Cloud Security Software Market Size and Share
Cloud Security Software Market Analysis by Mordor Intelligence
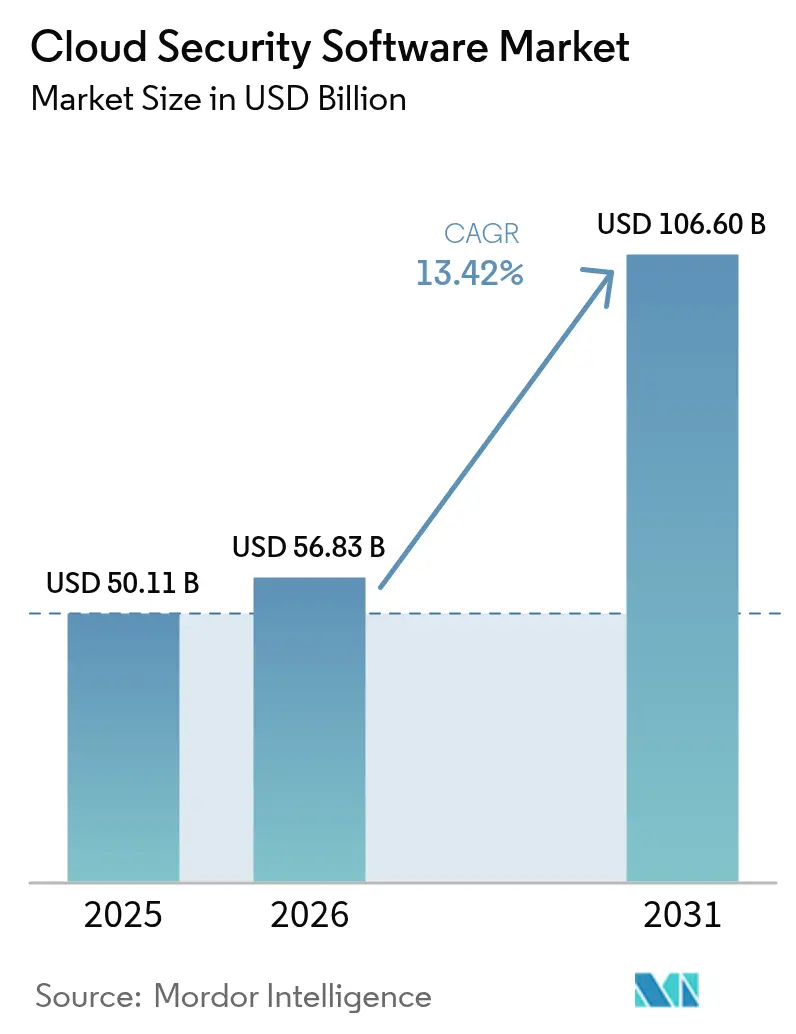
The Cloud Security Software Market size was valued at USD 50.11 billion in 2025 and estimated to grow from USD 56.83 billion in 2026 to reach USD 106.6 billion by 2031, at a CAGR of 13.42% during the forecast period (2026-2031).
This growth trajectory confirms a robust cloud security software market size that is shaped by regulated industries racing to modernize digital infrastructure, the embrace of zero-trust frameworks, and the emergence of generative-AI-driven threats. Heightened compliance obligations, sovereign-cloud policies, and capital spending by hyperscalers have amplified demand for unified security orchestration across multi-cloud deployments. As enterprises shift critical workloads to the public cloud, they prioritize identity management, runtime protection, and automated compliance reporting to streamline risk management and sustain business velocity. Vendor competition now centers on platform consolidation and native AI capabilities that promise faster detection, lower false-positive rates, and seamless integration across diverse cloud environments.
Key Report Takeaways
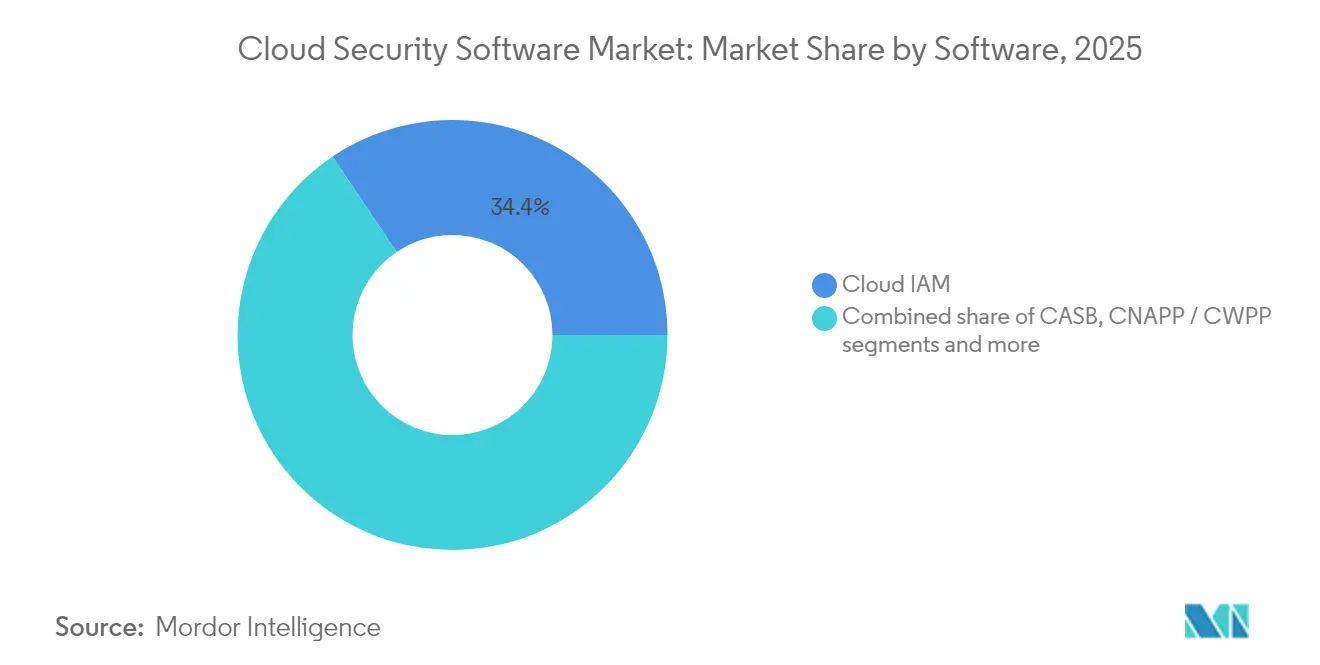
- By software product, Cloud Identity and Access Management led with 34.42% of the cloud security software market share in 2025, whereas Cloud-Native Application Protection Platforms are forecast to expand at a 14.12% CAGR through 2031.
- By deployment mode, public cloud retained 64.85% revenue share in 2025, while hybrid and multi-cloud configurations record the highest projected CAGR at 14.76% to 2031.
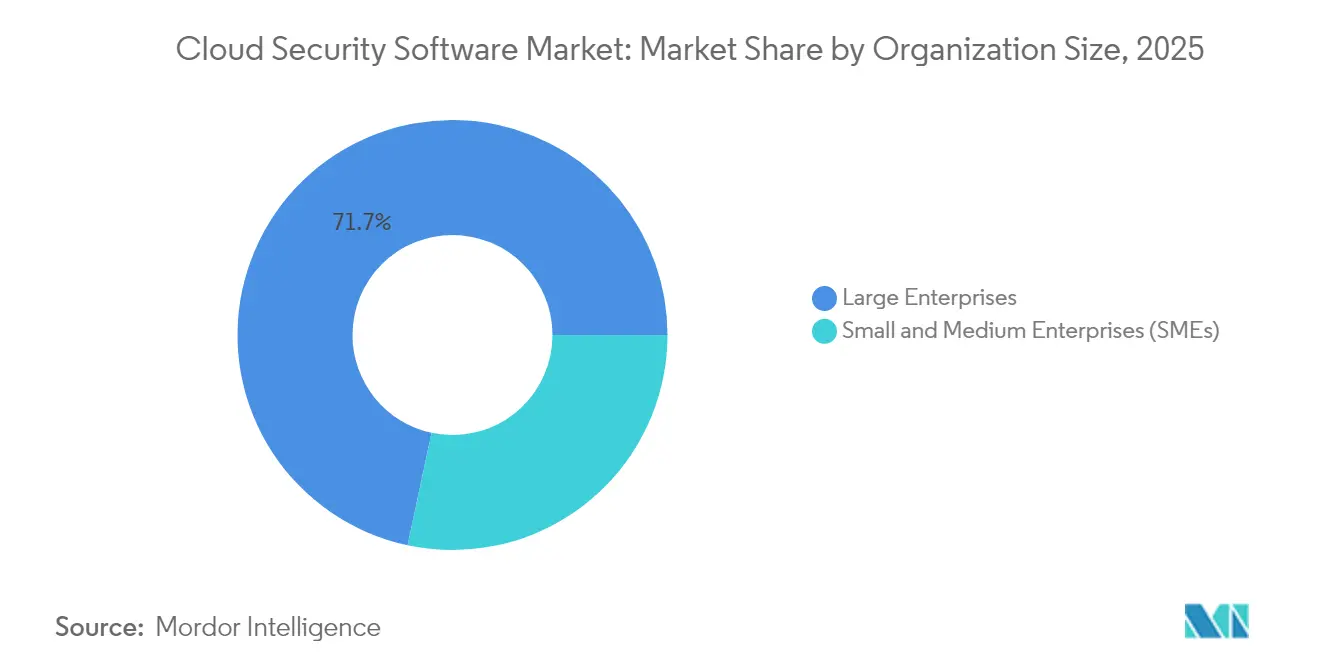
- By organization size, large enterprises held 71.65% of the cloud security software market in 2025; small and medium enterprises post the fastest 15.03% CAGR, signaling broader democratization of advanced security.
- By end-user industry, Banking, Financial Services, and Insurance captured 35.10% of the cloud security software market size in 2025, whereas Information Technology and Telecommunications posts a 13.62% CAGR through 2031.
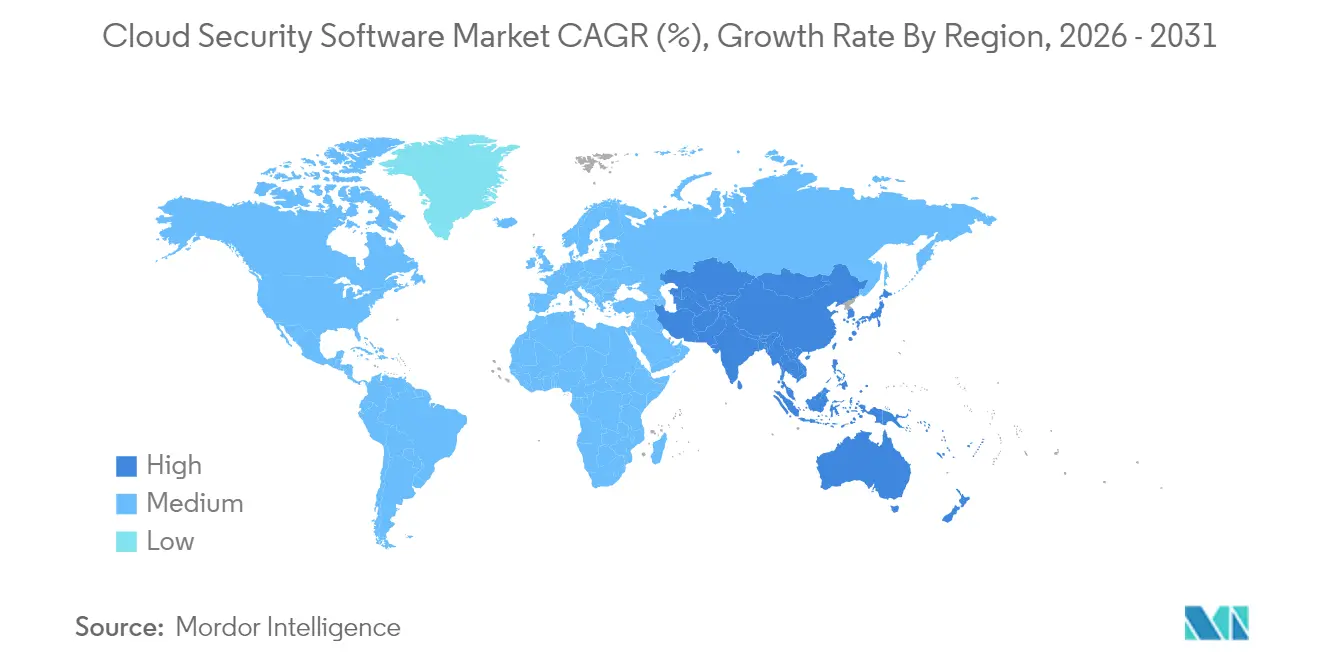
- By geography, North America maintained 40.95% revenue share in 2025, yet Asia-Pacific is the fastest-growing region at 14.32% CAGR.
Note: Market size and forecast figures in this report are generated using Mordor Intelligence’s proprietary estimation framework, updated with the latest available data and insights as of 2026.
Global Cloud Security Software Market Trends and Insights
Drivers Impact Analysis*
| Driver | (~) % Impact on CAGR Forecast | Geographic Relevance | Impact Timeline |
|---|---|---|---|
| Fast-growing public-cloud adoption among regulated industries | +2.8% | Global, especially North America and EU | Medium term (2–4 years) |
| Surge in multi-cloud and hybrid-cloud complexity | +2.1% | Global, high in APAC and North America | Short term (≤ 2 years) |
| Zero-trust architecture mandates | +1.9% | North America and EU, expanding in APAC | Medium term (2–4 years) |
| Generative-AI-driven threat vectors | +1.7% | Global, earliest in North America | Short term (≤ 2 years) |
| Cyber-insurance premium incentives | +1.4% | North America and EU | Long term (≥ 4 years) |
| Sovereign-cloud initiatives | +1.2% | EU and APAC | Long term (≥ 4 years) |
| Source: Mordor Intelligence | |||
Fast-growing Public-cloud Adoption Among Regulated Industries
Regulated enterprises are re-tooling legacy architectures as supervisory bodies update cloud guidance. The Federal Financial Institutions Examination Council now stresses real-time third-party risk monitoring, prompting banks and insurers to adopt automated controls that verify compliance evidence continuously. Healthcare providers likewise align modernization plans with security certifications that deliver competitive benefit rather than mere regulatory box-ticking. Federal Risk and Authorization Management Program reforms further legitimize cloud migrations, cascading adoption expectations across contractors and suppliers. Vendors respond with pre-packaged compliance templates that shorten onboarding times and translate policy into programmatic guardrails across multi-cloud estates[1]Federal Financial Institutions Examination Council, “Cybersecurity Resource Guide,” ffiec.gov.
Surge in Multi-cloud and Hybrid-cloud Complexity
Enterprises typically run workloads on 3.2 cloud providers, multiplying policy silos and integration debt. Disparate APIs and variable security models fuel demand for centralized orchestration able to normalize controls independent of underlying infrastructure. Cloud-native application protection platforms thus gain favor by detecting misconfigurations and runtime anomalies across containers and serverless functions. Organizations originally pursued multi-cloud for diversification but now rely on orchestration to maintain operational viability as cost, performance, and jurisdictional requirements diverge.
Zero-trust Architecture Mandates
Zero-trust shifts perimeter-based defenses toward continuous verification of user, device, and application context. The National Institute of Standards and Technology issued draft API protection guidance that underscores risk-based policies across the full software lifecycle, accelerating procurement of identity-centric tooling that supports granular access decisions[2]National Institute of Standards and Technology, “Special Publication 800-228: API Security Guidance,” nist.gov. Adoption extends beyond federal agencies to commercial entities dealing with distributed workforces and hybrid data flows. Implementation success hinges on scalable identity and access management platforms capable of harmonizing policies without degrading user experience.
Generative-AI-driven Threat Vectors
Generative AI equips bad actors to produce polymorphic malware and persuasive phishing at unprecedented speed, forcing defenders to automate threat analysis at similar velocity. Organizations pilot AI-powered detection engines that sift cloud telemetry for anomalous behavior in real time. Security teams also craft AI governance policies to prevent model drift and data leakage, balancing automation gains against explainability and compliance imperatives.
Restraints Impact Analysis*
| Restraint | (~) % Impact on CAGR Forecast | Geographic Relevance | Impact Timeline |
|---|---|---|---|
| Integration debt with legacy security stacks | –1.8% | Global, notably mature markets | Medium term (2–4 years) |
| Cloud-native skills shortage | –1.3% | Global, acute in APAC | Short term (≤ 2 years) |
| Compliance conflicts across jurisdictions | –0.9% | Global, cross-border firms | Long term (≥ 4 years) |
| Persistent shadow-IT and BYOD behavior | –0.7% | Global, industry-dependent | Medium term (2–4 years) |
| Source: Mordor Intelligence | |||
Integration Debt with Legacy Security Stacks
Security leaders grapple with duplicated tooling and inconsistent policies as cloud controls overlay on-premises investments. Parallel environments obscure attack paths and inflate operating costs, especially when organizations retrofit zero-trust models onto hub-and-spoke networks. Without unified telemetry, threat intelligence remains siloed, and remediation cycles extend, undermining return on security spend.
Cloud-native Skills Shortage
Japan illustrates the global talent gap: 70% of companies cite deficits in cloud technology expertise versus 47% worldwide, even as 94% earmark upskilling as a top priority[3]Linux Foundation, “State of Cloud Native Security Skills Report 2024,” linuxfoundation.org. Scarcity drives project delays, misconfigurations, and rising service costs. Small and medium enterprises feel the pinch most acutely, reinforcing managed services demand to bridge expertise shortfalls.
*Our updated forecasts treat driver/restraint impacts as directional, not additive. The revised impact forecasts reflect baseline growth, mix effects, and variable interactions.
Segment Analysis
By Software: Identity Management Anchors Growth
Cloud Identity and Access Management accounted for a 34.42% cloud security software market share in 2025, reflecting its cornerstone role in zero-trust rollouts. The segment’s entrenched status underpins the broader cloud security software market as organizations prioritize least-privilege policies to mitigate lateral movement risks. Simultaneously, Cloud-Native Application Protection Platforms and Cloud Workload Protection Platforms achieve a 14.12% CAGR through 2031, mirroring the proliferation of containerized workloads that require runtime safeguards. Their ascent joins Cloud Access Security Brokers and vulnerability scanners that integrate within DevSecOps pipelines, offering continuous assessment across development and production.
Demand for unified logging drives Security Information and Event Management modernization, with platforms leveraging machine learning to parse cloud-scale telemetry and accelerate mean-time-to-detect. Vendors further experiment with quantum-resistant algorithms, as demonstrated by SEALSQ’s Crystal Kyber and Crystal Dilithium showcase, signaling the long-term evolution of encryption boundaries. These innovations collectively reshape category borders, encouraging platform vendors to fold adjacent capabilities into consolidated suites for simplified procurement and operations.

By Deployment Mode: Hybrid Complexity Drives Innovation
Public cloud retained 64.85% share of the cloud security software market size in 2025, buoyed by hyperscaler investments that reached USD 215 billion in 2025. Amazon alone allocated more than USD 75 billion, augmenting native security services and geographic redundancy. Despite public cloud scale advantages, hybrid and multi-cloud environments post the fastest 14.76% CAGR as enterprises seek workload portability, data residency assurance, and cost optimization.
Hybrid complexity magnifies the need for policy abstraction, prompting security providers to offer central dashboards that push uniform rules across Kubernetes clusters, SaaS applications, and on-premises assets. Private cloud adoption persists among industries with sensitive intellectual property or latency-critical workloads, though many treat private environments as transitional waypoints toward broader public adoption once compliance hurdles ease.
By Organization Size: SME Acceleration Signals Democratization
Large enterprises controlled 71.65% of the cloud security software market in 2025, shielded by skilled personnel and substantial budgets capable of supporting layered defenses. They invest in orchestration platforms that fuse vulnerability management, runtime protection, and automated compliance into a single pane of glass. Nevertheless, the 15.03% CAGR among small and medium enterprises demonstrates that automation and managed services lower barriers to entry. Low-touch deployment models and subscription pricing allow resource-constrained firms to inherit best-practice configurations without building extensive in-house teams.
Service providers now offer tiered bundles that map essential controls to specific regulatory obligations, delivering predictable cost structures. The democratization trend widens the addressable base, encouraging vendors to streamline user interfaces, integrate AI-based playbooks for incident response, and embed compliance reporting templates that satisfy auditors with minimal manual effort.

By End-User Industry: Financial Services Lead Digital Transformation
Banking, Financial Services, and Insurance maintained a 35.10% share of the cloud security software market size in 2025, captivated by regulatory oversight and high-value digital assets. The Federal Financial Institutions Examination Council’s guidance on third-party cloud risk amplifies spending on identity governance, encryption key management, and continuous control monitoring. Information Technology and Telecommunications industries record a 13.62% CAGR to 2031, reflective of their role as cloud infrastructure stewards and early adopters of AI-infused security.
Healthcare organizations invest in specialized compliance automation to reconcile electronic health record protection with operational efficiency. Retail and Consumer Goods prioritize fraud prevention and data integrity to sustain omnichannel commerce, while manufacturing entities secure industrial IoT deployments linking operational technology to enterprise clouds. This convergence of IT and OT estates accelerates demand for industry-tuned security blueprints capable of addressing unique production uptime and safety requirements.
Geography Analysis
North America retained a 40.95% revenue share in 2025, signifying the largest regional slice of the cloud security software market. Federal Risk and Authorization Management Program modernization boosts confidence in cloud controls across civilian agencies, contractors, and heavily regulated industries. Concurrently, the U.S. Department of Justice Data Security Program introduces fresh compliance layers for telecommunications firms handling foreign data traffic, generating opportunities for automated policy-mapping tools that reconcile overlapping rule sets.
Asia-Pacific is the fastest-growing territory with a 14.32% CAGR through 2031, underpinned by sovereign-cloud directives, 5G rollout, and broad-scale digitization. Yet acute talent shortages threaten execution timelines. Japan’s skills deficit underscores the training imperative, spurring partnerships between universities, cloud providers, and security vendors to expand certification access. China advances domestically sourced security stacks to meet sovereignty mandates, whereas India emphasizes low-cost, scalable solutions to service a diverse enterprise base. Australia, New Zealand, and South Korea leverage advanced network infrastructure to adopt real-time threat detection platforms that ensure low-latency protection for financial trading and smart-factory environments.
Europe navigates the delicate balance between innovation and sovereignty. General Data Protection Regulation and the evolving Network and Information Security Directive shape procurement criteria that favor providers offering data-localization options and transparent audit trails. Germany leads adoption in manufacturing, while France invests in nationally hosted cloud zones to underpin critical infrastructure projects. Post-Brexit, the United Kingdom crafts its own data security stance yet aligns closely enough to facilitate cross-border transfers. Regional harmonization efforts simplify vendor entry, although divergent national timelines for directive transposition continue to complicate uniform rollout strategies.
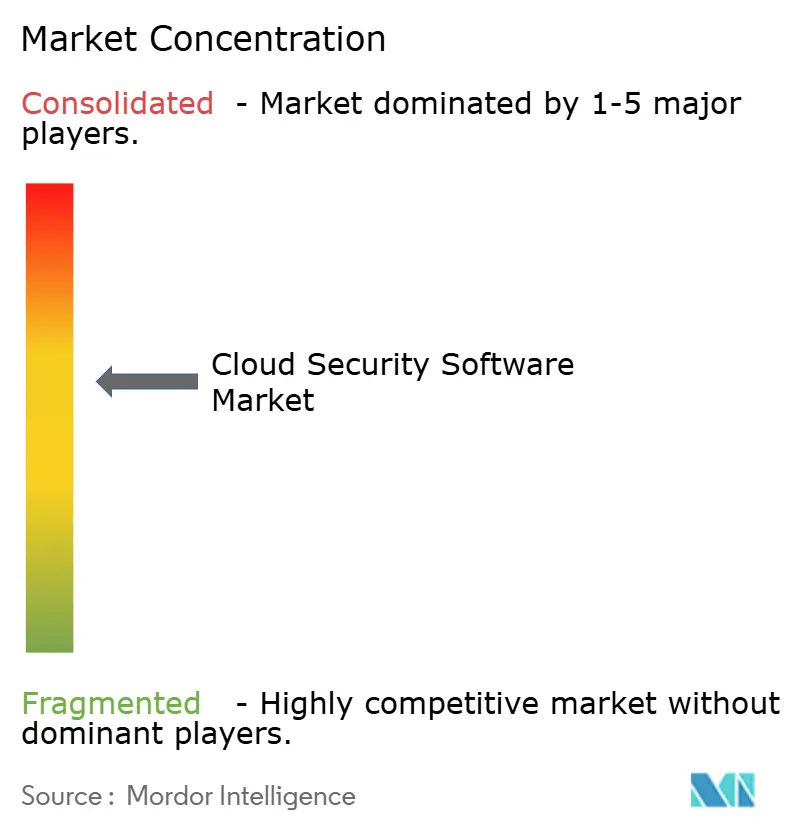
Competitive Landscape
The cloud security software market demonstrates moderate consolidation, propelled by platform vendors acquiring niche innovators to assemble comprehensive suites. Palo Alto Networks posted USD 2.29 billion in quarterly revenue and revealed plans to absorb Protect.ai, signaling aggressive expansion toward AI-driven protection. CrowdStrike’s outage in 2024, which triggered USD 5.4 billion in downstream losses, amplified buyer scrutiny of release-management practices and uptime assurances, nudging vendors to adopt gradual deployment pipelines and real-time rollback mechanisms.
Hyperscalers embed security features inside infrastructure services, compelling specialized vendors to differentiate through deep analytics, policy portability, and verticalized compliance tooling. Start-ups market post-quantum encryption libraries, evidenced by SEALSQ’s IoT-oriented Crystal Kyber showcase, to prepare for quantum threats that could render present-day cryptography obsolete. Investors reward firms that translate AI research into practical detection gains without inflating operational costs. Consequently, product roadmaps prioritize contextual analytics, low-code policy creation, and seamless interoperability across multi-cloud APIs to minimize customer integration debt.
Vendor alliances proliferate as integrated solutions ease procurement fatigue. Service providers curate marketplaces that bundle identity, workload protection, and governance reporting, offering customers subscription flexibility with predictable budgeting. Competitive intensity is expected to persist as players vie for share in high-growth niches such as API security, data security posture management, and continuous compliance automation.
Cloud Security Software Industry Leaders
Check Point Software Technologies
IBM Corporation
Microsoft
Cisco Systems
Amazon Web Services (Security services)
- *Disclaimer: Major Players sorted in no particular order


Recent Industry Developments
- June 2025: Palo Alto Networks reported USD 2.29 billion in quarterly revenue and agreed to acquire Protect.ai, enhancing its AI security portfolio and targeting USD 15 billion annual recurring revenue by 2030.
- May 2025: SEALSQ Corp demonstrated Crystal Kyber and Crystal Dilithium post-quantum algorithms at Quantum Days 2025, addressing upcoming quantum computing threats to traditional encryption.
- April 2025: U.S. Department of Justice finalized Data Security Program rules governing telecom and cloud data transfers with countries of concern, elevating compliance complexity for providers.
- March 2025: General Services Administration launched a revamped Federal Risk and Authorization Management Program to accelerate federal cloud security approvals.
- March 2025: National Institute of Standards and Technology released draft SP 800-228, detailing API protection guidance for cloud-native systems.
- February 2025: Alphabet, Microsoft, Meta, and Amazon earmarked USD 215 billion for 2025 cloud infrastructure expansion, enlarging the canvas for native security services.
Research Methodology Framework and Report Scope
Market Definitions and Key Coverage
Our study defines the cloud security software market as the global revenue generated by commercial off-the-shelf software that protects data, applications, and workloads hosted on public, private, and hybrid clouds. It covers identity and access management, cloud access security broker tools, cloud-native application and workload protection, vulnerability and risk management, secure web and email gateways, and SIEM/log management that are delivered in a SaaS or pay-as-you-go model.
Scope Exclusion: Hardware firewalls, stand-alone on-premises security appliances, and pure advisory services are outside the definition.
Segmentation Overview
- By Software
- Cloud IAM
- CASB
- CNAPP / CWPP
- Vulnerability and Risk Management
- Web, Email and DNS Security
- SIEM and Log Management
- By Deployment Mode
- Public Cloud
- Private Cloud
- Hybrid / Multi-Cloud
- By Organization Size
- Large Enterprises
- Small and Medium Enterprises (SMEs)
- By End-User Industry
- BFSI
- IT and Telecom
- Healthcare and Life-Sciences
- Retail and Consumer Goods
- Manufacturing
- Others
- By Geography
- North America
- United States
- Canada
- Mexico
- Europe
- Germany
- United Kingdom
- France
- Italy
- Spain
- Russia
- Rest of Europe
- Asia-Pacific
- China
- Japan
- India
- South Korea
- Australia and New Zealand
- Rest of Asia-Pacific
- South America
- Brazil
- Argentina
- Rest of South America
- Middle East and Africa
- Middle East
- Saudi Arabia
- United Arab Emirates
- Turkey
- Rest of Middle East
- Africa
- South Africa
- Nigeria
- Rest of Africa
- Middle East
- North America
Detailed Research Methodology and Data Validation
Primary Research
Mordor analysts interviewed CISOs at banks, payers in healthcare, and IT leaders within hyperscale cloud partners across North America, Europe, and Asia-Pacific. These discussions validated license prices, typical seat counts, and rollout timelines, and filled gaps on multi-cloud security budgets for small and medium firms.
Desk Research
We began with publicly available benchmarks from NIST, the U.S. Cybersecurity and Infrastructure Security Agency, ENISA, and the OECD to size cloud adoption footprints. Trade bodies such as the Cloud Security Alliance and regional telecom regulators supplied penetration and compliance data, while corporate 10-Ks, investor decks, and trusted news feeds on Dow Jones Factiva clarified vendor revenue splits. D&B Hoovers aided us in mapping segment revenues for listed as well as privately held suppliers. The sources cited are illustrative; many additional documents, customs datasets, and academic papers informed our desk work.
Market-Sizing and Forecasting
A top-down model converted global cloud infrastructure spend into an addressable security software pool using penetration rates that vary by cloud type and industry. Supplier roll-ups and sampled average selling price times user counts were then used as a bottom-up check, with mismatches adjusted after client channel feedback. Key variables like active public-cloud workloads, zero-trust policy adoption, breaches per thousand accounts, average SaaS price erosion, and regulatory deadline calendars drive annual estimates. Forecasts to 2030 rely on multivariate regression blended with scenario analysis when new regulation or macro shocks emerge.
Data Validation and Update Cycle
Outputs pass anomaly checks, peer review, and a final sign-off before publication. We refresh every twelve months and trigger interim updates when mergers, major attacks, or policy shifts materially alter input variables.
Why Mordor's Cloud Security Software Baseline Inspires Confidence
Published values often diverge because firms choose a narrower component mix, convert currencies differently, or apply aggressive cloud workload growth curves.
Key gap drivers for other publishers include counting only 'solution' revenues, treating managed services as part of software, and using single-region surveys that miss Asia's fast uptake, whereas Mordor's model anchors on globally reconciled variables and is refreshed annually.
Benchmark comparison
| Market Size | Anonymized source | Primary gap driver |
|---|---|---|
| USD 50.11 B (2025) | Mordor Intelligence | - |
| USD 40.81 B (2025) | Global Consultancy A | Excludes SIEM and hybrid-cloud licenses |
| USD 36.80 B (2024) | Industry Portal B | Uses vendor revenue only, omits SMB demand |
In sum, the disciplined scope selection, dual-path modeling, and frequent updates executed by Mordor analysts give decision-makers a balanced, replicable baseline they can trust.


Key Questions Answered in the Report
What is the current value of the cloud security software market?
The cloud security software market generates USD 56.83 billion in 2026 and is on track for USD 106.6 billion by 2031 at a 13.42% CAGR.
Which software category holds the largest share?
Cloud Identity and Access Management leads with 34.42% of the cloud security software market share in 2025.
Why is Asia-Pacific the fastest-growing region?
Digital transformation programs, sovereign-cloud mandates, and 5G rollouts propel a 14.32% CAGR, although talent shortages temper momentum.
How are zero-trust mandates influencing demand?
Zero-trust guidelines from NIST emphasize continuous verification, driving investment in identity-centric tools and API protection platforms.
What impact will post-quantum cryptography have on vendors?
Demonstrations such as SEALSQ’s Crystal Kyber highlight future requirements, encouraging providers to embed quantum-resistant algorithms into product roadmaps to safeguard long-term data confidentiality.
How are SMEs adopting advanced cloud security?
Automation, managed services, and simplified interfaces allow SMEs to implement enterprise-grade defenses, fueling a 15.03% CAGR among small and medium enterprises within the cloud security software industry.
Page last updated on: