IoT Testing Market Size and Share
IoT Testing Market Analysis by Mordor Intelligence
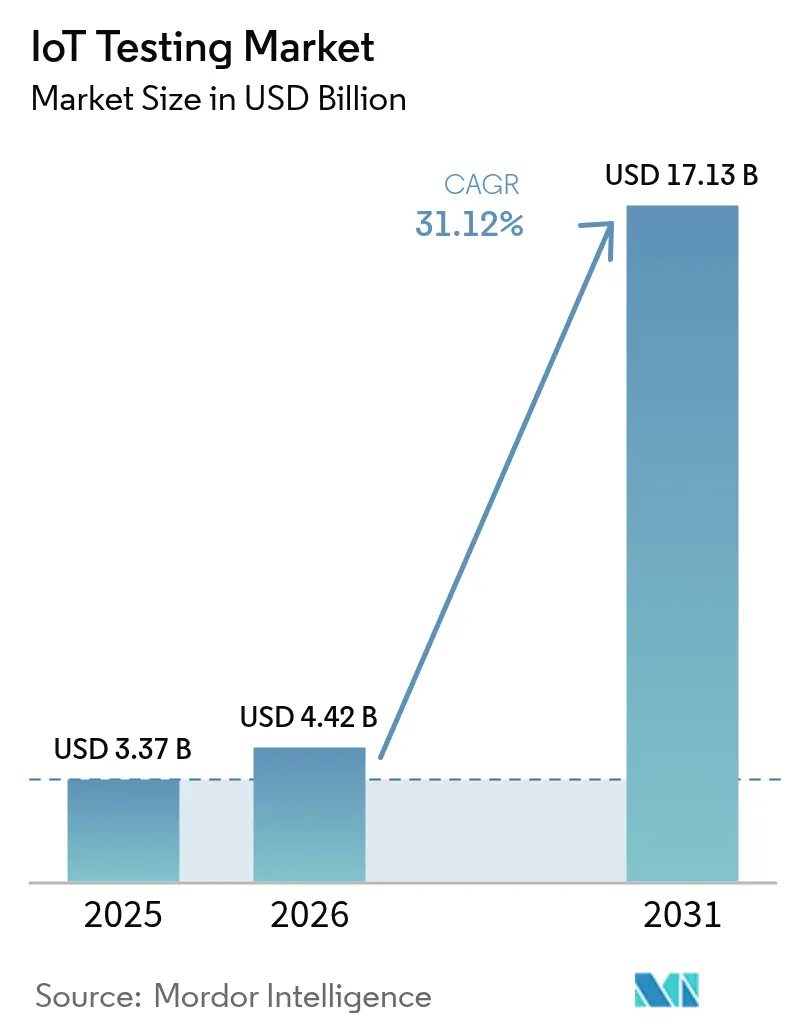
IoT Testing Market size in 2026 is estimated at USD 4.42 billion, growing from 2025 value of USD 3.37 billion with 2031 projections showing USD 17.13 billion, growing at 31.12% CAGR over 2026-2031.
This rapid expansion mirrors rising digital-transformation targets, stricter cybersecurity mandates, and the swelling universe of connected endpoints that now permeate industrial and consumer settings. Enterprises are migrating from reactive to predictive validation models because a single device failure can stall production lines, trigger safety incidents, and invite regulatory penalties running into millions. Low-latency requirements born of 5G and edge computing are intensifying demand for testbeds that can capture millisecond-level performance variations in mission-critical workloads. At the same time, digital-twin environments are cutting hardware costs by letting developers model full device lifecycles in software while maintaining traceability to real-world conditions.
Key Report Takeaways
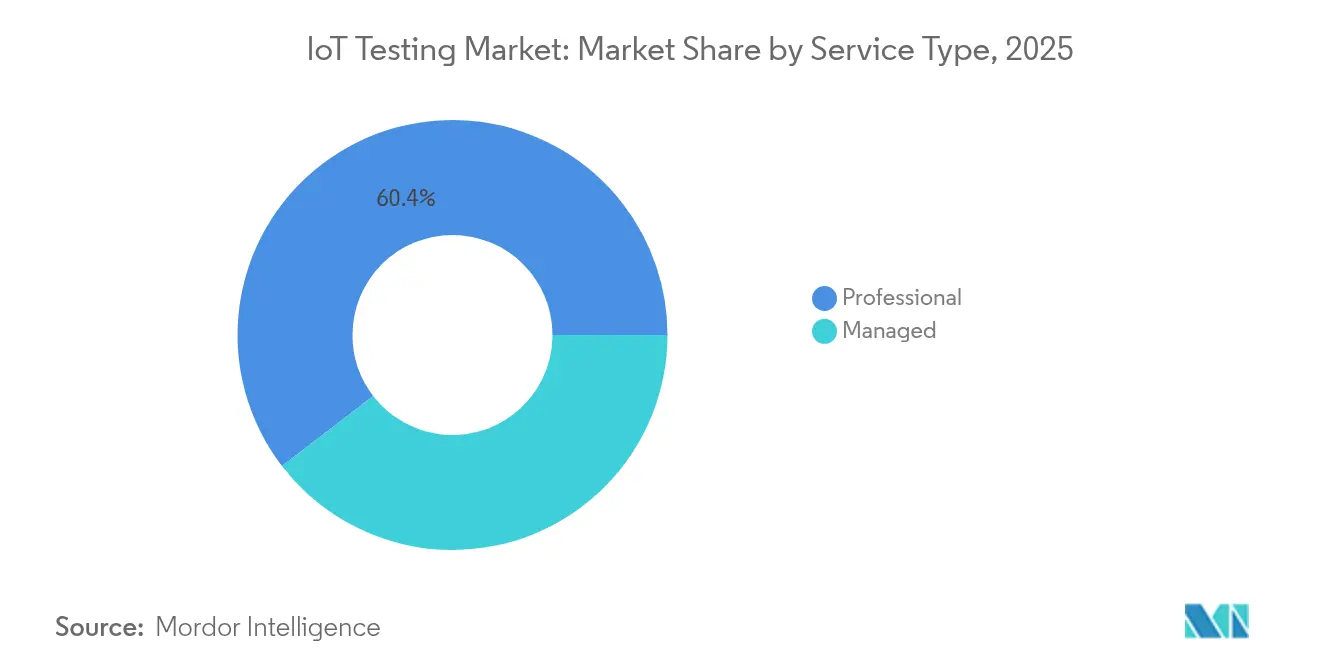
- By service type, professional services held 60.42% of the IoT testing market share in 2025, whereas managed services are projected to expand at an 18.15% CAGR to 2031.
- By testing type, functional testing led with 26.85% revenue share in 2025; security testing is forecast to grow at a 21.95% CAGR through 2031.
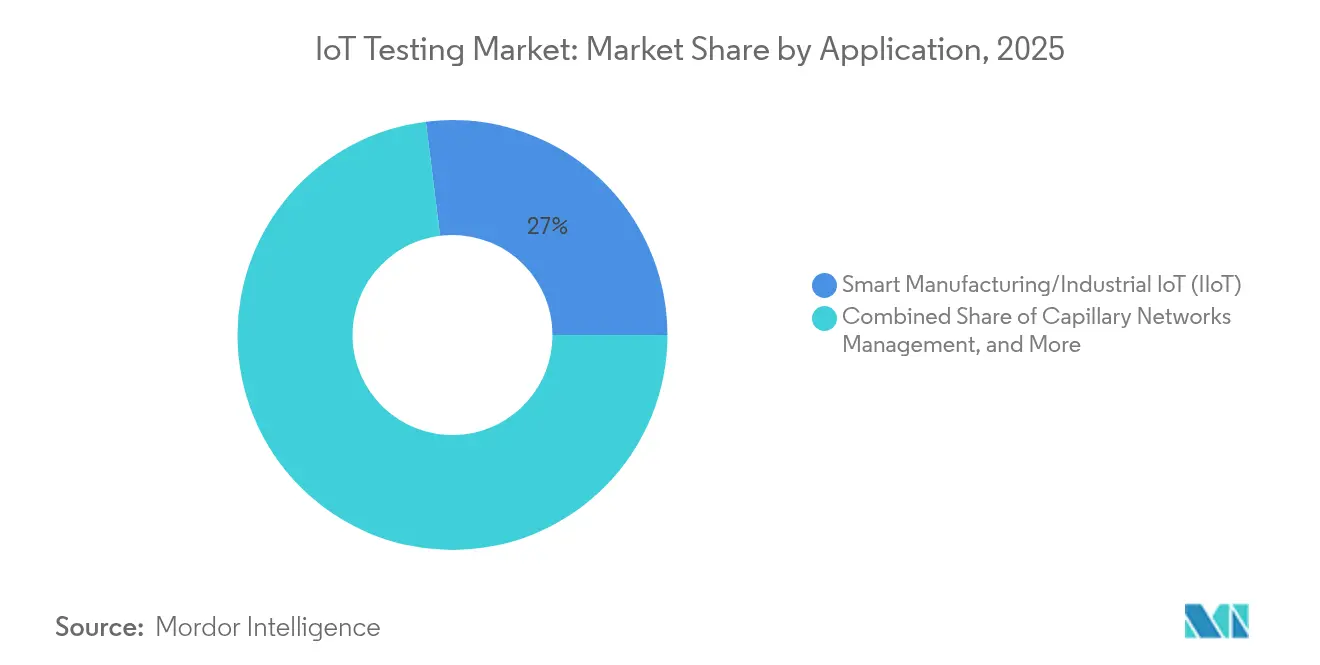
- By application, smart manufacturing/industrial IoT captured 26.98% of the IoT testing market size in 2025, while vehicle telematics is advancing at a 22.35% CAGR to 2031.
- By end-user industry, manufacturing accounted for 27.55% revenue share in 2025; healthcare is expected to post the fastest 18.95% CAGR up to 2031.
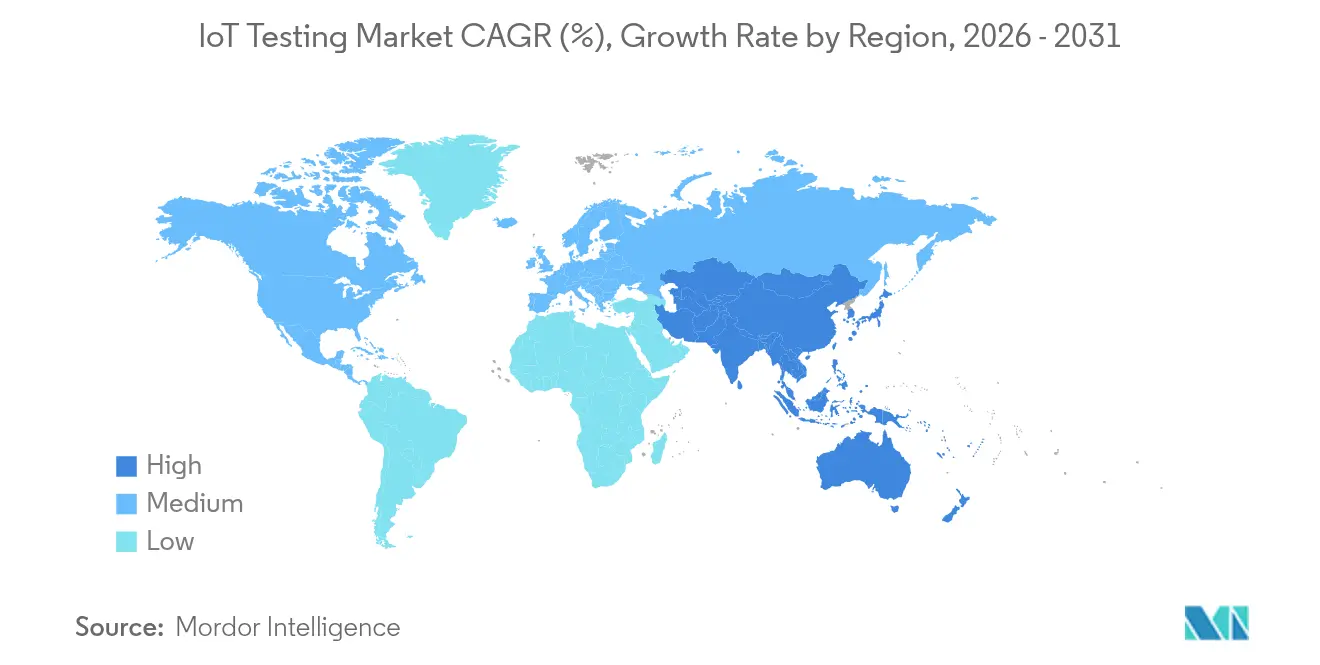
- By region, North America commanded 38.12% of revenue in 2025, and Asia Pacific is set to grow at a 15.32% CAGR to 2031.
Note: Market size and forecast figures in this report are generated using Mordor Intelligence’s proprietary estimation framework, updated with the latest available data and insights as of 2026.
Global IoT Testing Market Trends and Insights
Drivers Impact Analysis*
| Driver | (~) % Impact on CAGR Forecast | Geographic Relevance | Impact Timeline |
|---|---|---|---|
| Explosion in connected IoT endpoints | +8.20% | Global, with Asia Pacific leading deployment density | Medium term (2-4 years) |
| Escalating security and privacy regulations | +6.80% | Europe & North America, expanding to Asia Pacific | Short term (≤ 2 years) |
| Shift toward DevOps and continuous testing pipelines | +5.40% | North America & Europe, enterprise-focused | Medium term (2-4 years) |
| 5G/edge-computing driven low-latency use-cases | +4.90% | Global, concentrated in urban centers | Long term (≥ 4 years) |
| Source: Mordor Intelligence | |||
Explosion in Connected IoT Endpoints
China reported 2.57 billion active IoT terminals by August 2024, underscoring the scale shift that now drives exponentially larger test matrices[1]China Daily, “China’s IoT Terminals Exceed 2.5 Billion,” chinadaily.com.cn. A single smart factory can blend Zigbee sensors, LoRaWAN gateways, and 5G RedCap robots, forcing validation teams to assure seamless interoperability across every protocol permutation. Hyundai and Samsung have already proven private 5G RedCap production lines that demand sub-10 millisecond latency verification. As mixed-generation fleets proliferate, each new device SKU multiplies the combinations that must be certified, compelling enterprises to invest in unified test-automation frameworks able to scale without sacrificing coverage. The IoT testing market must therefore support legacy 4G modules and future 5G endpoints in one configurable environment.
Escalating Security and Privacy Regulations
From August 2025, the European Union’s Radio Equipment Directive obliges every internet-connected product to pass cybersecurity conformance testing before sale. The harmonized EN 18031 series now prescribes network protection, data privacy, and fraud-prevention test cases, expanding compliance workloads well beyond functional checks. In the Gulf region, mandatory biometric SIM registration in Saudi Arabia and the UAE is reshaping connectivity-test protocols. Enterprises unable to field in-house security expertise are increasingly outsourcing validation, steering demand toward managed-service providers inside the IoT testing market.
Shift Toward DevOps and Continuous Testing Pipelines
DevOps adoption is relocating IoT validation from discrete project phases to ongoing pipelines aligned with every code commit. Ford integrates digital-twin models of building-management assets at its Dearborn campus, generating real-time sensor replicas for automated regression runs[2]Ford Motor Company, “Digital Twins Drive Energy Optimization,” corporate.ford.com. “Testing-as-code” applies infrastructure-as-code principles so engineers can spin up identical cloud testbeds on demand, drive parallel scenario execution, and receive pass-fail metrics within hours. These efficiencies curb time-to-market and help the IoT testing market align with agile product roadmaps across the automotive, healthcare, and utilities sectors.
5G/Edge-Computing Driven Low-Latency Use-Cases
Researchers in Munich measured standalone 5G New Radio latency below 7 milliseconds, but production deployments must validate performance under congestion, handover, and edge-node failure scenarios. Azure Private 5G Core now offers industrial clients a containerized network slice plus a companion test suite that mirrors real-time traffic loads before rollout. This fusion of telecom and IT disciplines places fresh emphasis on synchronized radio, transport, and application-layer tests extending the IoT testing market beyond traditional device metrics into holistic system validation.
Restraints Impact Analysis*
| Restraint | (~) % Impact on CAGR Forecast | Geographic Relevance | Impact Timeline |
|---|---|---|---|
| Rising device/protocol complexity | -4.60% | Global, acute in multi-vendor environments | Short term (≤ 2 years) |
| Lack of global interoperability standards | -3.80% | Fragmented across regions and industries | Medium term (2-4 years) |
| Source: Mordor Intelligence | |||
Rising Device/Protocol Complexity
Contemporary deployments mix Wi-Fi 6E sensors, Bluetooth 5.4 beacons, LoRaWAN meters, NB-IoT trackers, and 5G RedCap modems, each demanding distinct tooling. Automotive semiconductor content is projected to hit USD 1,200 per car by 2030, doubling validation points across control units and telematics gateways. Every new protocol stacks onto the existing matrix, lengthening test cycles and challenging resource-constrained labs. Unless automation, virtualization, and AI-enabled prioritization shrink cycle times, this complexity could slow spend within the IoT testing market.
Lack of Global Interoperability Standards
ETSI EN 303 645, US NIST 8259A guidelines, and emerging Chinese smart-city benchmarks all diverge, forcing multinational vendors to certify identical devices three separate times. Redundant testing inflates costs, extends release dates, and limits SMEs’ ability to scale internationally. Harmonization initiatives are underway, yet near-term fragmentation continues to dampen economies of scale for the IoT testing market.
*Our updated forecasts treat driver/restraint impacts as directional, not additive. The revised impact forecasts reflect baseline growth, mix effects, and variable interactions.
Segment Analysis
By Service Type: Professional Services Drive Complex Validations
Professional services dominated 2025 revenue with a 60.42% stake as enterprises leaned on external specialists for multifaceted protocol, security, and compliance needs. Their strength stems from deep benches versed in 5G, RedCap and EU cyber-conformance testing. Managed services, however, are forecast to rise 18.15% annually because manufacturers and fleet operators prefer subscription contracts that guarantee 24/7 lab capacity. HCL Technologies reported USD 13.3 billion FY24 revenue, attributing strong growth to its managed testing portfolios. This transition is redefining delivery models across the IoT testing market and widening demand for fully outsourced validation centers.
The IoT testing market size for managed services is projected to jump from USD 1.33 billion in 2025 to USD 3.63 billion by 2031, mirroring the steep complexity curve that favors dedicated external labs. Global system integrators are investing in remote-accessible device farms so clients can queue tests around the clock without shipping hardware.

By Testing Type: Security Testing Emerges as Growth Leader
Functional validation retained the largest 26.85% revenue slice in 2025 because projects still begin with connectivity and data-flow checks. Nevertheless, security testing is expected to post a 21.95% CAGR through 2031. The IoT testing market must now execute penetration simulations, firmware-integrity scans, and encrypted-channel evaluations aligned with EN 18031 and US FDA pre-market submissions. Applus+ opened a new European cyber-lab in 2024 to fast-track ETSI 303 645 certification demand.
Security services alone could capture 30.20% IoT testing market share by 2031 as regulatory fines push device makers to bake validation into every build. In parallel, performance-stress and network-handover tests stay critical for 5G URLLC scenarios, keeping them relevant, though not as fast-growing.
By Application: Vehicle Telematics Accelerates Past Manufacturing
Smart manufacturing/industrial IoT applications owned 26.98% of 2025 revenue thanks to proven ROI in downtime reduction and predictive maintenance. Thyssenkrupp Materials documented a 52% fall in unplanned stoppages once connected-equipment monitoring went live, underscoring why factories prioritize exhaustive test coverage. Yet vehicle telematics is tracking a blistering 22.35% CAGR, fueled by eSIM rollouts and over-the-air update mandates in Europe and North America. Geotab’s integration program with Volkswagen Group is one illustration of the data volumes and security layers now requiring validation.
Consequently, the IoT testing market size allocated to automotive applications could surpass USD 4.38 billion by 2031, bringing strict ISO 21434 and UNECE R155 cybersecurity clauses into mainstream lab routines.

By End-User Industry: Healthcare Disrupts Manufacturing Leadership
Manufacturing held 27.55% of the 2025 demand as Industry 4.0 programs matured, integrating sensors across conveyors, robots, and warehouse systems. However, remote-patient monitoring and connected therapeutics mean healthcare is set to expand at 18.95% CAGR. The Monit4Healthy project combines multi-sensor fusion with edge analytics for continuous vital tracking and exemplifies the depth of validation now essential for medical devices.
This shift signals rising regulatory oversight from the US FDA’s cybersecurity guidance to the EU MDR, compelling healthcare OEMs to contract specialized partners inside the IoT testing industry for lifecycle-long compliance support.
Geography Analysis
North America led with 38.12% revenue in 2025 as enterprises adopted DevOps pipelines that embed testing from design through production. San Antonio’s SmartSA initiative demonstrates municipal-grade pilots where every lamp-post sensor must clear interoperability and security gates before field deployment. The IoT testing market benefits from established certification ecosystems and well-funded aerospace, automotive, and industrial-automation clients.
Asia Pacific is predicted to post the fastest 15.32% CAGR. China’s Xiong’an 10 Gbps backbone and Beijing’s vehicle-road-cloud pilots elevate demand for massive-scale conformance labs. Japan’s Society 5.0 and South Korea’s USD 101 million national smart-city fund are adding thousands of devices that must be profiled under region-specific telecom and privacy rules. The IoT testing market size in Asia Pacific could cross USD 5.23 billion by 2031 as local vendors integrate cloud-native automation.
Europe maintains solid growth anchored in its rule-first posture. Radio Equipment Directive cybersecurity clauses require third-party labs to run penetration tests before CE marking. Smart-meter rollouts hit 60% for electricity and 45% for gas in 2023, driving sustained validation work for utility suppliers. Nordic telcos are opening shared 5G IoT labs, exemplified by Telenor’s Karlskrona facility that grants global device makers plug-and-play access to Swedish networks. These frameworks ensure the IoT testing market in Europe remains compliance-centric and resilient.
Competitive Landscape
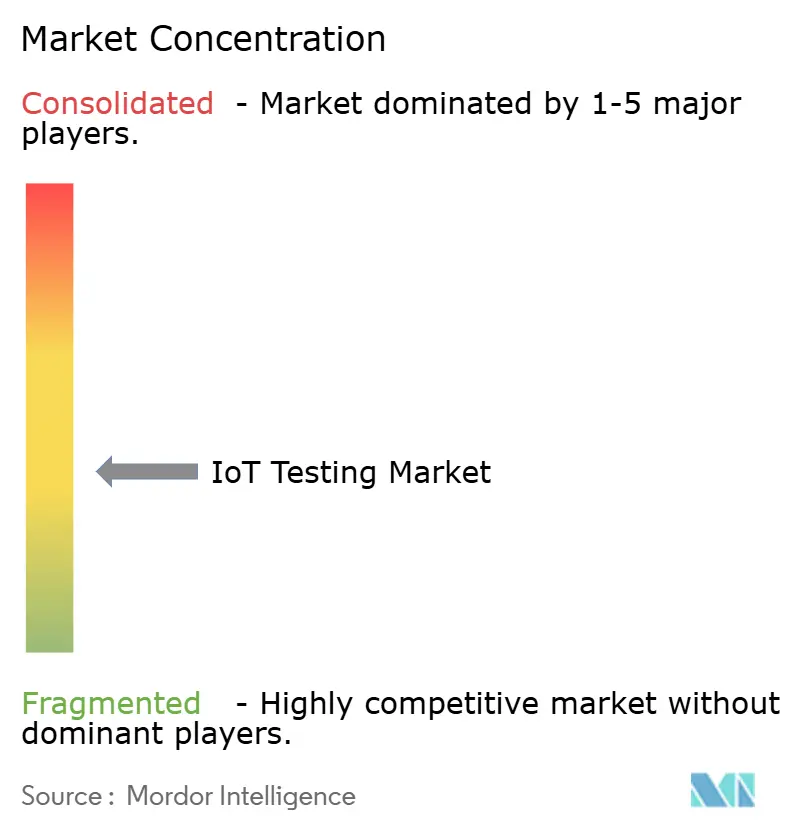
The IoT testing market is moderately fragmented. IBM, Keysight Technologies, HCL Technologies, and Accenture head the global tier, holding diversified device, network, and application test portfolios. Keysight shifted the landscape in March 2025 by acquiring Spirent Communications for USD 1.46 billion, then divesting Ethernet and security assets to VIAVI Solutions for USD 410 million to clear regulators. This maneuver consolidates 5G, cloud, and automotive test assets under one umbrella, accelerating integrated-platform demand.
Vendors now compete on AI-driven automation that slashes scenario-generation time. Rohde & Schwarz patented a context-aware engine that auto-selects required test suites based on detected traffic patterns, pointing toward self-optimizing labs. Edge-computing validation and 5G RedCap conformance are current white-space arenas where niche specialists attract premium valuations. Cloud-native upstarts offer containerized, pay-as-you-go environments appealing to start-ups and SMEs who cannot finance dedicated hardware labs. Continued acquisitions are likely as buyers seek one-stop partners able to traverse device, network, cloud, and application layers within the IoT testing industry.
IoT Testing Industry Leaders
Novacoast, Inc.
Keysight Technologies, Inc.
Praetorian Security, Inc.
Apica Systems
AFour Technologies Pvt. Ltd. (ACL Digital)
- *Disclaimer: Major Players sorted in no particular order


Recent Industry Developments
- March 2025: Keysight completed Spirent acquisition (USD 1.46 billion) and sold Spirent Ethernet/security units to VIAVI (USD 410 million), creating a USD 1.5 billion expansion avenue in cloud and 5G testing.
- February 2025: Hyundai Motor and Samsung showcased private 5G RedCap for smart factories, demanding ultra-reliable low-latency testing profiles.
- January 2025: Samsara deepened collaboration with Stellantis via Mobilisights, easing European fleet telematics integration.
- November 2024: Keysight posted USD 4.98 billion FY24 revenue, including USD 894 million from communications-testing solutions focused on AI-driven automation.
Global IoT Testing Market Report Scope
IoT testing can be defined as a procedure that includes running an IoT solution through a number of tests to make sure it is prepared for practical applications. The market for the study defines the revenues generated from the sales of IoT testing services across various end-users, including retail, manufacturing, healthcare, energy and utilities, IT & telecom. The market also covers the major factors impacting the growth of the IoT testing market in terms of drivers and restraints.
The IoT Testing Market is segmented by Service Type (Professional, Managed), Testing Type (Functional Testing, Performance Testing, Network Testing, Compatibility Testing, Usability Testing, Security Testing), End-user Industry (Retail, Manufacturing, Healthcare, Energy and Utilities, IT & Telecom), and Geography (North America, Europe, Asia Pacific, Latin America, and Middle East & Africa). The market sizes and forecasts are provided in terms of value (USD million) for all the above segments.
| Professional |
| Managed |
| Functional Testing |
| Performance Testing |
| Network Testing |
| Compatibility Testing |
| Security Testing |
| Usability Testing |
| Smart Building and Home Automation |
| Capillary Networks Management |
| Smart Utilities (Energy / Water) |
| Vehicle Telematics and Connected Vehicles |
| Smart Manufacturing / Industrial IoT (IIoT) |
| Retail |
| Manufacturing |
| Healthcare |
| Energy and Utilities |
| IT and Telecom |
| Government and Smart Cities |
| Transportation and Logistics |
| Other Industries |
| North America | United States | |
| Canada | ||
| Mexico | ||
| South America | Brazil | |
| Argentina | ||
| Rest of South America | ||
| Europe | United Kingdom | |
| Germany | ||
| France | ||
| Italy | ||
| Spain | ||
| Rest of Europe | ||
| Asia-Pacific | China | |
| Japan | ||
| India | ||
| South Korea | ||
| Rest of Asia-Pacific | ||
| Middle East and Africa | Middle East | United Arab Emirates |
| Saudi Arabia | ||
| Turkey | ||
| Rest of Middle East | ||
| Africa | South Africa | |
| Nigeria | ||
| Rest of Africa | ||
| By Service Type | Professional | ||
| Managed | |||
| By Testing Type | Functional Testing | ||
| Performance Testing | |||
| Network Testing | |||
| Compatibility Testing | |||
| Security Testing | |||
| Usability Testing | |||
| By Application | Smart Building and Home Automation | ||
| Capillary Networks Management | |||
| Smart Utilities (Energy / Water) | |||
| Vehicle Telematics and Connected Vehicles | |||
| Smart Manufacturing / Industrial IoT (IIoT) | |||
| By End-user Industry | Retail | ||
| Manufacturing | |||
| Healthcare | |||
| Energy and Utilities | |||
| IT and Telecom | |||
| Government and Smart Cities | |||
| Transportation and Logistics | |||
| Other Industries | |||
| By Geography | North America | United States | |
| Canada | |||
| Mexico | |||
| South America | Brazil | ||
| Argentina | |||
| Rest of South America | |||
| Europe | United Kingdom | ||
| Germany | |||
| France | |||
| Italy | |||
| Spain | |||
| Rest of Europe | |||
| Asia-Pacific | China | ||
| Japan | |||
| India | |||
| South Korea | |||
| Rest of Asia-Pacific | |||
| Middle East and Africa | Middle East | United Arab Emirates | |
| Saudi Arabia | |||
| Turkey | |||
| Rest of Middle East | |||
| Africa | South Africa | ||
| Nigeria | |||
| Rest of Africa | |||


Key Questions Answered in the Report
What is the current size of the IoT testing market?
The IoT testing market size is USD 4.42 billion in 2026.
How fast is the IoT testing market expected to grow?
It is projected to register a 31.12% CAGR, reaching USD 17.13 billion by 2031.
Which service model is expanding fastest?
Managed services are forecast to grow at an 18.15% CAGR as enterprises outsource complex validation work.
Why is security testing gaining momentum?
Cybersecurity mandates such as the EU Radio Equipment Directive require mandatory conformance, driving a 21.95% CAGR for security testing.
Which region offers the strongest growth outlook?
Asia Pacific is expected to advance at a 15.32% CAGR, supported by large-scale smart-city programs in China, Japan and South Korea.
How will 5G influence IoT testing demand?
5G and edge computing introduce sub-10 millisecond latency targets, compelling investments in advanced testbeds that simulate real-world network dynamics.
Page last updated on: