India Network Security And Cyber Risk Management Market Size and Share
India Network Security And Cyber Risk Management Market Analysis by Mordor Intelligence
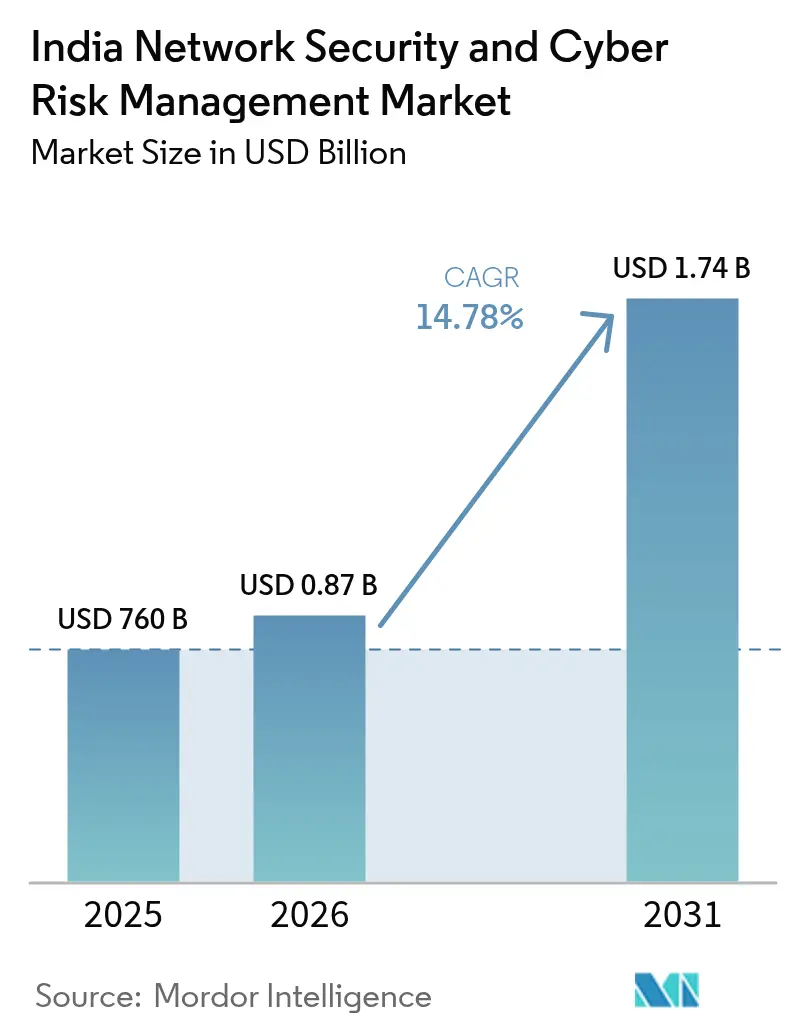
The India network security and cyber risk management market size is expected to grow from USD 760 million in 2025 to USD 872.3 million in 2026 and is forecast to reach USD 1.74 billion by 2031 at 14.78% CAGR over 2026-2031. Ongoing digital transformation, tighter privacy regulations, and a rise in sophisticated cyber incidents anchor this expansion. Breach-reporting rules that compel notification within six hours spur investments in real-time monitoring, while the Digital Personal Data Protection Act (DPDP 2023) drives heavy penalties for non-compliance, encouraging proactive security adoption. Accelerating cloud adoption among micro, small, and medium enterprises (MSMEs) expands attack surfaces and elevates demand for managed detection and response services. Parallel rollouts of private 5G networks across manufacturing corridors introduce new operational-technology risks that push organizations toward integrated, zero-trust architectures. Finally, a severe shortage of skilled cyber talent propels outsourcing to managed service providers and automation-led solutions, reshaping competitive dynamics across the India network security and cyber risk management market.
Key Report Takeaways
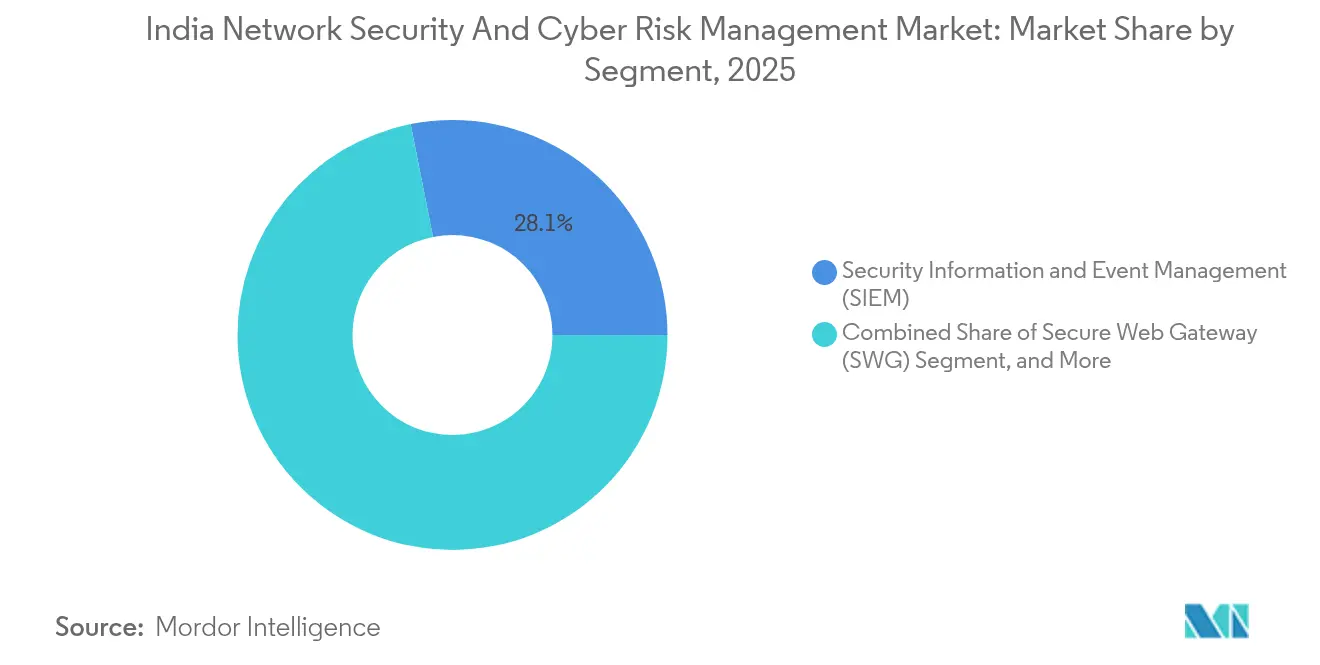
- By segment, Security Information and Event Management (SIEM) held 28.12% of the India network security and cyber risk management market share in 2025; Identity Governance and Administration (IGA) is projected to expand at a 17.18% CAGR to 2031.
- By solution, Identity and Access Management captured a 31.05% share of the India network security and cyber risk management market size in 2025, while Zero Trust Network Access is advancing at an 18.05% CAGR through 2031.
- By service, Network Security accounted for 34.12% of the India network security and cyber risk management market size in 2025; Cloud Security is forecast to register a 20.62% CAGR to 2031.
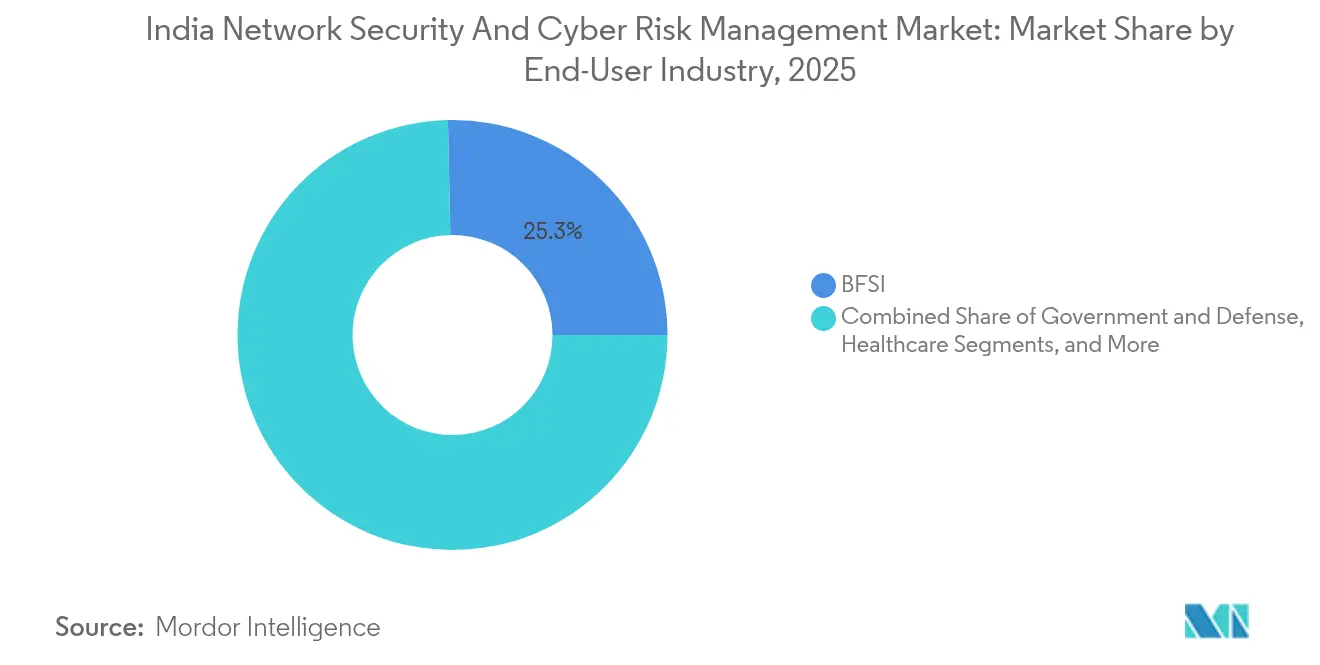
- By end-user industry, the BFSI segment commanded 25.34% revenue share in 2025, while Healthcare is advancing at the highest projected CAGR at 19.62% through 2031.
- By deployment mode, on-premises models led with 55.92% share of the India network security and cyber risk management market size in 2025, whereas cloud-based deployments are growing at a 20.14% CAGR between 2026-2031.
Note: Market size and forecast figures in this report are generated using Mordor Intelligence’s proprietary estimation framework, updated with the latest available data and insights as of 2026.
India Network Security And Cyber Risk Management Market Trends and Insights
Drivers Impact Analysis*
| Driver | (~) % Impact on CAGR Forecast | Geographic Relevance | Impact Timeline |
|---|---|---|---|
| FinTech transaction-sprawl intensifying attack surface | +2.8% | National, with concentration in Mumbai, Bengaluru, Delhi NCR | Short term (≤ 2 years) |
| Zero-day supply-chain exploits on Indian OEM firmware | +2.1% | National, with higher exposure in manufacturing hubs | Medium term (2-4 years) |
| Mandatory CERT-In six-hour breach-reporting rule | +3.2% | National | Short term (≤ 2 years) |
| Rising cloud-native adoption among MSMEs | +2.5% | Tier-II and Tier-III cities, with spillover to metro areas | Medium term (2-4 years) |
| 5G private‐network rollouts in smart-manufacturing hubs | +1.9% | Gujarat, Tamil Nadu, and Maharashtra industrial corridors | Long term (≥ 4 years) |
| Generative-AI-driven phishing and deep-fake prevention spend | +2.5% | National, with early adoption in the BFSI and Healthcare sectors | Short term (≤ 2 years) |
| Source: Mordor Intelligence | |||
FinTech Transaction-Sprawl Intensifying Attack Surface
Indian FinTech platforms recorded 429,847 cyber incidents in 2023, with exploits frequently targeting open APIs and third-party integrations that multiply entry points for attackers. The Aditya Birla Capital breach, which siphoned USD 0.23 million in digital gold, illustrates cascading risks created by interconnected service providers. Compliance with DPDP 2023 demands encryption, audit trails and breach notification, pushing FinTechs toward advanced SIEM platforms with AI-based anomaly detection. Competitive pressures encourage rapid feature releases, yet every new integration widens the attack surface. Consequently, chief information security officers prioritize continuous monitoring, micro-segmentation and identity-centric controls to protect customer transactions and sustain trust across the India network security and cyber risk management market.
Zero-Day Supply-Chain Exploits on Indian OEM Firmware
CERT-In has flagged multiple critical vulnerabilities in local OEM firmware, including Samsung devices running Android 11-14, enabling arbitrary code execution and sensitive-data exfiltration [1]CERT-In, “Multiple Vulnerabilities in Samsung Products,” cert-in.org.in. A 2024 ransomware campaign against Indian banks leveraged CVE-2024-23897 embedded in Jenkins servers to breach payment gateways, underscoring how firmware flaws propagate across supply chains [2]Juniper Threat Labs, “How CVE-2024-23897 Enabled Ransomware Attack on Indian Banks,” juniper.net. Proliferation of Industry 4.0 devices magnifies this exposure, especially in export-oriented manufacturing hubs. Enterprises, therefore, embed firmware-integrity checks, vendor-audit scorecards, and continuous vulnerability scanning in procurement workflows. Tightening supply-chain security raises demand for endpoint detection and response tools integrated with SIEM and SOAR platforms, reinforcing growth in the India network security and cyber risk management market.
Mandatory CERT-In Six-Hour Breach-Reporting Rule
The six-hour incident-reporting mandate enforces clock synchronization, 180-day log retention, and designation of a CERT-In liaison across all sectors. Non-compliance invites stiff fines and possible imprisonment, prompting urgent upgrades to logging, threat-detection, and automated response capabilities. Organizations now treat breach-reporting readiness as a board-level objective that affects brand equity. Demand surges for managed detection services able to contain threats and assemble compliant incident reports within statutory windows. Vendors differentiate through out-of-the-box compliance templates and machine-learning analytics that reduce mean-time-to-detect, further accelerating the India network security and cyber risk management market.
Rising Cloud-Native Adoption Among MSMEs
Government incentives and affordable SaaS tools have spurred a surge in cloud adoption, with 35% of MSMEs running critical workloads on public clouds by 2025. While cloud helps firms scale rapidly, resource constraints limit dedicated security teams. Cloud-native attacks such as misconfigured storage buckets and compromised access keys now rank among the top breach vectors. MSPs step in with bundled Cloud Security Posture Management and Zero-Trust Network Access offerings tailored to MSME budgets. Community-training programs foster basic cyber hygiene, but automated policy enforcement remains the game-changer for securing India’s distributed business landscape and sustaining momentum in the India network security and cyber risk management market.
Restraints Impact Analysis*
| Restraint | (~) % Impact on CAGR Forecast | Geographic Relevance | Impact Timeline |
|---|---|---|---|
| Shortage of 400k skilled cyber-security professionals | -1.8% | National, acute in Tier-II cities | Long term (≥ 4 years) |
| Fragmented state-level data-protection enforcement | -1.2% | Varies by state regulatory maturity | Medium term (2-4 years) |
| High TCO of zero-trust architectures for SMEs | -1.5% | MSME-concentrated regions across India | Medium term (2-4 years) |
| Legacy OT systems in critical infrastructure | -1.1% | Power generation hubs, manufacturing belts | Long term (≥ 4 years) |
| Source: Mordor Intelligence | |||
Shortage of 400k Skilled Cyber-Security Professionals
India requires 1 million cybersecurity professionals by 2027, yet only 300,000 people currently possess employable skills, creating a 400,000-person gap. BFSI alone accounts for half of this unmet demand, which raises labor costs and stretches internal teams [3]Economic Times Commentary, “India’s Skill Gap Crisis,” economictimes.indiatimes.com. Organizations increasingly outsource to Managed Detection and Response providers and deploy AI-based automation to compensate for missing talent. Government initiatives like Microsoft’s CyberShikshaa upskill underrepresented groups, yet annual output remains below market needs. Skills scarcity thereby slows implementation of sophisticated architectures such as zero-trust among small and mid-size enterprises, tempering the growth trajectory of the India network security and cyber risk management market.
Fragmented State-Level Data-Protection Enforcement
Although the DPDP 2023 establishes federal privacy norms, enforcement remains uneven across India’s states, leading to differing compliance deadlines and inconsistent audit criteria. Enterprises operating nationwide face overlapping mandates and duplicative reporting, driving up compliance costs. Smaller firms struggle with the legal complexity and risk of project delays as they await detailed state-level guidelines. The anticipated Data Protection Board may harmonize enforcement by 2025-end, yet the current patchwork hinders seamless data flows and slows procurement decisions for security solutions. Vendors respond by embedding compliance management dashboards that map security controls to multiple regulatory frameworks, a feature now viewed as critical in vendor evaluations across the India network security and cyber risk management market.
*Our updated forecasts treat driver/restraint impacts as directional, not additive. The revised impact forecasts reflect baseline growth, mix effects, and variable interactions.
Segment Analysis
By Segment: SIEM Remains Core While IGA Accelerates
The SIEM segment generated 28.12% of the India network security and cyber risk management market size in 2025, reflecting organizations’ need for centralized log analytics and automated alerts that satisfy CERT-In mandates. Large enterprises integrate SIEM with SOAR to orchestrate playbooks, reducing response times and audit overhead. Mid-sized firms prefer cloud-hosted SIEM subscriptions to avoid capital expenditure. Meanwhile, IGA solutions compound at a 17.18% CAGR as identity becomes the new perimeter in hybrid workplaces. Automated provisioning and risk-based access reviews improve user-lifecycle efficiency and compliance reporting.
Growth in both segments stems from demand for unified visibility in multi-cloud environments. Vendors embed machine-learning models for anomaly detection, while marketplace integrations pull telemetry from SaaS, container and IoT layers. As digital supply chains deepen, customers favor platforms that combine SIEM, XDR and identity governance, signaling a shift toward converged security operations that will redefine the India network security and cyber risk management market.

By Solution: IAM Holds Lead, ZTNA Gains Momentum
Identity and Access Management retained a 31.05% share of the India network security and cyber risk management market in 2025, anchoring everything from privileged-access controls to single sign-on. Regulatory clauses requiring granular access logs further entrench IAM platforms. Yet Zero Trust Network Access posts the fastest 18.05% CAGR, propelled by remote-work policies and 5G edge connectivity. ZTNA replaces perimeter-based VPNs with continuous verification, micro-segmentation, and contextual policies.
Encryption and DLP gain traction as enterprises prepare for post-quantum threats and DPDP compliance, respectively. Buyers increasingly adopt solution suites that integrate IAM, ZTNA, and encryption under unified policy engines. This convergence reduces operational overhead and accelerates adoption among MSMEs, expanding revenue opportunities across the India network security and cyber risk management market.
By Service: Network Security Foundational, Cloud Security Surging
Network Security services contributed 34.12% of the India network security and cyber risk management market size in 2025, reflecting demand for firewalls, IDS/IPS, and segmentation across data centers and branch networks. However, Cloud Security services are climbing at a 20.62% CAGR as enterprises pursue multi-cloud strategies. Cloud Access Security Brokers, container-security plugins, and serverless-function scanning become mainstream purchase criteria.
Managed Detection and Response fills talent gaps with 24/7 threat hunting valued by sectors facing advanced persistent threats. Wireless and endpoint security round out service portfolios, addressing 5G private networks and IoT proliferation. Providers bundle offerings to deliver outcome-based pricing, reinforcing the shift toward opex models in the India network security and cyber risk management market.
By End-User Industry: BFSI Leads, Healthcare Rising
BFSI accounted for 25.34% of revenue in 2025, driven by high-value digital transactions and stringent RBI technology guidelines. Threat actors target payment APIs, driving heavy spending on fraud analytics and tokenization. Healthcare, benefiting from telemedicine expansion, projects a 19.62% CAGR as ransomware actors exploit legacy hospital infrastructure and sensitive patient data.
Government and defense sustain steady investments to safeguard citizen services, while IT-telecom anchor consumption of cloud and 5G-edge security controls. Manufacturing firms, once focused on perimeter defense, now adopt OT-security gateways following high-profile plant disruptions. These dynamics collectively strengthen diversification across the India network security and cyber risk management market.

By Deployment Mode: On-Premise Still Dominant, Cloud Gains
On-premise deployments represented 55.92% of the India network security and cyber risk management market share in 2025 as regulated industries prefer data-center control. Financial institutions and healthcare providers often maintain in-house hardware for auditability and latency consistency. Cloud-based deployments, however, climb at 20.14% CAGR due to MSME adoption, elastic scalability and pay-as-you-grow billing.
Hybrid architectures become the norm, using on-premise appliances for core applications and SaaS security for customer-facing workloads. Vendors deliver policy orchestration layers that synchronize controls across Kubernetes, virtual machines and physical networks, supporting seamless expansion of the India network security and cyber risk management market.
Geography Analysis
Metropolitan hubs, Mumbai, Bengaluru, Delhi NCR, and Chennai, account for roughly 59.40% of spending thanks to dense clusters of banks, IT services, and startups that foster rapid technology uptake. These cities boast skilled talent pools and mature digital infrastructure, encouraging early adoption of XDR platforms, AI-powered analytics, and post-quantum encryption pilots. Vendor presence and channel ecosystems are deepest here, easing proof-of-concept deployment and accelerating upgrade cycles across the India network security and cyber risk management market.
Tier-II and Tier-III cities such as Jaipur, Coimbatore, and Kochi register a faster 17-19% CAGR as MSMEs digitize operations. Government Digital India initiatives subsidize broadband, while local incubators drive SaaS innovation that embeds security-by-design principles. Cloud-first strategies dominate in these regions because capital expenditure budgets remain tight, increasing reliance on managed services that bundle compliance support alongside threat defense.
Industrial corridors in Gujarat, Tamil Nadu, and Maharashtra emerge as cybersecurity hotspots owing to private 5G roll-outs that connect smart factories. Edge computing nodes located near production lines introduce novel attack vectors, pressing manufacturers to adopt OT-specific intrusion-prevention systems. State governments collaborate with academia on cyber-range facilities, improving workforce readiness and fostering local vendor ecosystems that fuel growth in the India network security and cyber risk management market.
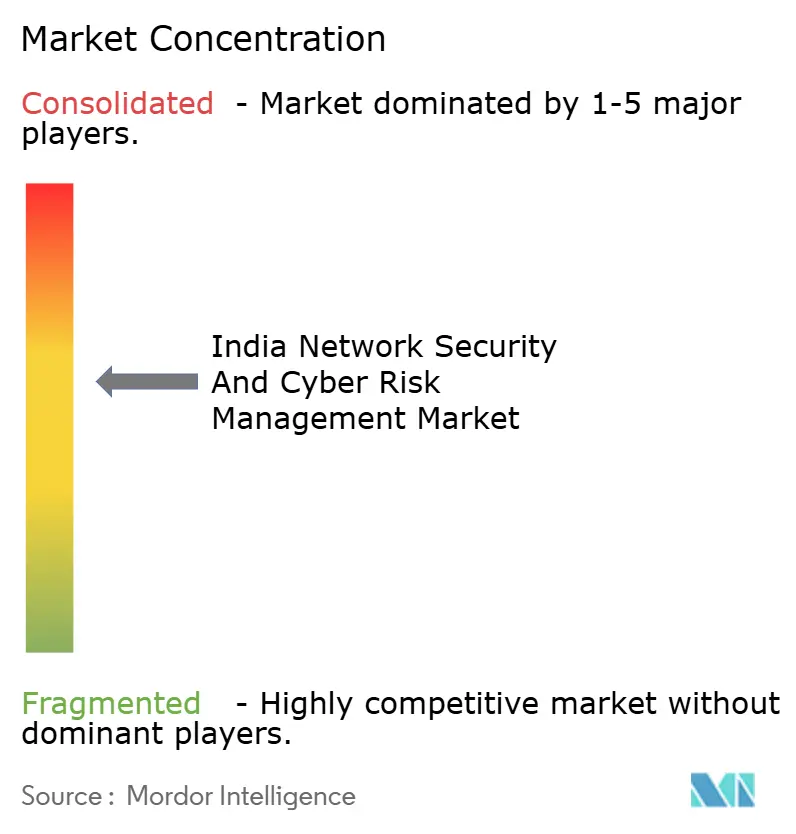
Competitive Landscape
The market remains moderately fragmented, with global majors—Cisco, Palo Alto Networks, and IBM—holding sizeable mindshare while domestic vendors innovate around price-performance. Consolidation intensified in 2023 as strategic buyers closed 396 cybersecurity M&A deals worldwide. SentinelOne’s USD 100 million purchase of Bangalore-based PingSafe gave the acquirer a cloud-native attack-surface management suite tailored for Indian developers [4]Business Standard Reporters, “SentinelOne Acquires PingSafe,” business-standard.com.
Strategic alliances reshape service delivery. Palo Alto Networks acquired IBM’s QRadar cloud assets and trained 1,000 IBM consultants on its platform to penetrate regulated verticals. Indigenous firms face profitability pressures; Quick Heal’s 67% profit slide in 2024 spurred a pivot to AI-based anti-fraud solutions. Yet local providers retain an edge in public-sector deals that require data-sovereignty assurances.
Product roadmaps converge on platformization. Vendors bundle SIEM, SOAR, and XDR within single subscriptions, advertising a lower total cost of ownership for stretched security teams. Post-quantum cryptography support emerges as a differentiator after the government released its quantum-safe roadmap [5]DD News Service, “India Releases Quantum-Safe Roadmap,” ddnews.gov.in. AI-driven threat-hunting features, multilingual dashboards, and pay-as-you-use pricing keep competition vibrant, sustaining healthy buyer bargaining power across the India network security and cyber risk management market.
India Network Security And Cyber Risk Management Industry Leaders
Cisco Systems Inc.
Palo Alto Networks Inc.
IBM Corporation
Check Point Software Technologies Ltd.
Trend Micro Inc.
- *Disclaimer: Major Players sorted in no particular order


Recent Industry Developments
- July 2025: India issued a national quantum-safe cybersecurity roadmap to guide enterprises on post-quantum cryptography transitions.
- June 2025: Aditya Birla Capital disclosed a breach that affected 435 customers and led to USD 0.23 million losses, spurring sector-wide API audits.
- April 2025: IBM opened a Lucknow software lab focusing on generative-AI security applications.
- April 2025: Jio Business expanded private 5G services for manufacturers, embedding industrial-grade security features.
India Network Security And Cyber Risk Management Market Report Scope
The Network Security and Cyber Risk Management market, once known to be a concern only for the IT and Banking industry, has now penetrated every vertical as a serious threat to any business or organization. Awareness and preparedness of these cyber risks have become a priority for consumers, suppliers, and manufacturers. While every sector is fast embracing the 'Internet of Things,' they are forced to challenge the existence of cyber threats, risks, and malware; there is thus an increase in focus among regulators.
The Network Security and Cyber Risk Management Market in India can be segmented by Segment (Security Information and Event Management (SIEM), Security Web Gateway (SWG), Identity Governance and Administration (IGA), Enterprise Content-Aware Data Loss Prevention (DLP)), Solution (Encryption, Identity and Access Management (IAM), Data Loss Protection (DLP), Intrusion Detection System/Intrusion Prevention System (IDS/IPS), Other solutions), Service (Network Security, Endpoint Security, Wireless Security, Cloud Security, Other Services), End-user Vertical (Aerospace and Defense, Retail, Government, Healthcare, It & Telecom, BFSI). The market sizes and forecasts are provided in terms of value (USD) for all the above segments.
| Security Information and Event Management (SIEM) |
| Secure Web Gateway (SWG) |
| Identity Governance and Administration (IGA) |
| Enterprise Content-Aware Data Loss Prevention (DLP) |
| Encryption |
| Identity and Access Management (IAM) |
| Data Loss Protection (DLP) |
| Intrusion Detection/Prevention (IDS/IPS) |
| Zero-Trust Network Access (ZTNA) |
| Network Security |
| Endpoint Security |
| Wireless Security |
| Cloud Security |
| Managed Detection and Response (MDR) |
| BFSI |
| Government and Defence |
| Healthcare |
| IT and Telecom |
| Retail and E-Commerce |
| Manufacturing |
| On-premise |
| Cloud-based |
| By Segment | Security Information and Event Management (SIEM) |
| Secure Web Gateway (SWG) | |
| Identity Governance and Administration (IGA) | |
| Enterprise Content-Aware Data Loss Prevention (DLP) | |
| By Solution | Encryption |
| Identity and Access Management (IAM) | |
| Data Loss Protection (DLP) | |
| Intrusion Detection/Prevention (IDS/IPS) | |
| Zero-Trust Network Access (ZTNA) | |
| By Service | Network Security |
| Endpoint Security | |
| Wireless Security | |
| Cloud Security | |
| Managed Detection and Response (MDR) | |
| By End-user Industry | BFSI |
| Government and Defence | |
| Healthcare | |
| IT and Telecom | |
| Retail and E-Commerce | |
| Manufacturing | |
| By Deployment Mode | On-premise |
| Cloud-based |


Key Questions Answered in the Report
Which segment currently generates the highest revenue?
Security Information and Event Management accounts for 28.12% of revenue as of 2025.
Why is Zero Trust Network Access adoption accelerating?
Hybrid work models and limitations of legacy VPNs drive ZTNA’s 18.05% CAGR through 2031.
How are private 5G roll-outs influencing cybersecurity spending?
Factory-focused 5G networks create new OT threat vectors, prompting investment in specialized intrusion-prevention and segmentation controls.
What factor most constrains market growth?
A shortage of 400 k qualified cybersecurity professionals hampers advanced technology deployment.
Page last updated on: