥ 4 years) |
| SMB-Led Managed-Service Pull | +2.9% | North America and Europe initially, widening to Latin America and Southeast Asia | Long term (≥ 4 years) |
| Source: Mordor Intelligence | |||
Soaring Federal EDR Mandates
The United States Executive Order 14028 obliged civilian agencies to install EDR on 80% of endpoints by September 2024, catalyzing rapid vendor authorizations under FedRAMP High and driving similar adoption among defense contractors and 23 U.S. states.[1]Cybersecurity and Infrastructure Security Agency, “Executive Order on Improving the Nation’s Cybersecurity,” CISA, cisa.gov The public-sector wave validated EDR as a compliance baseline, sparking parallel rollouts in Canada, the United Kingdom, and Australia, where suppliers sought to maintain security equivalence for joint programs. As procurement teams embedded EDR language into bid solicitations, platform vendors accelerated roadmaps for identity analytics and continuous diagnostics to win federal business. The mandate’s ripple effect expanded FedRAMP-certified offerings and encouraged agencies to fund zero-trust pilots that integrate endpoint signals with authentication telemetry. Collectively, the compliance orbit shortened refresh cycles across the endpoint detection and response market, reinforcing its transition from optional upgrade to default security layer.
Ransomware-as-a-Service Explosion
Turn-key affiliate programs slashed the technical barrier to entry for cyber-extortion, fueling a 74% jump in ransomware complaints and USD 1.1 billion in losses logged by the FBI Internet Crime Complaint Center in 2024.[2]Federal Bureau of Investigation, “Internet Crime Report 2024,” FBI, fbi.gov Healthcare bore the brunt, with 389 U.S. hospitals forced to divert ambulances after patient record encryption. Signature antivirus crumbled against polymorphic binaries that mutate faster than definition updates, pushing organizations toward behavior-based EDR that scores process injection, registry tampering, and file-encryption patterns in real time. Vendors retrained machine-learning models on ransomware telemetry from millions of endpoints, and managed detection services began to guarantee sub-15-minute dwell times for ransomware events. The threat’s global reach sustains elevated budget priority, underpinning the robust outlook for the endpoint detection and response market.
Shift to Identity-Centered Zero-Trust SOC
While zero-trust guidelines appeared in NIST SP 800-207, mass adoption only gained steam in 2024 as credential-theft campaigns bypassed perimeter defenses. Microsoft estimated that 99.9% of compromised accounts lacked multi-factor authentication in that year. In response, EDR vendors stitched user-behavior analysis into their consoles, flagging impossible-travel logins, privilege escalations, and anomalous Kerberos ticket requests alongside endpoint anomalies. The resulting identity-threat detection and response category delivers unified visibility spanning devices and accounts, reducing analyst context-switching and improving lateral-movement detection. As procurement teams insist on zero-trust roadmaps, platforms melding identity and endpoint telemetry solidify competitive advantage, nudging the endpoint detection and response market toward holistic threat-protection suites.
Surge in Cloud Workload Protection Integration
Hybrid architectures left blind spots; 67% of enterprises split workloads across on-premises and public clouds in 2025. To close visibility gaps, EDR suppliers embedded cloud workload protection, ingesting logs from AWS GuardDuty, Azure Security Center, and container runtimes. Analysts can now trace an attack from a phished laptop to an S3 bucket exfiltration within a single console, trimming mean time to containment. Middle Eastern sovereign-cloud mandates multiplied demand, as regulators in Saudi Arabia and the UAE require endpoint and cloud telemetry to stay within national borders. The cross-layer integration cements EDR as the nervous system of extended detection and response, fortifying growth trajectories across the endpoint detection and response market.
Restraints Impact Analysis*
| Restraint | (~) % Impact on CAGR Forecast | Geographic Relevance | Impact Timeline |
|---|---|---|---|
| Credential-Stealing EDR-Killer Toolkits | −2.1% | Global, concentrated in Eastern Europe and Southeast Asia cybercrime ecosystems | Short term (≤ 2 years) |
| CrowdStrike-Style Agent Update Outages | −1.9% | Global, heightened in North America and Europe after the July 2024 incident | Short term (≤ 2 years) |
| Mis-Configured AI Models Causing Alert Flood | −1.7% | Global, acute where SOC maturity is limited | Medium term (2-4 years) |
| Open-Source Agent Forks Driving Price Pressure | −1.4% | Global, most visible in cost-sensitive SME markets and emerging economies | Long term (≥ 4 years) |
| Source: Mordor Intelligence | |||
Credential-Stealing EDR-Killer Toolkits
Tools that issue direct system calls through frameworks such as SysWhispers evade user-mode API hooks, neutering conventional endpoint analytics. MITRE recorded 47 publicly documented EDR-evasion techniques by 2024.[3]MITRE Corporation, “ATT&CK Framework – EDR Evasion Techniques,” MITRE, attack.mitre.org Underground service operators monetize these exploits for USD 10-500 per credential set, forcing vendors to insert kernel-level drivers and minifilters that capture low-level events. The deeper instrumentation exacts a performance toll, especially on thin clients and industrial controllers, creating tension between detection breadth and resource overhead. Until kernel defenses mature, the tactic trims near-term gains in the endpoint detection and response market.
CrowdStrike-Style Agent Update Outages
A logic flaw in a July 2024 Falcon sensor update pushed 8.5 million Windows machines into boot loops, grounding thousands of airline flights and exposing USD 500 million in losses at one carrier. Enterprises answered with canary rollouts that limit updates to 5% of endpoints before general release, stretching patch windows from hours to days. Others added secondary agents on critical assets to spread operational risk, spurring complexity and license costs. The episode dampened confidence in cloud-pushed binaries, slowing uptake among risk-averse sectors and shaving points off the endpoint detection and response market’s near-term CAGR.
*Our updated forecasts treat driver/restraint impacts as directional, not additive. The revised impact forecasts reflect baseline growth, mix effects, and variable interactions.
Segment Analysis
By Solution Type: Identity Analytics Accelerates Adoption
Identity-threat detection and response posted a 24.83% CAGR through 2031, outgunning traditional endpoint prevention suites that still held 44.23% of endpoint detection and response market share in 2025. Buyers prize tools that correlate Active Directory queries with process behavior, isolating privilege escalations in minutes. The endpoint detection and response market size for identity-centric offerings is projected to expand rapidly as zero-trust programs mature across regulated sectors. In parallel, managed detection packages bundle these capabilities for resource-constrained firms, pushing platform vendors to open multitenant APIs.
Hybrid identity-endpoint convergence also propels acquisition activity, with endpoint specialists scooping up identity startups to compress time-to-feature parity. As vendors integrate graph analytics and credential attack heuristics, SOC analysts reduce console sprawl and speed triage. The outcome is a stickier customer base that values fewer panes of glass and shorter learning curves, reinforcing revenue durability in the endpoint detection and response market.

By Deployment Model: Cloud Services Lead, Air-Gaps Endure
Cloud-delivered agents controlled 68.12% of installations in 2025 and are on course for a 24.93% CAGR, mirroring the corporate shift toward SaaS governance dashboards. The endpoint detection and response market size attributable to software-as-a-service models rises as remote workforces normalize and internet-facing devices outnumber on-prem nodes. Instant policy updates, global threat-intelligence feeds, and subscription pricing resonate with finance, retail, and higher education.
Yet on-premises and air-gapped deployments retained 31.88% share, a figure unlikely to vanish amid classified networks and operational-technology sites where downtime means production losses. Energy utilities, defense labs, and semiconductor fabs still favor offline patch vetting, especially after the 2024 agent update mishap. This dual-track demand keeps appliance revenues afloat and encourages vendors to support hybrid licensing, preserving optionality within the endpoint detection and response market.
By End-User Vertical: Healthcare Outpaces BFSI
Banks, insurers, and capital-market players invested the most in 2025, taking 25.31% of spending thanks to PCI-DSS rules that insist on continuous endpoint monitoring. Healthcare is the fastest climber, advancing at a 25.23% CAGR as hospital ransomware events quadrupled emergency diversions in 2024.[4]U.S. Department of Health and Human Services, “Healthcare Sector Cybersecurity Performance Goals,” HHS, hhs.gov The endpoint detection and response market share for medical providers will expand as regulators threaten steep fines for protected-health-information breaches.
Telecom operators, retailers, and industrial players follow, adapting agents to embedded Windows machines and point-of-sale terminals. Emerging economies lean on lightweight sensors and managed detection backstops to stretch thin security budgets. Collectively, vertical diversification cushions the endpoint detection and response market against sector-specific spending lulls.

By Enterprise Size: MSP Programs Democratize Protection
Large enterprises still own 63.38% of deployments due to their in-house SOCs and volume pricing. Nevertheless, small businesses are registering a 25.03% CAGR as managed security providers offer per-seat bundles from USD 5 per endpoint monthly. Multi-tenant dashboards let service partners orchestrate updates, run hunts, and deliver executive reports without breaching client separation. The talent gap 3.5 million unfilled cybersecurity roles worldwide in 2025 makes outsourcing irresistible, steering incremental revenue into the endpoint detection and response market.
Managed service innovations, such as automated root-cause narration and one-click isolation, further condense analyst workloads. As more MSPs white-label leading platforms, OEM arrangements open secondary revenue streams for vendors, widening geographic reach and compressing customer acquisition costs.
Geography Analysis
North America generated 39.51% of global revenue in 2025, propelled by federal EDR mandates and state breach-notification fines that escalate per compromised record. U.S. buyers also benefit from deep MSSP ecosystems and abundant cyber-insurance discounts tied to EDR deployment. Canada and Mexico follow similar patterns, with cross-border suppliers ensuring compliance parity.
Europe’s NIS2 Directive, effective October 2024, obliged essential service operators to run continuous endpoint monitoring, broadening the addressable base across 27 member states. Data residency laws push multinational firms to spin up regional EDR clusters inside the bloc, fueling incremental license volume. Meanwhile, Asia-Pacific demand concentrates in Singapore, Hong Kong, and Tokyo, where banking supervisors require EDR on terminals that execute cross-border payments. China’s data-localization rules foster domestic agent ecosystems overseen by the Cyberspace Administration of China.
The Middle East is the sprinter, showing a 24.73% CAGR through 2031 as Saudi Arabia’s National Cybersecurity Authority designates EDR mandatory for critical-infrastructure operators. The UAE stipulates that telemetry remain inside sovereign clouds, spawning localized EDR instances with Arabic dashboards. Israel’s defense supply chain aligns with state guidance that ranks EDR among baseline controls. Latin America and Africa lag in per-endpoint spending; however, cloud-delivered agents priced for SMEs and bundled with managed services promise to close the gap, enlarging the global endpoint detection and response market footprint.
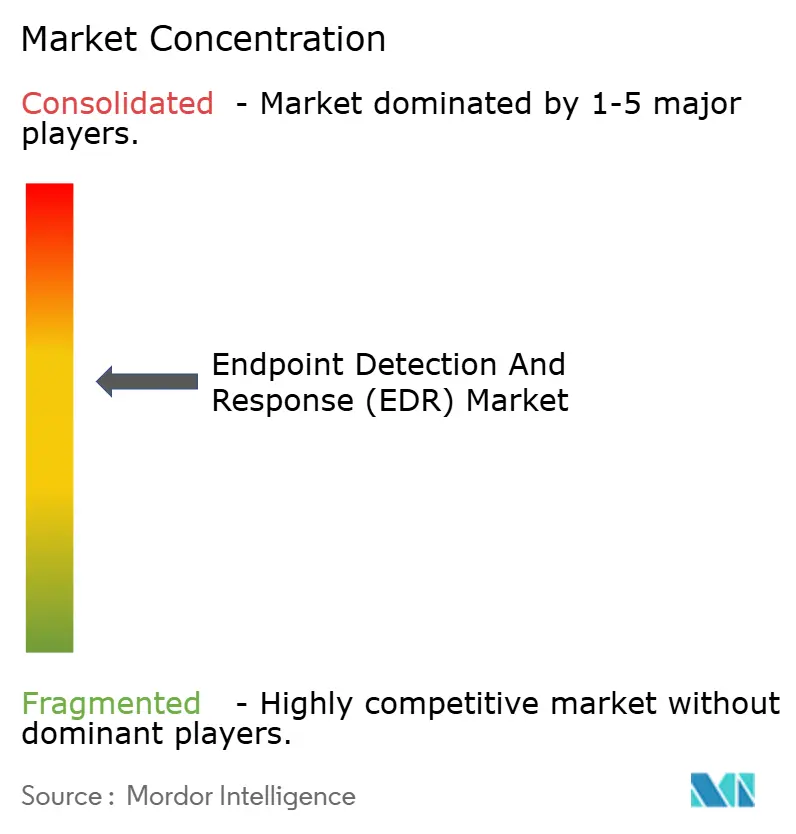
Competitive Landscape
The endpoint detection and response market is moderately concentrated. The top five vendors CrowdStrike, Microsoft, SentinelOne, Palo Alto Networks, and Trend Micro captured roughly 58% of 2025 revenue, while more than 40 challengers fight over the remainder. Competition centers on unified extended detection and response suites that blend endpoint, network, cloud, and identity telemetry. Generative-AI assistants that summarize alerts and generate hunt queries now headline product roadmaps, with Microsoft Copilot for Security already embedded in Defender for Endpoint.
Managed detection specialists such as Huntress Labs and Red Canary differentiate via fixed per-seat pricing and 24/7 human-led hunting, grabbing share inside the small-business corridor. Open-source agents, including Wazuh and Velociraptor, restrain pricing in cost-sensitive markets, yet enterprises often reserve community editions for low-value assets while paying for premium features on crown-jewel systems.
The post-outage appetite for multi-vendor stacks forces suppliers to improve API openness and coexistence testing. Lightweight sensors tailored to operational technology remain under-served, representing an avenue for niche entrants to disrupt incumbents.
Endpoint Detection And Response (EDR) Industry Leaders
CrowdStrike Holdings Inc.
Microsoft Corporation
SentinelOne Inc.
VMware by Broadcom
Trend Micro Inc.
- *Disclaimer: Major Players sorted in no particular order


Recent Industry Developments
- February 2026: Palo Alto Networks Inc. is investing USD 250 million to expand its Cortex XDR platform, integrating real-time threat intelligence while maintaining FedRAMP High authorization standards.
- January 2026: The U.S. Department of Defense awarded SentinelOne Inc. a USD 180 million contract to deploy its Singularity XDR platform across 500,000 classified network endpoints.
- January 2026: Microsoft Corporation has introduced the agentless scanning feature for Defender for Endpoint, enabling security teams to inspect virtual machines and containers without kernel-mode driver installations.
- December 2025: Trend Micro Inc. acquired Snyk Ltd.'s infrastructure-as-code security division for USD 320 million, integrating developer-focused vulnerability scanning into Vision One to enhance early EDR coverage.
Global Endpoint Detection And Response (EDR) Market Report Scope
The Endpoint Detection and Response (EDR) market is witnessing significant growth due to the increasing frequency of cyber threats and the rising adoption of advanced security solutions across various industries. Organizations are prioritizing endpoint security to safeguard sensitive data and ensure compliance with regulatory standards, driving the demand for EDR solutions globally.
The Endpoint Detection and Response Report is Segmented by Solution Type (Endpoint Prevention Platform, Cloud-Native EDR / CWP-Integrated, Identity-Threat Detection and Response, Managed EDR / MDR), Deployment Model (Cloud-Delivered, On-Prem / Air-Gapped), End-User Vertical (BFSI, Healthcare, IT and Telecom, Industrial and Defense, Retail and e-Commerce, Energy and Utilities, Manufacturing, Rest of End-User Vertical), Enterprise Size (SME, Large Enterprises), and Geography (North America, Europe, Asia-Pacific, Middle East, Africa, South America). Market Forecasts are Provided in Terms of Value (USD).
| Endpoint Prevention Platform (EPP + EDR) |
| Cloud-Native EDR / CWP-Integrated |
| Identity-Threat Detection and Response (ITDR) |
| Managed EDR / MDR |
| Cloud-Delivered |
| On-Prem / Air-Gapped |
| BFSI |
| Healthcare |
| IT and Telecom |
| Industrial and Defense |
| Retail and e-Commerce |
| Energy and Utilities |
| Manufacturing |
| Rest of End-User Vertical |
| Small and Medium Enterprises (SME) |
| Large Enterprises |
| North America | United States |
| Canada | |
| Mexico | |
| Europe | United Kingdom |
| Germany | |
| France | |
| Italy | |
| Rest of Europe | |
| Asia-Pacific | China |
| Japan | |
| India | |
| South Korea | |
| Rest of Asia-Pacific | |
| Middle East | Israel |
| Saudi Arabia | |
| United Arab Emirates | |
| Turkey | |
| Rest of Middle East | |
| Africa | South Africa |
| Egypt | |
| Rest of Africa | |
| South America | Brazil |
| Argentina | |
| Rest of South America |
| By Solution Type | Endpoint Prevention Platform (EPP + EDR) | |
| Cloud-Native EDR / CWP-Integrated | ||
| Identity-Threat Detection and Response (ITDR) | ||
| Managed EDR / MDR | ||
| By Deployment Model | Cloud-Delivered | |
| On-Prem / Air-Gapped | ||
| By End-User Vertical | BFSI | |
| Healthcare | ||
| IT and Telecom | ||
| Industrial and Defense | ||
| Retail and e-Commerce | ||
| Energy and Utilities | ||
| Manufacturing | ||
| Rest of End-User Vertical | ||
| By Enterprise Size | Small and Medium Enterprises (SME) | |
| Large Enterprises | ||
| By Geography | North America | United States |
| Canada | ||
| Mexico | ||
| Europe | United Kingdom | |
| Germany | ||
| France | ||
| Italy | ||
| Rest of Europe | ||
| Asia-Pacific | China | |
| Japan | ||
| India | ||
| South Korea | ||
| Rest of Asia-Pacific | ||
| Middle East | Israel | |
| Saudi Arabia | ||
| United Arab Emirates | ||
| Turkey | ||
| Rest of Middle East | ||
| Africa | South Africa | |
| Egypt | ||
| Rest of Africa | ||
| South America | Brazil | |
| Argentina | ||
| Rest of South America | ||


Key Questions Answered in the Report
What is the current size of the endpoint detection and response market?
The endpoint detection and response market size reached USD 6.33 billion in 2026 and is on course to hit USD 18.68 billion by 2031.
How fast is the endpoint detection and response sector growing?
The market is projected to register a robust 24.16% CAGR between 2026 and 2031, buoyed by federal mandates, ransomware risks, and cloud adoption.
Which deployment model is winning customer preference?
Cloud-delivered endpoint detection and response commands 68.12% share today and is expanding fastest, thanks to centralized management and subscription pricing.
Why is healthcare adopting EDR so rapidly?
Frequent ransomware attacks that disrupted 389 U.S. hospitals in 2024 have pushed healthcare organizations to deploy behavior-based EDR for faster threat containment.
How are small businesses affording advanced detection capabilities?
Managed service providers now bundle endpoint detection and response agents with 24/7 monitoring for as little as USD 5 per endpoint monthly, eliminating the need for in-house SOC staff.
What impact did the 2024 CrowdStrike outage have on buying behavior?
The incident highlighted single-vendor risk, prompting phased update rollouts and, for some firms, multi-agent strategies to ensure business continuity.
Page last updated on: