SECaaS Market Size and Share
SECaaS Market Analysis by Mordor Intelligence
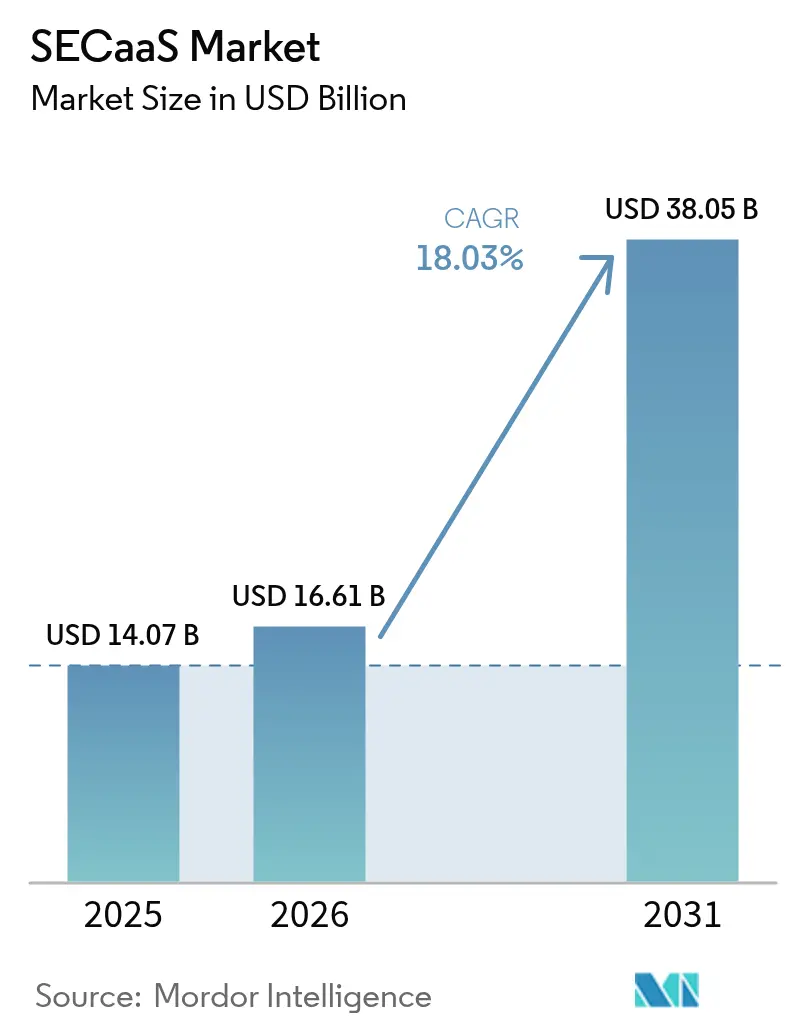
The SECaaS Market size was valued at USD 14.07 billion in 2025 and estimated to grow from USD 16.61 billion in 2026 to reach USD 38.05 billion by 2031, at a CAGR of 18.03% during the forecast period (2026-2031).
Heightened board-level focus on cyber-resilience, the mainstreaming of consumption-based pricing, and the steady migration of workloads to public and hybrid clouds are steering procurement budgets toward cloud-delivered security controls. Organizations replacing appliance-centric defenses with converged Security Service Edge platforms find that the pay-as-you-go model keeps protection levels aligned with actual traffic volumes, a decisive advantage as edge locations proliferate. Demand accelerates further when remote-work policies and the proliferation of cloud-native applications bring identity, device, and API traffic under one policy framework. The SECaaS market now benefits from AI-infused analytics that shorten dwell time and provide full-stack observability, turning threat intelligence into automated, closed-loop response.
Key Report Takeaways
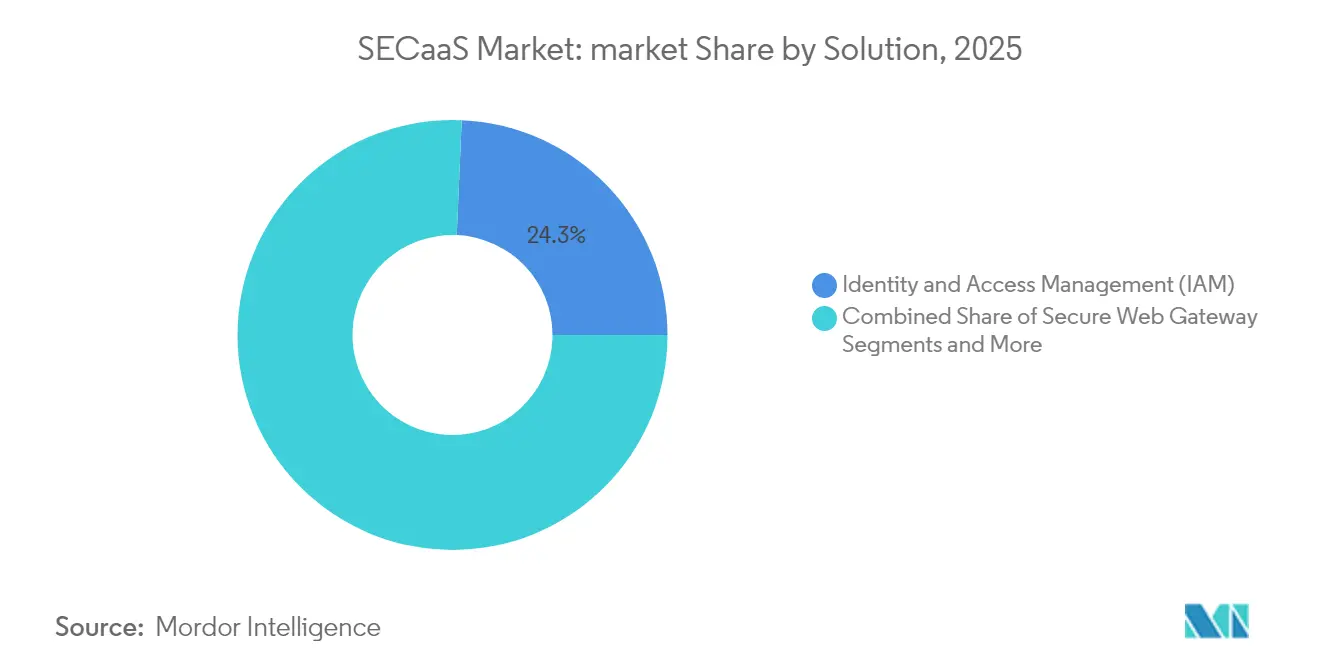
- By solution, Identity and Access Management led with 24.32% of SECaaS market share in 2025, while Cloud Access Security Broker is projected to expand at a 18.67% CAGR through 2031.
- By deployment model, the public-cloud segment accounted for 59.12% revenue share in 2025; hybrid-cloud deployments are growing the fastest at a 19.52% CAGR to 2031.
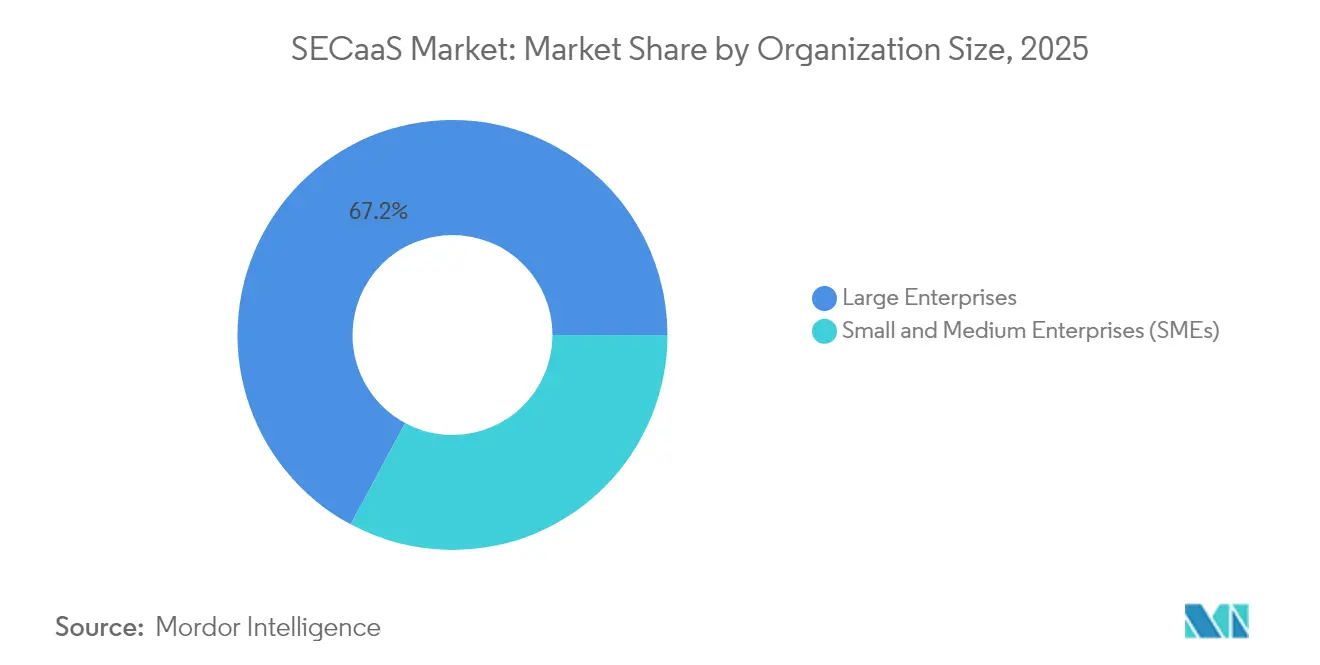
- By organization size, large enterprises held 67.15% of the SECaaS market size in 2025, yet the SME segment is advancing at a 19.86% CAGR through 2031.
- By end-user industry, IT and telecom generated 23.08% revenue share in 2025, whereas the BFSI segment records the highest projected CAGR at 18.55% into 2031.
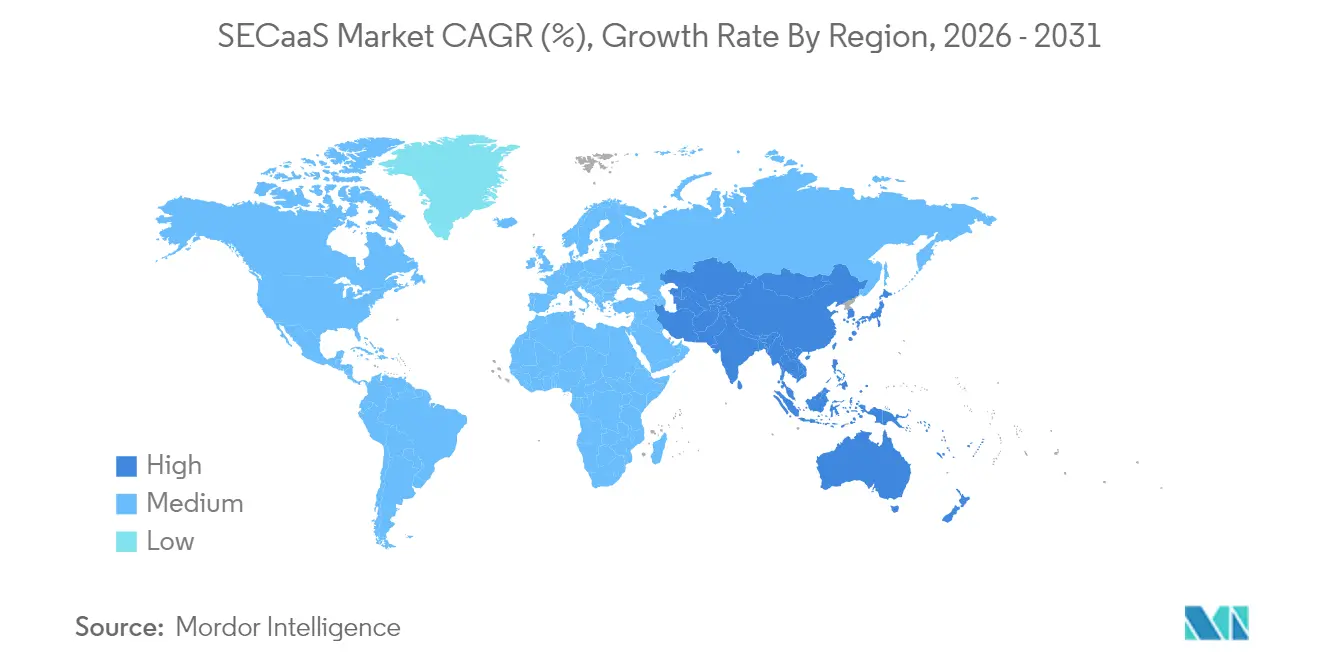
- By geography, North America commanded 36.72% of revenue in 2025; Asia-Pacific is forecast to grow the fastest at a 19.12% CAGR to 2031.
Note: Market size and forecast figures in this report are generated using Mordor Intelligence’s proprietary estimation framework, updated with the latest available data and insights as of 2026.
Global SECaaS Market Trends and Insights
Drivers Impact Analysis*
| Driver | (~) % Impact on CAGR Forecast | Geographic Relevance | Impact Timeline |
|---|---|---|---|
| Surging cloud adoption among SMEs and enterprises | +3.2% | Global with strong APAC uptake | Medium term (2-4 years) |
| Rising sophistication of cyber threats | +2.8% | North America and EU | Short term (≤ 2 years) |
| Shift to remote-work and BYOD environments | +2.1% | North America & EU, expanding in APAC | Medium term (2-4 years) |
| Stringent global data-protection regulations | +1.9% | EU primary, North America secondary | Long term (≥ 4 years) |
| API-driven “security-as-code” demand | +1.7% | North America & EU tech hubs | Medium term (2-4 years) |
| Rapid rollout of zero-trust Security Service Edge | +2.4% | Global, led by enterprises | Short term (≤ 2 years) |
| Source: Mordor Intelligence | |||
Surging Cloud Adoption among SMEs and Enterprises
Growing cloud budgets channel directly into the SECaaS market as firms retire perimeter-centric technologies in favor of identity-first defenses. Public-cloud services in India are forecast to exceed USD 24.2 billion by 2028, with security services advancing the quickest at a 19% CAGR. Small and mid-size businesses gain enterprise-grade protection without dedicated SOC investments, accelerating vendor pipelines for multi-tenant platforms. Financial institutions illustrate the shift: 98% already consume at least one class of cloud service, and most now extend regulated workloads to third-party clouds under tightly governed access policies. Each new workload moved to the cloud automatically expands the attach rate for SECaaS subscriptions, creating a compounding revenue effect across the vendor landscape.
Rising Sophistication of Cyber Threats
Adversaries now wield AI-generated phishing, autonomous malware, and large-scale credential-stuffing campaigns that overwhelm signature-based tools. Banks have responded by embedding machine-learning analytics inside core SOC workflows, dedicating a growing share of multi-year cyber budgets to cloud-native threat detection engines. Healthcare providers, facing a 256% spike in hacking-related breaches, now stipulate SOC 2 and HIPAA alignment as entry requirements for any third-party service. The SECaaS market offers autonomy at scale: threat-intelligence feeds are centralized, detection models are continuously retrained, and automated response actions are orchestrated across global points of presence in seconds.
Shift to Remote-Work and BYOD Environments
Hybrid work dissolves traditional boundaries and exposes VPN limitations, prompting enterprises to adopt zero-trust models delivered via Security Service Edge nodes. Research by Zscaler shows that 81% of enterprises aim to standardize on zero-trust frameworks by 2026, and 65% intend to phase out legacy VPN concentrators[1]Zscaler, “2025 State of Zero Trust Transformation,” zscaler.com . SECaaS vendors provide device-agnostic policy engines that enforce identity, posture, and application context at each access request, ensuring a uniform user experience whether employees are at headquarters or on personal devices. This network-agnostic paradigm cements recurring demand for scalable, cloud-based inspection and policy services.
Stringent Global Data-Protection Regulations
With 137 jurisdictions now enforcing dedicated data-privacy laws, real-time compliance automation is no longer optional. The EU’s GDPR and the forthcoming Digital Operational Resilience Act impose granular audit-trail and reporting mandates that manual processes cannot meet. SECaaS platforms embed privacy controls into runtime policies, auto-generating evidence artifacts for auditors. Continuous compliance shifts governance from periodic checklist exercises to always-on enforcement, making cloud-delivered security controls the fastest route to passing regulatory scrutiny.
Restraints Impact Analysis*
| Restraint | (~) % Impact on CAGR Forecast | Geographic Relevance | Impact Timeline |
|---|---|---|---|
| Data-residency and sovereignty concerns | -1.8% | EU primary, APAC secondary | Long term (≥ 4 years) |
| Multi-vendor subscription-management complexity | -1.4% | Global, large enterprises | Medium term (2-4 years) |
| Latency-sensitive workloads bypassing inline security | -1.1% | Manufacturing & finance | Short term (≤ 2 years) |
| Lack of usage-based billing standards | -0.9% | Global, affects SMEs | Medium term (2-4 years) |
| Source: Mordor Intelligence | |||
Data-Residency and Sovereignty Concerns
Cross-border data-flow restrictions challenge uniform cloud adoption. Europe’s GDPR and impending Digital Operational Resilience Act compel many financial institutions to maintain customer data within regional boundaries, limiting the choice of global cloud locations[2]Cloud Security Alliance, “Cross-Border Data Transfers and Compliance,” cloudsecurityalliance.org. Multi-cloud strategies appear attractive, yet variations in sovereignty controls create fragmented security architectures that duplicate cost. While emerging sovereign-cloud offerings promise localized processing, enterprises remain cautious about potential vendor lock-in.
Multi-Vendor Subscription-Management Complexity
Enterprises routinely juggle half a dozen discrete security-as-a-service contracts covering email security, CASB, SIEM, and vulnerability management. Each vendor pursues its own usage metric and billing cadence, complicating budget forecasting and vendor governance. CSO Online reports that security teams now dedicate as much as 20% of administrative hours to license reconciliation across platforms. Consolidation through acquisitions—such as Sophos absorbing Secureworks—targets this pain point, but organizations tread carefully to avoid single-vendor dependence.
*Our updated forecasts treat driver/restraint impacts as directional, not additive. The revised impact forecasts reflect baseline growth, mix effects, and variable interactions.
Segment Analysis
By Solution: Identity at the Core, CASB in Acceleration
Identity-and-Access Management remains the anchor of the SECaaS market, contributing 24.32% of 2025 revenue as cloud-first architectures elevate identity to the default control plane. The segment’s enduring relevance reflects tighter least-privilege mandates and the explosion of third-party developer accounts. Advanced IAM suites now extend beyond workforce SSO to govern non-human identities generated by container orchestrators, elevating license counts and average revenue per user. Less visible yet faster moving, the Cloud Access Security Broker segment is growing at a 18.67% CAGR, fueled by the need to discover unsanctioned SaaS and enforce data-loss-prevention rules directly in SaaS-to-SaaS traffic. Combined, these solution pillars underpin the transition toward unified Security Service Edge offerings, where in-line inspection, access control, and data classification co-reside on a global edge fabric. Secure Email Gateway and Secure Web Gateway functions are migrating into these converged stacks, while next-generation SIEM refactors ingestion pipelines to exploit hyperscaler object-storage, thus slashing per-terabyte economics and removing deployment friction.
Second-generation vulnerability-management tools, embedded directly into CI/CD pipelines, close feedback loops between code, build, and runtime. This segue ties security posture tightly to developer workflows and allies the SECaaS market with the broader Platform Engineering movement. Vendors now package pre-approved IaC templates, policy-as-code libraries, and pipeline plugins so that risk visibility becomes intrinsic rather than bolted-on. The most effective sales narratives pivot on measurable MTTD reductions, dashboard-driven compliance, and the demonstrable ROI of consolidating five point solutions into one contract.

By Deployment Model: Hybrid Momentum Challenges Public-Cloud Dominance
Public-cloud deployments represented 59.12% of the 2025 SECaaS market as organizations capitalized on turnkey global points of presence and elastic scale. Nevertheless, hybrid-cloud adoption is posting a 19.52% CAGR as regulated entities weigh data-sovereignty mandates against latency and performance criteria. Enterprises now commonly place identity brokers and policy engines in public cloud while running inline decryption nodes on customer-managed infrastructure for sensitive workloads. Such architectural pluralism requires orchestration layers that can propagate policy once and enforce everywhere—capabilities that have become a differentiator in vendor bake-offs.
Private-cloud SECaaS instances persist for defense and critical-infrastructure operators who cannot expose traffic metadata to shared environments. Emerging industry blueprints allow controlled synchronization of indicators of compromise across trust domains without violating data-residency rules, an approach pioneered by industrial-control vendors working with national CERTs. Over the forecast horizon, multi-cloud policy automation will become table stakes, catalyzing alliances between cloud platforms and security vendors aimed at streamlining identity federation, key management, and telemetry normalization.
By Organization Size: SMEs Narrow the Protection Gap
Large enterprises captured 67.15% of the SECaaS market size in 2025, buoyed by multi-year transformation programs, in-house SOC personnel, and cross-border infrastructure footprints that mandate globally distributed inspection points. They continue to prioritize vendor consolidation and AI-driven automation to offset shortages in tier-1 analysts. Meanwhile, small- and mid-size enterprises register a 19.86% CAGR, a clear signal that simplified onboarding and usage-based pricing are democratizing advanced security. Vendors catering to this cohort lead with zero-touch deployment, built-in best-practice defaults, and exportable compliance reports designed for insurance underwriters.
The insurance sector itself has become a channel for SECaaS adoption. Hybrid products that bundle breach insurance with ongoing monitoring—exemplified by DUAL Europe’s Cyber Active Protect solution—translate risk mitigation into lower premiums, effectively subsidizing the security subscription. As underwriters tighten payout conditions, SME adoption curves steepen; vendors able to provide insurer-approved controls enjoy reduced customer-acquisition costs and higher renewal rates.

By End-User Industry: BFSI Growth Outpaces Traditional Leaders
IT and telecom providers were first movers into cloud-native architectures and, consequently, continue to generate 23.08% of 2025 revenue. Yet the Banking, Financial Services, and Insurance vertical is projected to grow the fastest, posting an 18.55% CAGR as regulatory frameworks evolve toward zero-trust baselines. BFSI buyers increasingly demand certified cryptographic modules, automated key rotation, and near-real-time compliance evidence. Vendors responding with integrated secrets management and continuous control validation secure multi-year framework agreements with global banks.
Healthcare and life-sciences organizations, under siege from ransomware, prioritize managed detection and response delivered entirely as a service. Government and defense buyers place sovereignty and supply-chain transparency at the top of RFP scoring, reserving workloads for platforms audited under FedRAMP High or equivalent schemes. Retailers and manufacturers push for inline tokenization and operational-technology anomaly detection, respectively, merging IT and OT telemetry in unified data lakes that feed AI analytics.
Geography Analysis
North America retained 36.72% of global revenue in 2025, reflecting its concentration of hyperscalers, cybersecurity innovators, and early-adopter enterprises. Federal guidance from CISA urging the sunset of legacy VPN tunnels in favor of zero-trust, cloud-native access further cements demand. Financial institutions now mandate Security Service Edge controls during third-party due-diligence reviews, reinforcing network effects across supply chains. Canada and Mexico ride this momentum, integrating regional data-protection statutes with cross-border data flows to spur platform expansion.
Asia-Pacific is advancing at a 19.12% CAGR to 2031 as cloud-migration roadmaps underpin national digital-economy targets. India’s public-cloud revenues already rank among the world’s fastest-growing, and Australia’s IRAP framework has opened government procurement channels for certified providers. Japan’s telecom operators spearhead 5G edge rollouts, prompting industrial clients to pre-provision inline inspection to remote factories. Localized data regulations are diverse, but providers that can demonstrate consistent, region-aware encryption-key management gain a decisive bidding advantage.
Europe maintains robust demand, driven by GDPR and the emerging Digital Operational Resilience Act that obliges real-time control validation for financial entities. Germany and the United Kingdom lead investments in converged platforms that unify cloud access, email security, and data-loss prevention. France and Italy accelerate procurement through national cyber-resilience plans that allocate co-funding for SME adoption. Elsewhere, South America and the Middle East and Africa are earlier in their cloud journeys yet rapidly expanding internet backbones and regulatory frameworks, setting the stage for elevated SECaaS penetration rates as economic conditions stabilize.
Competitive Landscape
The SECaaS market shows moderate consolidation as hyperscalers, legacy firewall vendors, and pure-play cloud-security specialists race to assemble full-stack platforms. Google’s USD 32 billion purchase of Wiz augments its cloud portfolio with agentless workload scanning and deep runtime visibility, mirroring CyberArk’s USD 1.54 billion acquisition of Venafi that fuses machine-identity management with human IAM workloads. Such landmark transactions underscore buyer preference for integrated control planes over best-of-breed mosaics.
Product strategies pivot sharply toward generative-AI enablement. Zscaler’s collaboration with NVIDIA delivers real-time language translation of threat telemetry into actionable remediation steps. Palo Alto Networks shattered previous marketplace records by surpassing USD 1.5 billion in sales through Google Cloud Marketplace, proving that co-selling motions shorten enterprise procurement cycles. Startup investments gravitate toward niche capabilities such as AI-native data-leak protection and post-quantum cryptography. Tenable’s acquisition of Apex Security folds AI-based activity-risk scoring directly into its vulnerability-management fabric, confirming that analytics differentiation remains acquisition-driven.
Channel dynamics evolve as managed-service providers embed SECaaS modules into broader digital-transformation offerings. Fortinet’s ASIC-driven next-generation firewalls deliver up to 11x higher IPsec throughput, a performance edge that resonates in latency-sensitive verticals. NTT DATA’s expanded partnership with Rubrik blends backup resilience with ransomware-aware automation, illustrating how data-protection and security silos converge. Strategic positioning now hinges on delivering measurable resilience outcomes—mean-time-to-recover, policy drift eradication, and regulatory evidence generation—rather than merely enumerating feature matrices.
SECaaS Industry Leaders
IBM Corporation
Cisco Systems Inc.
Amazon Web Services
Google Cloud
Microsoft
- *Disclaimer: Major Players sorted in no particular order


Recent Industry Developments
- March 2022: Google closed its USD 32 billion acquisition of Wiz, instantly bolstering Google Cloud’s threat-detection and posture-management capabilities.
- March 2025: NTT DATA broadened its alliance with Rubrik, offering Fortune 500 clients ransomware recovery and cyber-resilience managed services.
- February 2025: Fortinet unveiled FortiGate G-series firewalls featuring proprietary ASICs and AI security services that raise IPsec VPN throughput to 11x industry averages.
- January 2025: Cognizant partnered with CrowdStrike to integrate Falcon Next-Gen SIEM and Falcon Cloud Security into its cloud-migration engagements.
Global SECaaS Market Report Scope
In Security-as-a-Service (SECaaS) model, a service provider integrates their security services into the business infrastructure on a subscription basis more cost-effectively than most individuals or corporations can provide on their own.
The Security-as-a-Service (SECaaS) Market is segmented by solution (identity and access management, secure email gateway, secure web gateway, vulnerability management, Security Information and Event Management (SIEM), application security testing, and other solutions), organization size (small and medium enterprises, large enterprises), and geography (North America, Europe, Asia-Pacific, Latin America, Middle East & Africa).
The market sizes and forecasts are in terms of value (USD million) for all the above segments.
| Identity and Access Management (IAM) |
| Secure Email Gateway |
| Secure Web Gateway |
| Cloud Access Security Broker (CASB) |
| Security Information and Event Management (SIEM) |
| Vulnerability Management |
| Other Solutions |
| Public Cloud |
| Private Cloud |
| Hybrid Cloud |
| Large Enterprises |
| Small and Medium Enterprises (SMEs) |
| BFSI |
| IT and Telecom |
| Healthcare and Life Sciences |
| Government and Defense |
| Retail and E-commerce |
| Manufacturing |
| Others |
| North America | United States | |
| Canada | ||
| Mexico | ||
| Europe | Germany | |
| United Kingdom | ||
| France | ||
| Italy | ||
| Spain | ||
| Rest of Europe | ||
| Asia-Pacific | China | |
| Japan | ||
| India | ||
| South Korea | ||
| Australia | ||
| Rest of Asia-Pacific | ||
| South America | Brazil | |
| Argentina | ||
| Rest of South America | ||
| Middle East and Africa | Middle East | Saudi Arabia |
| United Arab Emirates | ||
| Turkey | ||
| Rest of Middle East | ||
| Africa | South Africa | |
| Egypt | ||
| Nigeria | ||
| Rest of Africa | ||
| By Solution | Identity and Access Management (IAM) | ||
| Secure Email Gateway | |||
| Secure Web Gateway | |||
| Cloud Access Security Broker (CASB) | |||
| Security Information and Event Management (SIEM) | |||
| Vulnerability Management | |||
| Other Solutions | |||
| By Deployment Model | Public Cloud | ||
| Private Cloud | |||
| Hybrid Cloud | |||
| By Organization Size | Large Enterprises | ||
| Small and Medium Enterprises (SMEs) | |||
| By End-User Industry | BFSI | ||
| IT and Telecom | |||
| Healthcare and Life Sciences | |||
| Government and Defense | |||
| Retail and E-commerce | |||
| Manufacturing | |||
| Others | |||
| By Geography | North America | United States | |
| Canada | |||
| Mexico | |||
| Europe | Germany | ||
| United Kingdom | |||
| France | |||
| Italy | |||
| Spain | |||
| Rest of Europe | |||
| Asia-Pacific | China | ||
| Japan | |||
| India | |||
| South Korea | |||
| Australia | |||
| Rest of Asia-Pacific | |||
| South America | Brazil | ||
| Argentina | |||
| Rest of South America | |||
| Middle East and Africa | Middle East | Saudi Arabia | |
| United Arab Emirates | |||
| Turkey | |||
| Rest of Middle East | |||
| Africa | South Africa | ||
| Egypt | |||
| Nigeria | |||
| Rest of Africa | |||


Key Questions Answered in the Report
What is the current value of the SECaaS market?
The SECaaS market size is USD 16.61 billion in 2026 and is forecast to reach USD 38.05 billion by 2031.
Which solution segment holds the largest share?
Identity and Access Management leads with 24.32% of SECaaS market share in 2025.
Which deployment model is growing the fastest?
Hybrid-cloud SECaaS deployments are expanding at a 19.52% CAGR through 2031.
Why is the BFSI sector a high-growth adopter?
Rising regulatory mandates and zero-trust initiatives push BFSI organizations to embrace SECaaS platforms, resulting in an 18.55% projected CAGR to 2031.
What geographic region is expected to post the highest growth rate?
Asia-Pacific is forecast to grow at a 19.12% CAGR, propelled by aggressive cloud-migration programs and evolving data-protection laws.
How does zero-trust architecture influence SECaaS demand?
Zero-trust frameworks require identity-centric controls delivered at the edge, making cloud-native Security Service Edge platforms the most efficient delivery mechanism and accelerating overall SECaaS market adoption.
Page last updated on: