BFSI Security Market Size and Share
BFSI Security Market Analysis by Mordor Intelligence
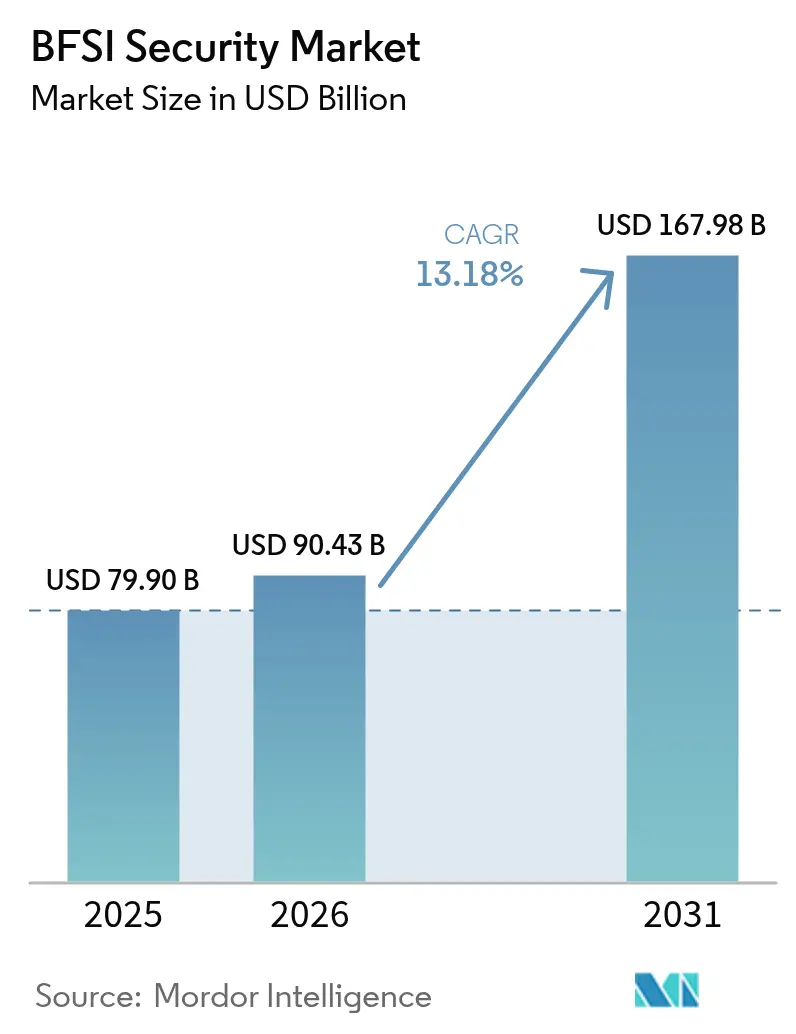
The BFSI security market size was valued at USD 79.9 billion in 2025 and estimated to grow from USD 90.43 billion in 2026 to reach USD 167.98 billion by 2031, at a CAGR of 13.18% during the forecast period (2026-2031). This trajectory underscores how regulators, banks and insurers are reacting to an unrelenting spike in sophisticated breaches, typified by the February 2025 email compromise at the Office of the Comptroller of the Currency that exposed more than 100 senior officials’ messages. Rising third-party risk came into sharper focus after the April 2025 ransomware strike on Toppan Next Tech that affected customer records from DBS Bank and Bank of China’s Singapore branch.[1]Monetary Authority of Singapore, “Ransomware Attack on Toppan Next Tech,” mas.gov.sg At the same time, the European Union’s Digital Operational Resilience Act (DORA) and parallel rules in India and New York are compelling financial firms to replace periodic audits with real-time controls. The result is a steady redirection of budgets toward zero-trust architectures, cloud-native defenses and quantum-safe cryptography pilots, all of which continue to expand the BFSI security market.
Key Report Takeaways
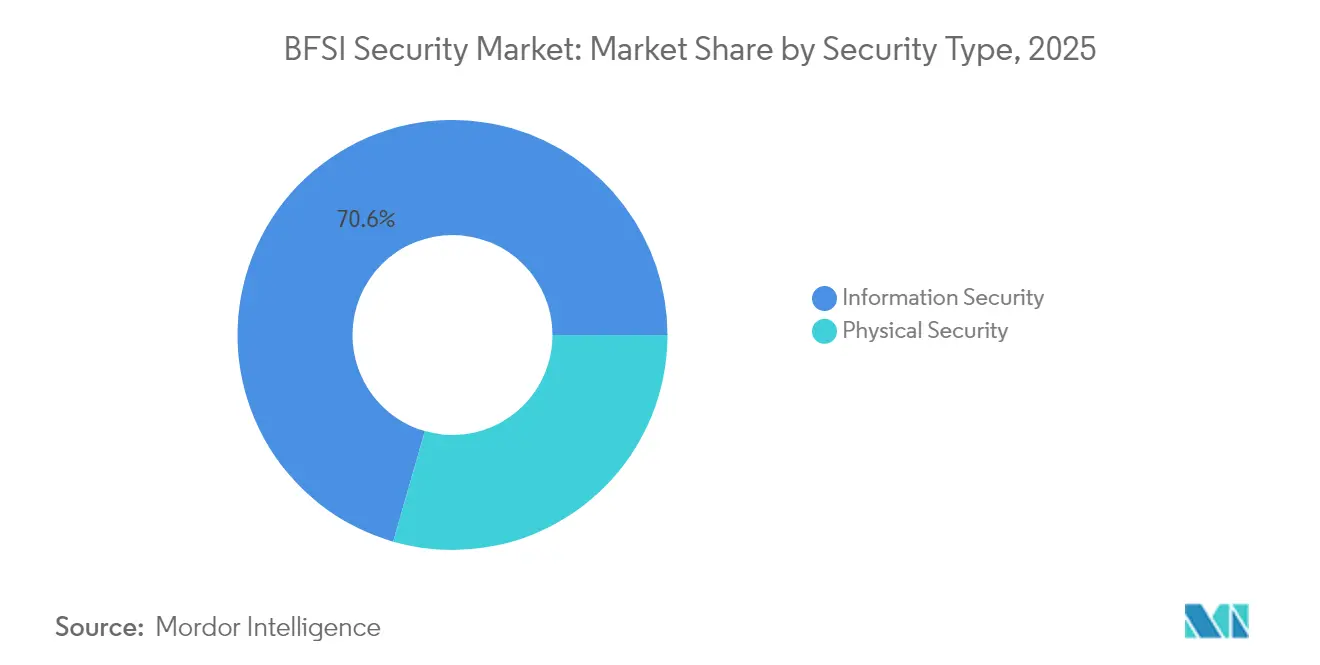
- By security type, Information Security led with 70.55% revenue share in 2025; cloud-based sub-solutions are advancing at a 16.15% CAGR through 2031.
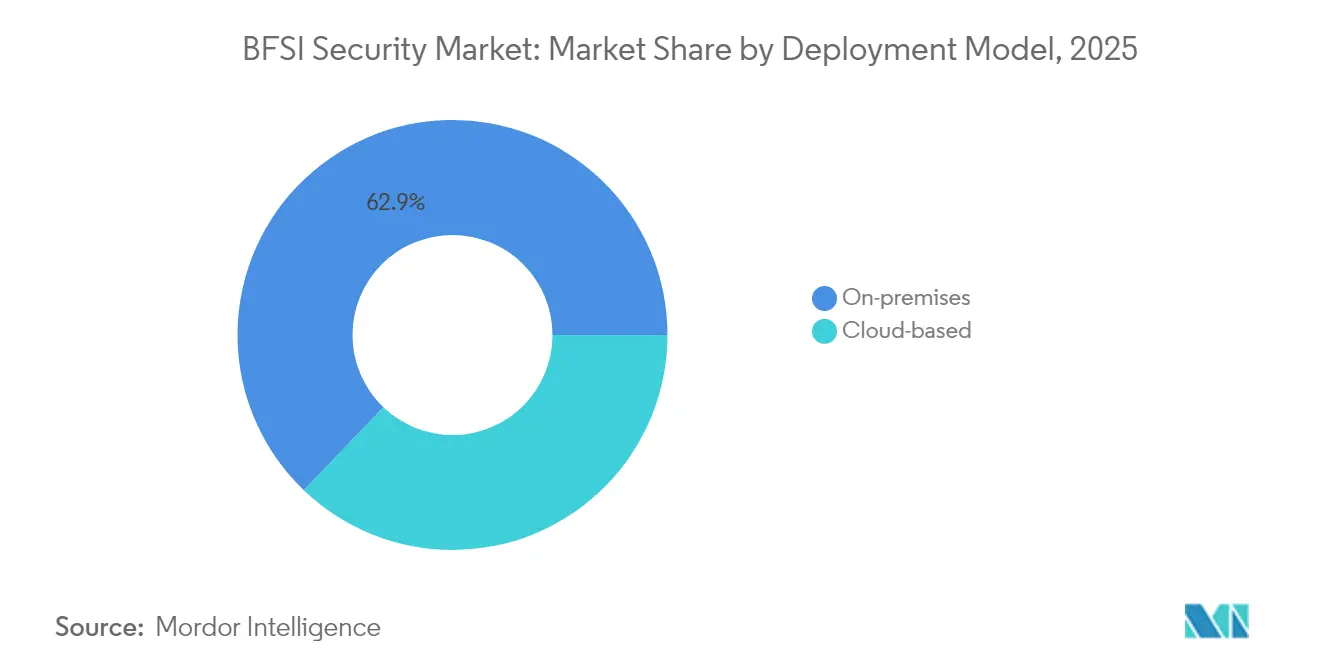
- By deployment model, on-premises retained 62.85% of the BFSI security market share in 2025, while cloud models are growing quickest at 19.25% CAGR.
- By vertical, banking institutions held 60.95% of the BFSI security market size in 2025; the insurance segment is expanding at a 15.12% CAGR to 2031.
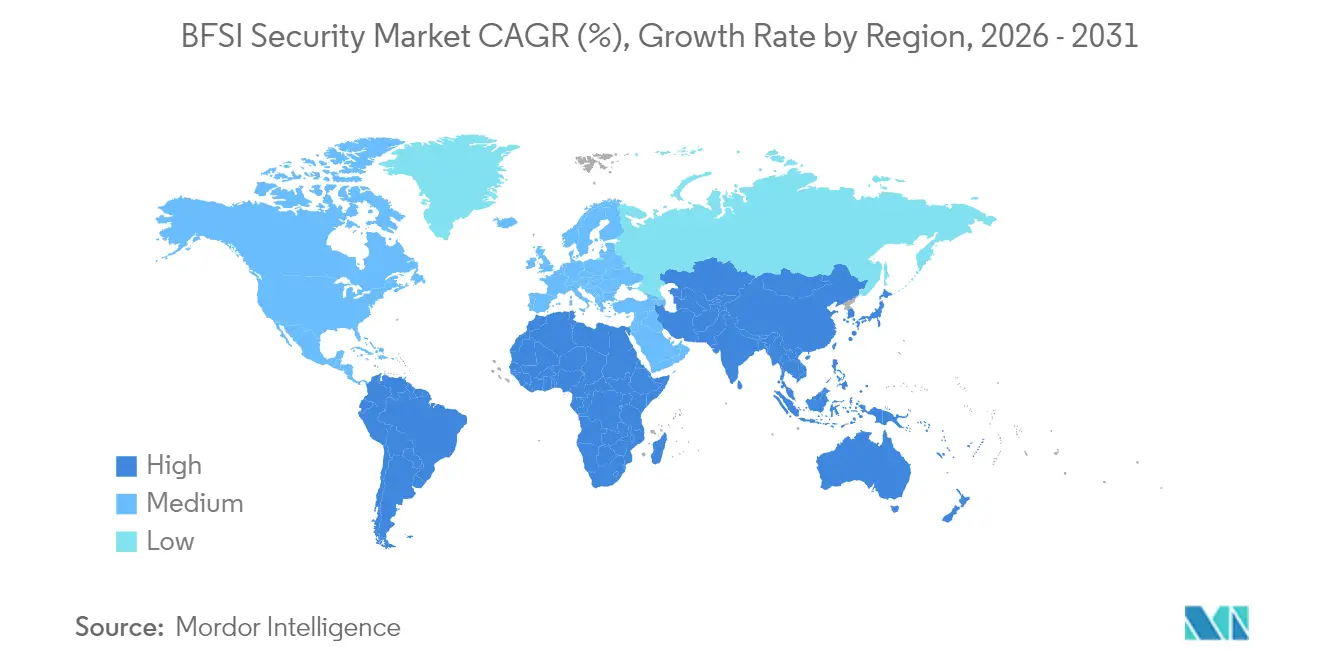
- By geography, North America accounted for 36.10% revenue in 2025, whereas Asia-Pacific is the fastest-growing region at 14.72% CAGR.
- Palo Alto Networks, Fortinet, Check Point, Cisco and IBM collectively supplied integrated platforms that served more than half of the top 200 global banks in 2024.
Note: Market size and forecast figures in this report are generated using Mordor Intelligence’s proprietary estimation framework, updated with the latest available data and insights as of 2026.
Global BFSI Security Market Trends and Insights
Drivers Impact Analysis*
| Driver | (~) % Impact on CAGR Forecast | Geographic Relevance | Impact Timeline |
|---|---|---|---|
| Surge in digital banking transactions | +3.2% | Global, highest in Asia-Pacific and Europe | Medium term (2-4 years) |
| Escalating sophistication of cyber-attacks | +2.8% | Global, especially North America and Europe | Short term (≤ 2 years) |
| Stringent data-protection regulations | +2.1% | Europe and North America, expanding to Asia-Pacific | Medium term (2-4 years) |
| Cloud migration of core-banking platforms | +1.9% | Global, led by North America and Europe | Long term (≥ 4 years) |
| AI-driven fraud-prevention adoption | +1.4% | North America and Asia-Pacific | Medium term (2-4 years) |
| Open-banking APIs expanding attack surface | +1.1% | Europe and North America | Short term (≤ 2 years) |
| Source: Mordor Intelligence | |||
Surge in Digital Banking Transactions
Electronic payments continue to cannibalize cheques, driving volumes that legacy fraud-detection stacks cannot analyze in real time. Singapore’s Monetary Authority has set mid-2025 for nationwide Electronic Deferred Payment roll-out, while India now obliges banks to deploy AI-powered behavioural analytics for fraud spotting.[2]Grant Thornton Bharat, “RBI Regulatory Banking Insights: August 2024,” grantthornton.in These mandates are funnelling spending toward cloud-native transaction monitoring and low-latency core-banking APIs. As the BFSI security market broadens, vendors that can inspect payloads at millisecond speed without performance drag secure a first-mover advantage. Institutions are also overhauling authentication flows to support risk-based step-up verification for high-value transfers, further accelerating platform rip-and-replace activity.
Escalating Sophistication of Cyber-Attacks
The LockBit assault on Evolve Bank and Trust laid bare the dual-threat model of encryption plus data theft, while the Minja memory injection exploit reached a 95% success rate against AI chatbots in lab tests.[3]Jack Naglieri, “The Evolve Bank and Trust Breach,” jacknaglieri.substack.com Attackers now weaponize large language models to refine phishing scripts in seconds, leaving signature-based controls obsolete. Financial firms therefore prioritize behavioural analytics, adversary emulation and automated response orchestration. The BFSI security market responds by bundling extended detection and response (XDR) with threat-intelligence enrichment so analysts can triage novel tactics in minutes rather than hours. Proof-of-concept quantum decryption techniques also loom, nudging boards to allocate seed budgets for quantum-resistant encryption roll-outs.
Stringent Data-Protection Regulations
New rules tighten timelines for breach disclosure and mandate threat-led penetration testing. DORA fines can reach 2% of annual turnover, creating a cost-of-non-compliance higher than many attack losses. In India, SEBI’s Cybersecurity and Cyber-Resilience Framework imposes near-real-time risk dashboards for capital-markets entities. Meanwhile, the United States’ CFPB Section 1033 standardizes open-banking APIs, forcing unified security layers across data aggregators.[4]Ozone API Marketing, “Technical Guide to CFPB Section 1033,” ozoneapi.com These statutes are expanding the addressable BFSI security market as institutions swap periodic audits for continuous-compliance automation platforms and micro-segmentation.
Cloud Migration of Core-Banking Platforms
Almost every financial institution now runs at least one regulated workload in a public or hybrid cloud, according to the Cloud Security Alliance’s 2025 survey. The FFIEC’s new guidance clarifies shared-responsibility models, reducing board-level hesitation. Yet migration lifts the threat surface from well-defined data centers to distributed multi-cloud topologies. Vendors that embed policy-as-code, container runtime defense and cloud security posture management into unified consoles gain traction within the BFSI security market. Banks increasingly replace virtual appliances with agentless scanning that baselines workloads in seconds and auto-remediates misconfigurations before auditors flag them.
Restraints Impact Analysis*
| Restraint | (~) % Impact on CAGR Forecast | Geographic Relevance | Impact Timeline |
|---|---|---|---|
| High total cost of ownership | -1.8% | Global, hardest on mid-tier institutions | Medium term (2-4 years) |
| Legacy-system integration complexity | -1.5% | North America and Europe, rising in Asia-Pacific | Long term (≥ 4 years) |
| Cyber-security talent shortage | -1.2% | Global, most acute in mature markets | Long term (≥ 4 years) |
| Cross-border data-residency ambiguity | -0.9% | Multinational institutions worldwide | Medium term (2-4 years) |
| Source: Mordor Intelligence | |||
High Total Cost of Ownership
Globally, budget growth for cyber programs decelerated to 8% in 2024, down from 16% in 2021, as economic headwinds and unclear ROI stall spending. Mid-tier institutions earmark 13.2% of IT outlays for security yet still report readiness gaps, reflecting fragmentation across dozens of overlapping tools. Tool sprawl inflates licensing, integration and SOC staffing costs, suppressing net new investment and placing a drag on the BFSI security market. Consolidated platforms that automate triage and incident response can lower per-alert costs by 40%, but migration budgets often exceed in-year savings, prolonging payback windows and delaying purchase approvals.
Legacy-System Integration Complexity
Many core-banking engines still rely on COBOL code, limiting compatibility with API-driven zero-trust controls. Post-quantum encryption initiatives risk breaking older message formats outright, requiring wholesale system replacement rather than patching. Integration projects stretch across multiple fiscal years and consume scarce engineering bandwidth, slowing rollout of advanced defenses and tempering expansion of the BFSI security market. Institutions therefore triage modernization roadmaps, leaving non-internet-facing workloads on legacy stacks and restricting system scopes for new tooling to avoid business disruption.
*Our updated forecasts treat driver/restraint impacts as directional, not additive. The revised impact forecasts reflect baseline growth, mix effects, and variable interactions.
Segment Analysis
By Security Type: Information Security Dominates Digital Transformation
Information Security captured 70.55% of the BFSI security market share in 2025, far outpacing physical controls as customer engagement shifts to digital channels. Demand concentrates on data-loss prevention, endpoint detection and response, and identity governance platforms that satisfy DORA’s prescriptive testing clauses. The BFSI security market size for Information Security will expand at 16.15% CAGR through 2031, powered by mandatory threat-led penetration testing and AI infusion into fraud analytics.
Convergence of physical and logical safeguards is nonetheless advancing. Branch and data-center operators integrate biometric access logs with SIEM dashboards, enabling unified risk scoring. Zero-trust blueprints treat door readers and API gateways alike, requiring continuous verification before granting privileges. Vendors that supply interoperable credential management vaults therefore secure a growing slice of the BFSI security market. Institutions also pilot deception grids and autonomous threat-containment to reduce mean-time-to-respond below the regulatory 24-hour disclosure threshold.

By Service Type: Integration Services Lead Market Transformation
System-integration specialists accounted for 40.05% of 2025 revenue as banks wrestled with patch-work architectures and regulatory deadlines. Every DORA or NYDFS requirement triggers mapping of control libraries, API hooks and audit workflows into heterogeneous tech stacks, solidifying integration services’ place at the center of the BFSI security market. Managed Security Services follow closely, forecast to climb 18.55% CAGR on the back of 24/7 monitoring mandates that smaller lenders cannot staff internally.
The financial services cybersecurity industry increasingly favors outcome-based contracts over time-and-materials engagements. Cisco’s HyperShield release bundles autonomous segmentation with professional services, offering guaranteed vulnerability remediation windows. In response, mid-market banks outsource alert triage to specialised SOCs, cutting incident dwell times by up to 60%. Ecosystem partners embed compliance dashboards that align with auditors’ report formats, reinforcing integration services’ pivotal role in capitalization of the BFSI security market.
By Deployment Model: Cloud Adoption Accelerates Despite Compliance Concerns
On-premises solutions still held 62.85% of spending in 2025 as risk-averse boards favored direct control and granular data-residency assurance. That said, cloud deployments are on a 19.25% CAGR curve, underpinned by elastic compute and native AI acceleration that on-premises hardware struggles to match. Hybrid blueprints dominate large-bank strategies, blending private clouds for regulated workloads with public IaaS/SaaS for analytics.
Asia-Pacific regulators now issue explicit guidance on shared responsibility, dissipating residual hesitation and unlocking further growth in the BFSI security market. The BFSI security market size tied to cloud-native workloads is expected to more than double by 2031. Vendors that deliver agentless posture management, serverless runtime defense and near-real-time compliance evidence find receptive audiences, particularly among digital-only banks that bypassed legacy data centers altogether.

By Vertical: Banking Institutions Drive Market Growth
Banking institutions constituted 60.95% of 2025 revenue and remain the BFSI security market’s anchor clientele. High-value account data, real-time payment rails and stringent supervisory audits fuel sustained investment. The insurance segment, though smaller, is projected to post a 15.12% CAGR as NAIC’s Model Law and NYDFS Part 500 enforcement expand.
Within the segment, insurers deploy quantitative risk engines that link control maturity to underwriting capital, tying cybersecurity investments directly to premium pricing. Credit unions and payment processors follow suit, adapting bank-grade controls to lighter budget envelopes. Insurance providers’ embrace of threat-led red-team exercises broadens the BFSI security market, rewarding solution vendors that demonstrate measurable risk reduction in actuarial models. Overall, the vertical mix is diversifying, with non-bank entities accounting for a growing minority of total spend.
Geography Analysis
North America commanded 36.10% of revenue in 2025 thanks to early adoption of NYDFS Part 500, CISA sector directives and a mature breach-notification regime that fines non-compliance within days. Competitive pressure among Tier-1 banks spurred multiyear platform refreshes that now trickle down to regional lenders and fintechs, solidifying the region’s leadership in the BFSI security market.
Asia-Pacific is expanding at a 14.72% CAGR, propelled by Singapore’s Shared Responsibility Framework and India’s AI-based fraud monitoring mandates. The BFSI security market size for Asia-Pacific grew past USD 26.4 billion in 2026, spurred by 31% of global cyber incidents targeting the region commonwealth.int. Local banks accelerate cloud adoption under regulatory sandbox regimes, while Japan and Australia push quantum-safe pilots, further widening growth differentials versus mature markets.
Europe holds significant weight via DORA, GDPR and the NIS 2 Directive. Harmonized supervisory expectations drive cross-border platform consolidation, giving rise to pan-European managed SOC hubs. The BFSI security market in Europe increasingly demands vendor evidence of full supply-chain resilience, including continuous third-party risk scoring and in-region key custody, keeping spending momentum steady through the decade.
Competitive Landscape
Market consolidation intensified in 2024–2025 as boards insisted on platform rationalization to tame alert fatigue and redundancy. Palo Alto Networks’ USD 500 million purchase of IBM’s QRadar SaaS portfolio created a unified Cortex-centric stack spanning SIEM, XDR and compliance reporting. Cisco’s HyperShield integrates Splunk telemetry with autonomous segmentation, reflecting a shift toward AI-assisted remediation that slashes patch windows from weeks to minutes.
Quantum-safe encryption emerges as a battleground. Fitch Ratings notes that JPMorgan Chase and HSBC have piloted quantum key distribution, nudging incumbents to embed post-quantum algorithms across TLS, VPN and hardware security modules. Niche vendors offering lattice-based cryptography APIs attract venture funding as banks brace for Crypto-Agile transformation roadmaps.
Meanwhile, verticalized compliance solutions gain traction. Start-ups tailor dashboards for DORA or PCI DSS 4.0, integrating evidence collection and narrative-ready reporting. Larger vendors respond with modular packaging, allowing customers to subscribe to specific compliance regimes as plug-ins. Strategic alliances with global system integrators ensure turnkey delivery, while managed-service overlays help mid-tier banks circumvent talent shortages.
BFSI Security Industry Leaders
Symantec Corporation
Sophos Group Plc.
McAfee Inc.
IBM Corporation
Honeywell International Inc.
- *Disclaimer: Major Players sorted in no particular order


Recent Industry Developments
- June 2025: Hypernative raised USD 40 million to expand real-time loss-prevention tools that flagged USD 2.2 billion in potential crypto hacks during 2024.
- April 2025: Singapore’s MAS confirmed vulnerable-customer safeguards will begin in H2 2025, bolstering data-protection duties for all licensees.
- April 2025: The OCC disclosed an email breach affecting about 100 senior officials, triggering immediate coordination with CISA.
- January 2025: The EU’s DORA entered into force, setting uniform ICT-risk standards for more than 22,000 European financial entities.
Research Methodology Framework and Report Scope
Market Definitions and Key Coverage
Our study defines the BFSI security market as all commercially procured physical-security systems (surveillance, access control, vault protection) and information-security solutions and related services (network, cloud, endpoint, identity, threat analytics, integration, support) that banking, financial services, and insurance institutions deploy to prevent or mitigate unauthorized access, fraud, and data loss.
Scope Exclusion: Spending on internally built, non-commercial tools and cash-replenishment logistics is excluded.
Segmentation Overview
- By Security Type
- Information Security
- Physical Security
- By Service Type
- System Integration
- Maintenance
- Support
- By Deployment Model
- On-premises
- Cloud-based
- By Vertical
- Banking
- Insurance
- Other Financial Institutions
- By Geography
- North America
- United States
- Canada
- Mexico
- South America
- Brazil
- Argentina
- Rest of South America
- Europe
- Germany
- United Kingdom
- France
- Spain
- Italy
- Rest of Europe
- Asia-Pacific
- China
- Japan
- South Korea
- India
- Australia and New Zealand
- Rest of Asia-Pacific
- Middle East
- Israel
- Saudi Arabia
- United Arab Emirates
- Turkey
- Rest of Middle East
- Africa
- South Africa
- Egypt
- Nigeria
- Rest of Africa
- North America
Detailed Research Methodology and Data Validation
Primary Research
Mordor analysts interviewed chief information security officers, risk heads, and compliance leads at banks, insurers, and fintech platforms across North America, Europe, Asia-Pacific, and the Gulf. These conversations validated deployment preferences, average selling prices, and upcoming budget resets, filling gaps left by public statistics.
Desk Research
We began with structured desk work, gathering baseline figures from tier-1 regulators and associations such as the Bank for International Settlements, the European Central Bank, the US Federal Deposit Insurance Corporation, FS-ISAC incident reports, and NIST, as well as regional cybersecurity agencies. Company filings, listed-bank 10-Ks, and investor presentations clarified security-spend ratios, while reputed global press helped trace breach costs and merger activity.
For supplier financials and deal pipelines, we tapped D&B Hoovers and screened global news on Dow Jones Factiva, which allowed us to benchmark vendor revenue derived from BFSI contracts across regions. Many other secondary sources were also consulted for cross-checks and context.
Market-Sizing & Forecasting
A top-down construct starts with country-level IT-security spending by financial institutions, rebuilt from regulatory filings and capital-expenditure disclosures, and then allocates shares to physical and information security sub-pools. Results are corroborated through selective bottom-up vendor roll-ups, sampled ASP-times-volume checks, and channel partner feedback. Key drivers in the model include 1) number of active mobile-banking users, 2) cost per reported cyber incident, 3) regulatory compliance outlay linked to PCI DSS and DORA, 4) branch digital-transaction ratio, and 5) share of cloud workloads hosted off-premise. Forecasts employ a multivariate regression that ties those variables to historic spend patterns and are stress-tested with scenario analysis provided by our primary respondents. Gap patches where supplier data are thin rely on nearest-neighbor averages adjusted for purchasing-power parity.
Data Validation & Update Cycle
Outputs pass an anomaly check against independent indicators and peer review by a second analyst team before sign-off. We refresh every twelve months, triggering interim updates when material events, major breaches, and new mandates, as well as currency swings, alter the demand curve, and we revalidate figures just before client delivery.
Why Mordor's BFSI Security Baseline Commands Confidence
Published estimates vary because firms diverge on scope, currency treatment, refresh cadence, and the weight they give to managed services versus hardware.
Key gap drivers include some publishers folding branch-automation hardware into security totals, using outdated exchange rates, or excluding cloud-delivered managed detection and response. Our disciplined definition, mixed-method sizing, and annual refresh keep our baseline balanced and decision-ready.
Benchmark comparison
| Market Size | Anonymized source | Primary gap driver |
|---|---|---|
| USD 79.9 B (2025) | Mordor Intelligence | - |
| USD 69.0 B (2024) | Regional Consultancy A | Adds NBFC branch-automation hardware; older base year |
| USD 70.7 B (2024) | Trade Journal B | Uses constant-2023 FX and omits managed security services |
In sum, the small but critical choices our team makes on scope, variable selection, and iterative validation enable Mordor Intelligence to deliver a transparent, reproducible benchmark that clients trust for strategic planning.


Key Questions Answered in the Report
What is the current size of the BFSI security market?
The BFSI security market size reached USD 90.43 billion in 2026 and is projected to hit USD 167.98 billion by 2031 at a 13.18% CAGR.
Which segment holds the largest share within the market?
Information Security dominated with 70.55% of BFSI security market share in 2025, reflecting regulatory focus on data and threat protection.
Which deployment model is expanding fastest?
Cloud-based solutions are the fastest-growing, expected to advance at 19.25% CAGR through 2031 as banks migrate workloads to scalable, AI-ready platforms.
How are quantum computing risks influencing spending?
Early pilots by major banks and Project Leap’s findings are prompting investment in quantum-safe cryptography, opening a new sub-segment within the market.
What drives the shift toward managed security services?
Talent shortages and 24/7 monitoring demands are motivating mid-tier institutions to outsource to managed SOC providers, fueling a 18.55% CAGR in this service line.
Page last updated on: