Middle East Cyber Security Market Size
Middle East Cyber Security Market Analysis
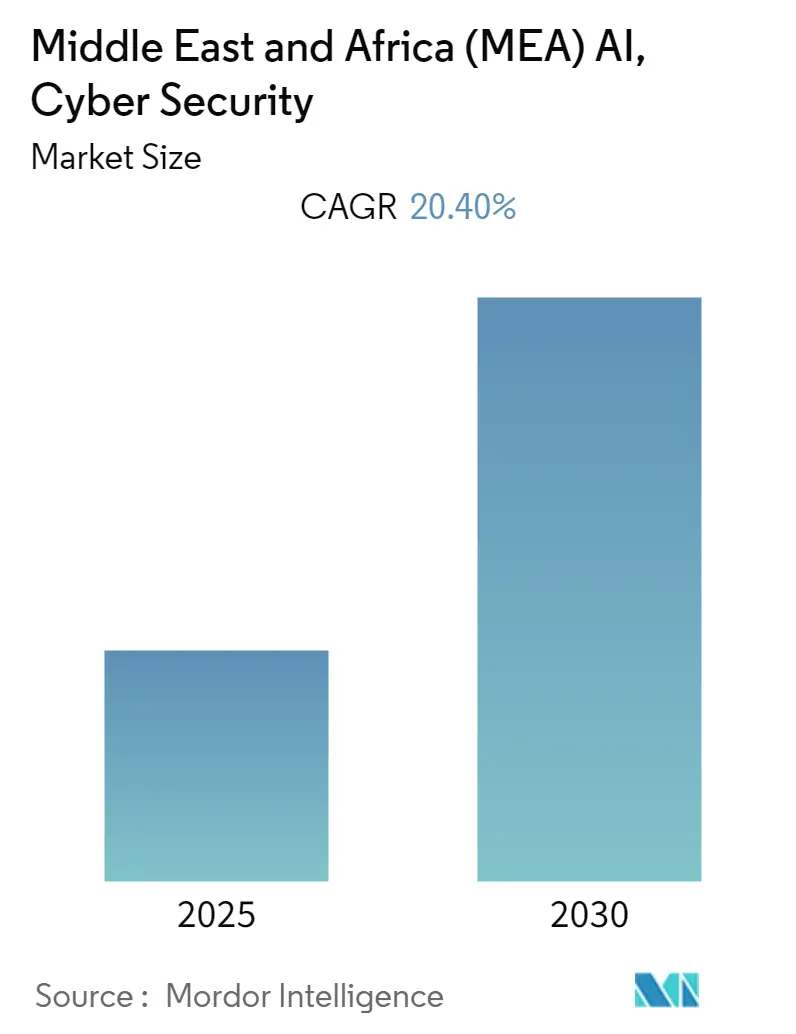
The Middle East & Africa AI, Cyber Security & Big Data Analytics Market is expected to register a CAGR of 20.4% during the forecast period.
- Enterprises in the end-user industries are increasingly deploying AI to realize cost benefits, increase productivity, and improve their safety standards. Several government-driven initiatives are changing the dynamics of the industrial sector, reshaping the landscape in critical economies within the Middle East & African region, and creating more robust institutional set-up and practical regulatory frameworks to promote private sector investments.
- Moreover, regional governments have conducted long-term plans to use AI and ML as an economic stimulus or enhance workforce efficiency and government structure agility. Now, AI programs are carried out with the government's direct support. The UAE government is the first country in the Middle East region to launch its AI strategy and the first in the world to create a Ministry of Artificial Intelligence. The government also planned to invest in AI technologies in about nine sectors.
- Further, in the Middle East & African region, a country like Saudi Arabia plays a significant role in creating an AI-friendly ecosystem with high-speed broadband and 5G deployment, data access, and security. For instance, in the 1st quarter of the current year, The CITC (Communications and Information Technology Commission) of Saudi Arabia moved on with its fifth-generation (5G) technology deployment plan. In collaboration with the UK business Stratospheric Platforms Limited, The CITC tested the High-Altitude Platform System, which delivers 5G network coverage from the stratosphere.
- However, the surge in the overall operational challenges due to the lack of supporting infrastructure in the Middle East & African region might be a factor that could overall restrain the market's growth throughout the forecast period.
- With COVID-19 becoming the new reality, organizations worldwide must respond proactively to cyber threats that have witnessed a spike during the pandemic. For this reason, cyber resilience, which refers to a sector or organization's ability to respond to, prepare for, and recover from cyberattacks, has become an absolute necessity rather than a mere option in the current scenario. Moreover, over the past few decades, various crucial initiatives to enhance online privacy and security for consumers and companies incrementally gained traction in the technology sector and among vital regulatory agencies across the Middle East and North America.
Middle East Cyber Security Market Trends
Rise in the Government initiatives and scalable IT infrastructure
- Africa plays a significant role in the global AI supply chain within the entire market, particularly in the early production phase. Countries, including Egypt, Rwanda, and Mauritius, have published comprehensive AI strategies. African governments are ramping up national strategy on adopting Artificial Intelligence (AI) in a new hunt for crucial data that would help improve public service delivery and governance.
- For instance, The National Infrastructure Plan 2050 of South Africa aims to connect all government buildings to high-speed fibre-optic broadband, universal access, and public sector connectivity, relying on the government as the procure and regulator, with SOEs and the private sector implementing, among other such plans.
- Moreover, The Ministry of Communications and Information Technology (MCIT) has been working to create an infrastructure that is secure, dependable, and accessible to complete Digital Egypt and achieve the transition to a digital society. For instance, earlier this year, the Egyptian National Telecommunications Regulatory Authority (NTRA) signed an MoU with the Saudi Communication and Information Technology Commission (CITC) to collaborate and exchange expertise on a variety of topics, including radio spectrum management, smart cities, and capacity building in digital transformation.
- Also, due to growing government expenditures on advanced technology, Saudi Arabia is anticipated to be one of the top nations in the Middle Eastern area in the artificial intelligence and significant data sector. Due to favorable regulations, government financing, and initiatives, Saudi Arabia has evolved into a digital hub and a supplier in the shift to 5G. For instance, STC's Mena HUB, a USD 1 billion investment in infrastructure and connectivity for the area, supports Saudi Arabia's rapidly expanding digital and cloud sector. Also, the country exhibits readiness to adopt AI, and launching the Saudi Vision 2030 plan was regarded as a significant progression in the value of data as a public asset. Around 70% of the 96 strategic goals under Vision 2030 are related to data and AI.
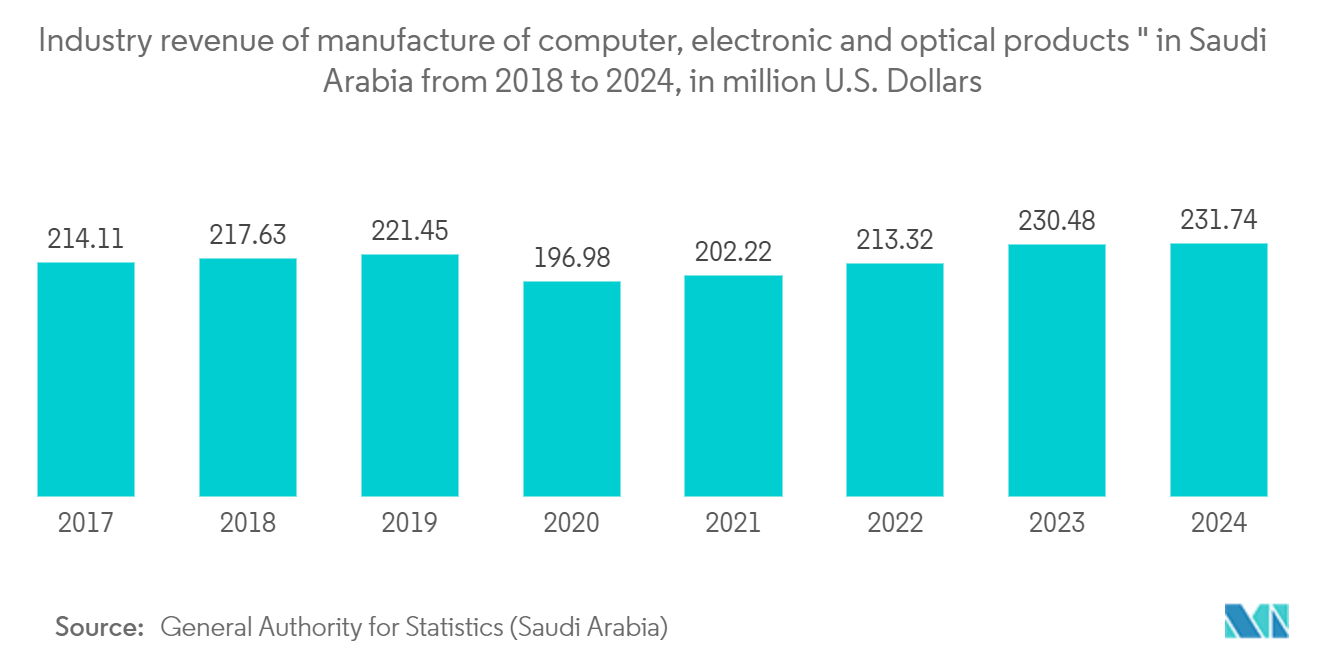
- According to General Authority for Statistics (Saudi Arabia), by 2024, it is expected that Saudi Arabia's optical, electrical, and computer manufacturing will generate around USD 231,7 million in sales. This indicates a drastic growth in the overall IT sector, creating an immense growth opportunity for the market throughout the forecasted period.
IT & Telecom Sector to Witness Significant Growth
- The adoption of AI is growing in popularity in the region owing to AI-based solutions that can be economically used as a service by enterprises for different purposes. AI is being used across the Middle East telecom industry to design products and services, manage life-cycle, remote and onsite operations, and manage large amounts of data being handled.
- During the last quarter of the current year, the Saudi telecommunications corporation STC formed a new subsidiary, Center 3, which will connect Asia, Africa, and Europe through a regional media centre to boost the Kingdom's digital economy. This will significantly increase the market's growth.
- The growing regional IT industry, along with AI initiatives, is expected to boost the AI market in the industry. Governments in the region are looking to skill the professionals who are part of the IT industry to enhance their presence in the global AI sector. For instance, the UAE government's AI Talent Hunt Program and '1 Million Arab Coders' initiatives are expected to impact market growth positively.
- 5G, with its ultra-high speed and low latency, will support new services for South African consumers, like online augmented reality, virtual reality gaming, and ultra-high definition streaming, while enabling businesses with cloud and artificial intelligence technologies. In the last quarter of this year, South African telecoms operator Telkom announced its partnership with Vodacom and MTN using China's Huawei Technologies technology to launch a 5G high-speed internet network.
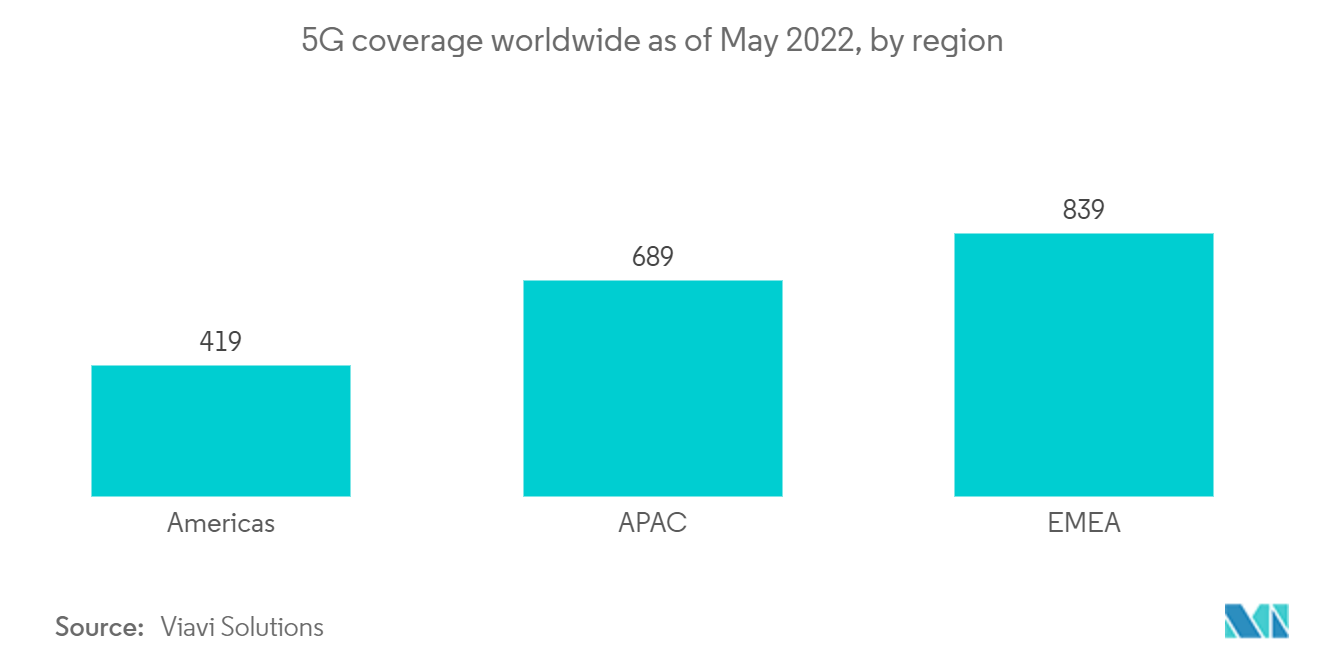
- As per Viavi Solutions, Europe, the Middle East, and Africa (EMEA) surpassed Asia as the region with the highest 5G coverage globally as of May of the current year, with about 839 cities having coverage from a 5G network. While 419 cities in the Americas have commercial 5G services, 689 cities in Asia have 5G coverage overall.
Middle East Cyber Security Industry Overview
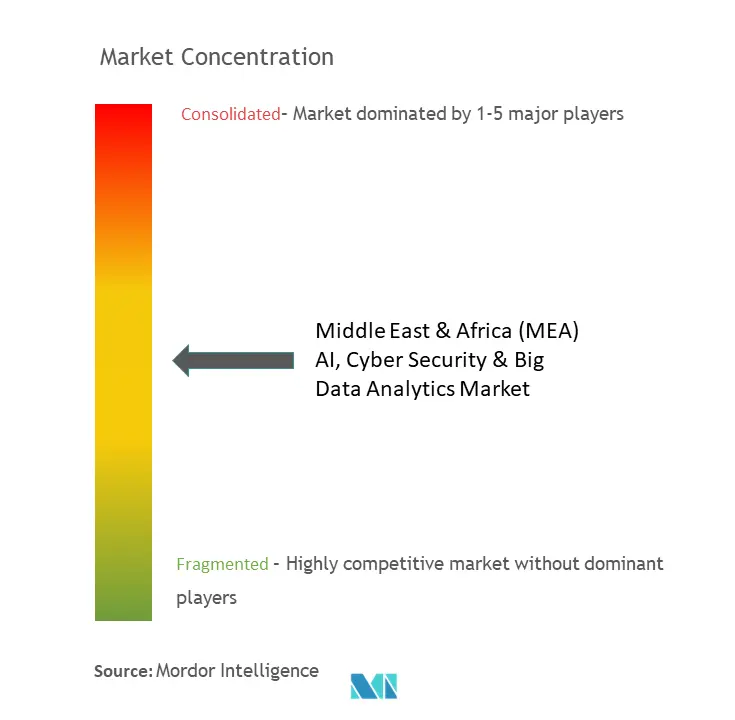
The MEA AI, Cyber Security & Big Data Analytics Market is moderately consolidated, with few firms having a limited share. The companies keep innovating and entering into strategic partnerships to retain their market share. Some of the developments are as follows:
- November 2022 - Saudi Arabia signed a contract to assist economic growth through data and AI. The Saudi Data & AI Authority (SDAIA) and the Ministry of Economy and Planning of Saudi Arabia have signed a preliminary agreement to investigate utilizing artificial intelligence (AI) and data to aid policymaking and economic growth. The deal would permit more intensive strategic collaboration in critical areas, creating metrics to gauge the influence and efficacy of social and economic programs within the kingdom.
- April 2022 - Thales planned to open a new Cyber Security Operations Center (SOC) in Morocco, the sixth in its international network. This centre will offer real-time protection against all the cyber-attacks in the country as well as across the African continent as a whole. This operations center offers African and Moroccan administrations and businesses adequate supervision resources in cybersecurity.
Middle East Cyber Security Market Leaders
-
SYMANTEC CORPORATION (Norton lifelock)
-
Trend Micro INC.
-
SAP SE
-
SAS INSTITUTE INC
-
Microsoft Corporation
- *Disclaimer: Major Players sorted in no particular order
Middle East Cyber Security Market News
- November 2022 - The Saudi Ministry of Finance declared that it permitted two more artificial intelligence companies to operate in the kingdom. QVALON and Faceki thus have business licenses in Saudi Arabia.
- July 2022 - Liquid C2, a business of Cassava Technologies, a pan-African technology group, opened the doors of its first Cyber Security Fusion Centre (CSFC) in Nairobi, Kenya, making this the 2nd center of its kind in Africa. Clients in Kenya would encounter new cybersecurity services that leverage Microsoft Sentinel and Microsoft Defender - all delivered and constantly monitored without interruption.
Middle East Cyber Security Industry Segmentation
The study analyzes the current market scenario and growth trends related to the AI, Cyber Security, and Data Analytics industries in the Middle East & Africa region, with a focus on the developments in the GCC region, which has emerged as one of the major hotspots for investments, aided by substantial investment activity and supportive governmental policies.
The study tracks the country-level market dynamics and the primary implementation use cases for AI and data analytics. The study analyzes the impact of COVID-19 on the region's I and digital transformation-related technologies.
The Market is Segmented by Component (Hardware, Software, Services), End-user Industry (IT & Telecom, Retail, Public & Government Institutions, BFSI, Manufacturing, and Construction, Healthcare), Cyber Security Type (Network, Cloud, Application, End-point, Wireless Network), Big Data Analytics Type (Data Discovery & Visualization, Advanced Analytics), and Country (UAE, Saudi Arabia, Qatar, Kuwait). The market sizes and forecasts are provided in terms of value (USD million) for all the above segments.
| Component | Hardware | ||
| Software | |||
| Services | |||
| End-user Industry | IT & Telecom | ||
| Retail | |||
| Public & Government institutions | |||
| BFSI | |||
| Manufacturing And Construction | |||
| Healthcare | |||
| Other End-user Industries | |||
| Type | Cyber Security Market | Network | |
| Cloud | |||
| Application | |||
| End-point | |||
| Wireless Network | |||
| Other Security Types | |||
| Big Data Analytics Market | Data Discovery & Visualization | ||
| Advanced Analytics | |||
| Country | United Arab Emirates | ||
| Saudi Arabia | |||
| Egypt | |||
| South Africa | |||
| Qatar | |||
| Kuwait | |||
| Morocco | |||
| Rest of the MEA | |||
| Hardware |
| Software |
| Services |
| IT & Telecom |
| Retail |
| Public & Government institutions |
| BFSI |
| Manufacturing And Construction |
| Healthcare |
| Other End-user Industries |
| Cyber Security Market | Network |
| Cloud | |
| Application | |
| End-point | |
| Wireless Network | |
| Other Security Types | |
| Big Data Analytics Market | Data Discovery & Visualization |
| Advanced Analytics |
| United Arab Emirates |
| Saudi Arabia |
| Egypt |
| South Africa |
| Qatar |
| Kuwait |
| Morocco |
| Rest of the MEA |
Middle East Cyber Security Market Research FAQs
What is the current Middle East & Africa (MEA) AI, Cyber Security & Big Data Analytics Market size?
The Middle East & Africa (MEA) AI, Cyber Security & Big Data Analytics Market is projected to register a CAGR of 20.4% during the forecast period (2025-2030)
Who are the key players in Middle East & Africa (MEA) AI, Cyber Security & Big Data Analytics Market?
SYMANTEC CORPORATION (Norton lifelock), Trend Micro INC., SAP SE, SAS INSTITUTE INC and Microsoft Corporation are the major companies operating in the Middle East & Africa (MEA) AI, Cyber Security & Big Data Analytics Market.
What years does this Middle East & Africa (MEA) AI, Cyber Security & Big Data Analytics Market cover?
The report covers the Middle East & Africa (MEA) AI, Cyber Security & Big Data Analytics Market historical market size for years: 2021, 2022, 2023 and 2024. The report also forecasts the Middle East & Africa (MEA) AI, Cyber Security & Big Data Analytics Market size for years: 2025, 2026, 2027, 2028, 2029 and 2030.
Page last updated on: June 16, 2024
Middle East & Africa AI And Cybersecurity Industry Report
Statistics for the 2025 Middle East & Africa (MEA) AI, Cyber Security & Big Data Analytics market share, size and revenue growth rate, created by Mordor Intelligence™ Industry Reports. Middle East & Africa (MEA) AI, Cyber Security & Big Data Analytics analysis includes a market forecast outlook for 2025 to 2030 and historical overview. Get a sample of this industry analysis as a free report PDF download.