Cybersecurity Market Analysis by Mordor Intelligence
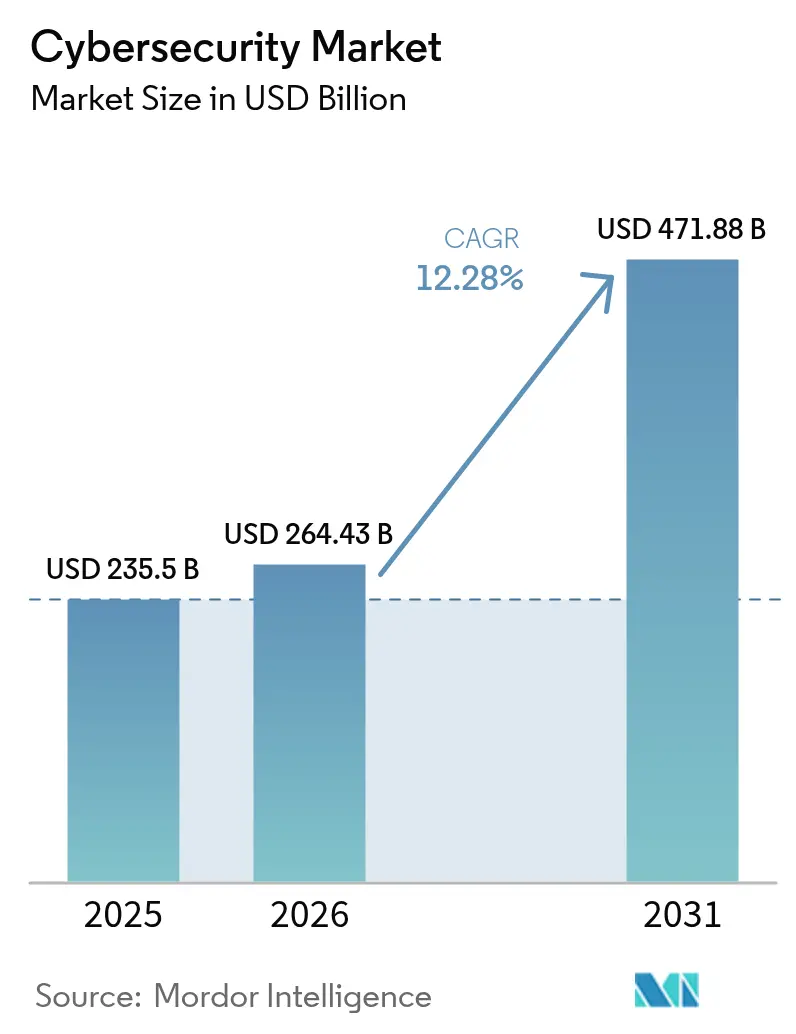
Cybersecurity Market size in 2026 is estimated at USD 264.43 billion, growing from 2025 value of USD 235.5 billion with 2031 projections showing USD 471.88 billion, growing at 12.28% CAGR over 2026-2031.
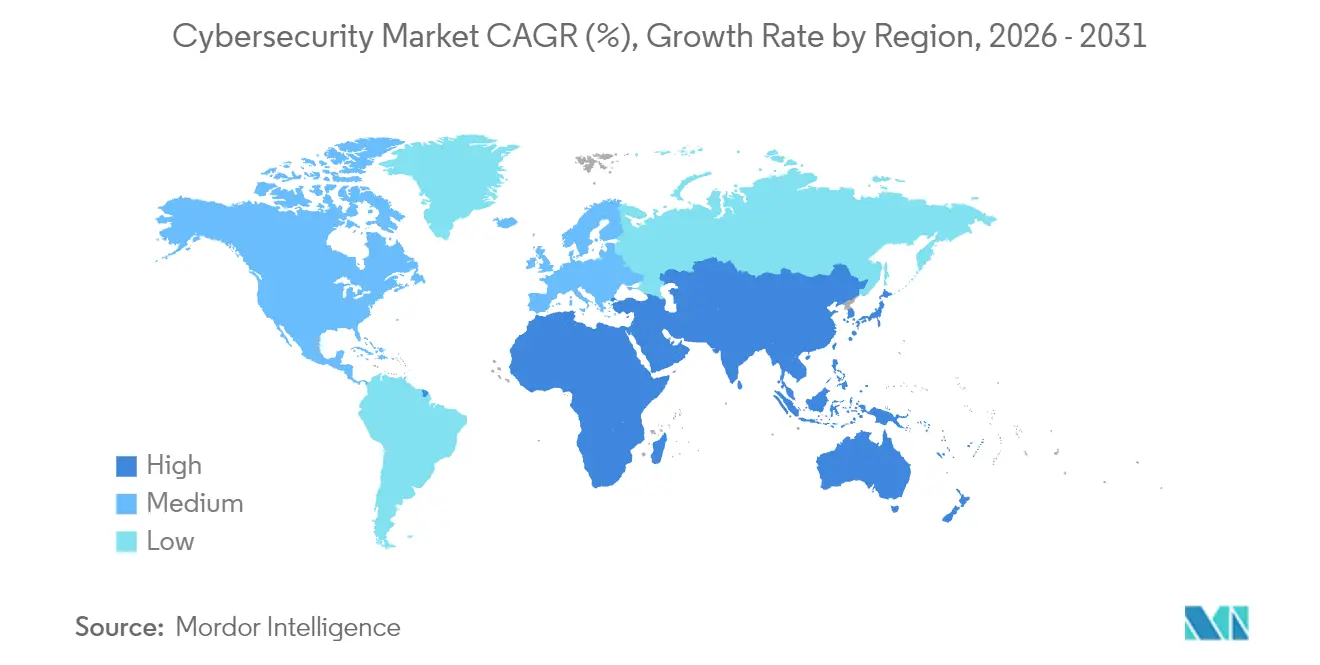
Increased spending on zero-trust architectures, the integration of IT and operational technology (OT) defenses, and preparations for quantum-ready encryption are the primary forces behind this expansion. North America retains spending leadership, while Asia-Pacific registers the most rapid gains as enterprises migrate workloads to cloud-first environments. Budget allocations are also rising as cyber-insurance underwriters demand verifiable controls, pushing organizations toward unified security platforms that simplify oversight. Simultaneously, platform consolidation through mergers and acquisitions is intensifying as vendors race to cover emerging threat vectors.
Key Report Takeaways
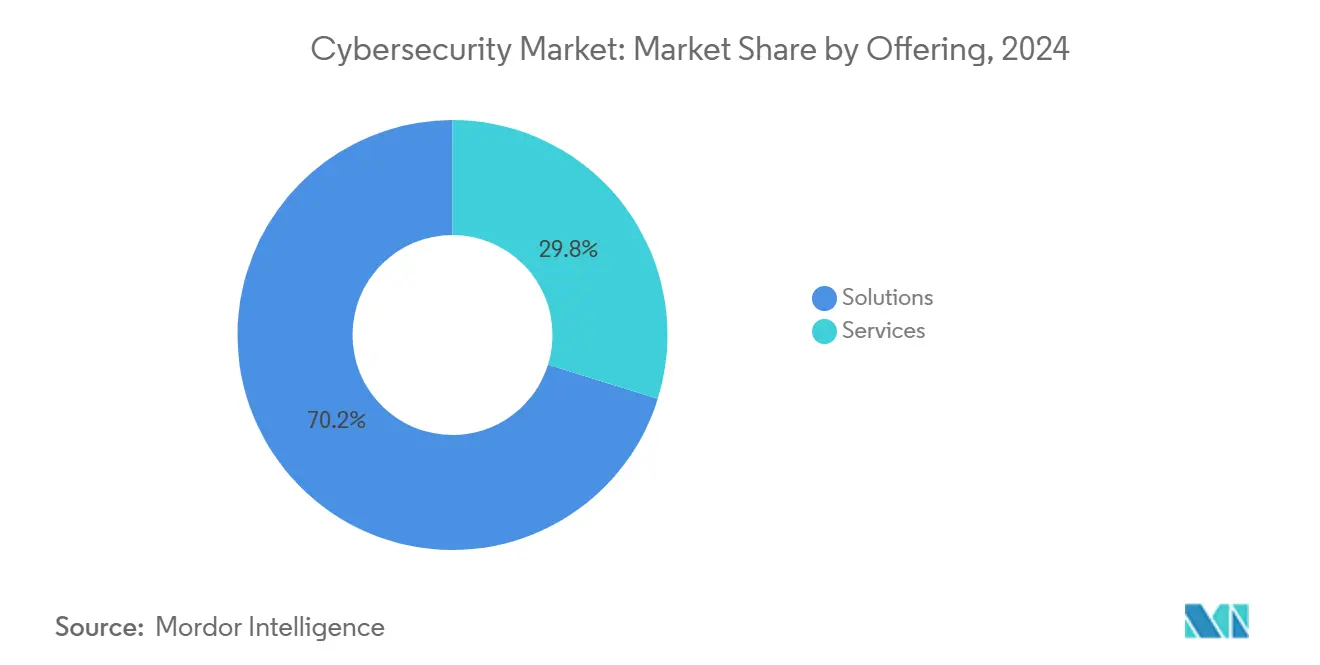
- By offering, solutions captured 69.55% of cybersecurity market share in 2025, while services are expanding through 2031 at 12.85% CAGR.
- By deployment mode, on-premise retained 59.40% share of the cybersecurity market size in 2025, yet cloud-based security is projected to compound at 15.95% CAGR.
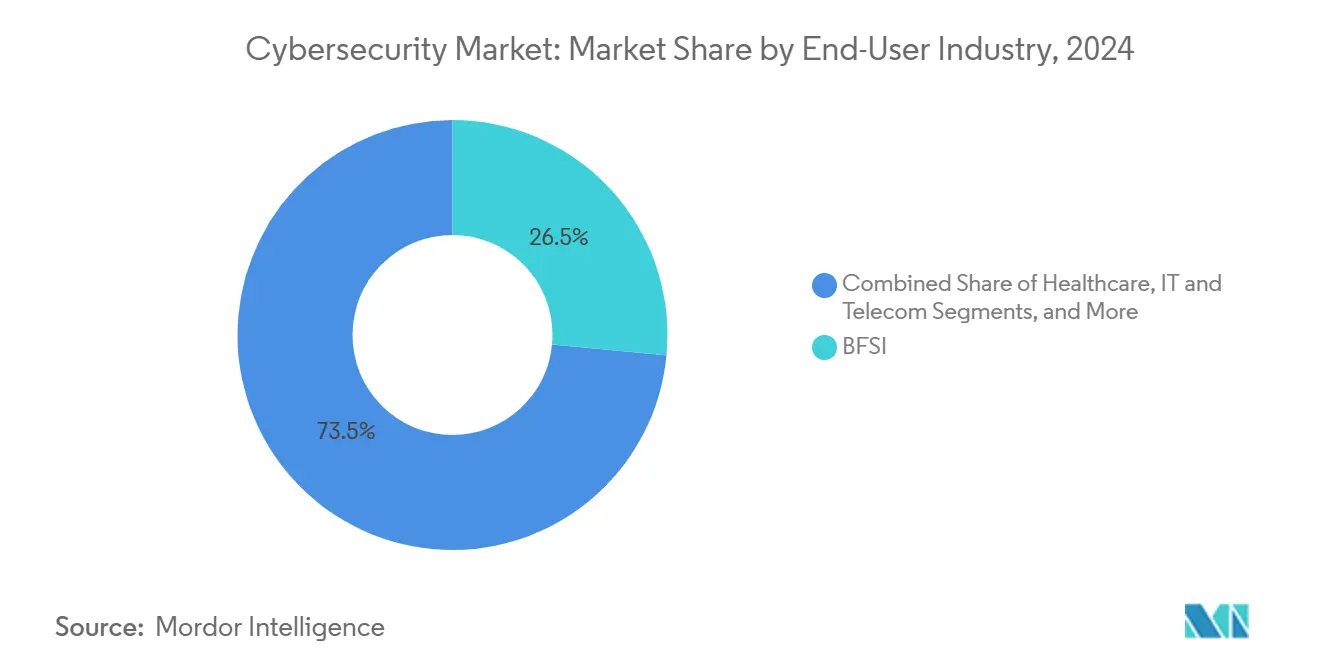
- By end-user industry, BFSI led with 26.10% revenue share in 2025; retail and e-commerce is forecast to advance at 15.05% CAGR to 2031.
- By end-user enterprise size, large organizations commanded 67.55% of the cybersecurity market size in 2025, while SMEs are set to grow at 13.25% CAGR.
- By geography, North America held 43.20% cybersecurity market share in 2025; Asia-Pacific is projected to post a 16.85% CAGR through 2031.
Note: Market size and forecast figures in this report are generated using Mordor Intelligence’s proprietary estimation framework, updated with the latest available data and insights as of 2026.
Global Cybersecurity Market Trends and Insights
Drivers Impact Analysis*
| Driver | (~) % Impact on CAGR Forecast | Geographic Relevance | Impact Timeline |
|---|---|---|---|
| Accelerated cloud-first digital transformation | +2.1% | Global; strongest in North America and Asia-Pacific | Medium term (2-4 years) |
| IT-OT security convergence across critical infrastructure | +1.8% | North America, Europe, and industrial Asia | Long term (≥4 years) |
| Zero-trust architecture mandates for hybrid workforce | +1.5% | North America and EU, expanding in Asia-Pacific | Short term (≤2 years) |
| Surge in cyber-insurance underwriting requirements | +1.2% | North America and Europe, emerging in Asia-Pacific | Medium term (2-4 years) |
| Digital-sovereignty regulations driving localised security stacks | +0.9% | Europe, China, India | Long term (≥4 years) |
| Timelines for quantum-ready cryptography migration | +0.8% | Global; early adoption in government and finance | Long term (≥4 years) |
| Source: Mordor Intelligence | |||
Accelerated Cloud-First Digital Transformation
Cloud migration is reshaping security investment priorities as perimeter controls fail in distributed environments. Cloud deployment is growing, outpacing on-premise allocations and driving demand for cloud-native application protection platforms that integrate identity, workload, and data safeguards. Enterprises are seeking unified consoles to reduce tool sprawl, and vendors are responding with platforms that correlate telemetry across hybrid estates, improving visibility and response efficiency [1]Tenable Research Team, “State of Cloud Security 2025,” tenable.com.
IT-OT Security Convergence Across Critical Infrastructure
Industry 4.0 forces formerly air-gapped systems online, exposing legacy control networks to the same adversaries that target IT assets, driving heightened demand in the cybersecurity market. Regulatory frameworks such as ISA/IEC 62443 now require integrated defenses that span production floors and data centers, encouraging investment in specialized OT threat detection and segmentation tools. Energy utilities are leading adoption as nation-state actors probe grid vulnerabilities, and returns on OT-focused security initiatives now exceed comparable IT projects in risk-reduction value.
Zero-Trust Architecture Mandates for Hybrid Workforce
Executive Order 14028 obliges U.S. federal agencies and contractors to shift to zero-trust models by 2025, prompting private-sector emulation. Identity-centred controls, continuous authentication, and micro-segmentation replace legacy VPN-based access, mitigating credential misuse that underlies 38% of breaches. Financial institutions now allocate 12% of IT budgets to zero-trust implementation, up from 9.7% four years ago, reflecting the strategic role of identity governance.
Surge in Cyber-Insurance Underwriting Requirements
Global cyber-insurance premiums are projected to grow, and underwriters increasingly require proof of endpoint protection, multi-factor authentication, and incident response readiness. This compliance-driven purchasing influences small and medium enterprises, which adopt cloud-delivered security stacks to satisfy insurers and secure coverage.
Restraints Impact Analysis*
| Restraint | (~) % Impact on CAGR Forecast | Geographic Relevance | Impact Timeline |
|---|---|---|---|
| Cyber-security talent deficit and wage inflation | -1.4% | Global; most acute in North America and Europe | Short term (≤2 years) |
| Integration complexity with legacy infrastructure | -0.7% | Manufacturing and finance worldwide | Medium term (2-4 years) |
| API sprawl expanding attack-surface complexity | -0.6% | Cloud-first enterprises globally | Short term (≤2 years) |
| SOC alert fatigue and false-positive overload limiting ROI | -0.5% | Organizations with mature SOCs | Medium term (2-4 years) |
| Source: Mordor Intelligence | |||
Cyber-Security Talent Deficit and Wage Inflation
The shortfall of 3.4 million professionals strains budgets as salaries climb for scarce skills in cloud, OT, and AI-driven defense. This constraint is driving market consolidation toward platforms that require fewer specialized personnel to operate, while simultaneously creating opportunities for vendors offering managed security services and AI-powered automation tools. The situation is exacerbated by high turnover rates, with 64% of cybersecurity professionals considering job changes due to workload stress, creating a continuous cycle of recruitment and training costs that impact organizational security budgets [2]Bitdefender Labs, “Global Cyber-Workforce Study 2025,” bitdefender.com.
Integration Complexity with Legacy Infrastructure
Manufacturers and banks struggle to bolt advanced controls onto decades-old systems while preserving uptime. Only 31% of industrial executives believe their current IT stack is future-ready, and 70% of financial institutions admit underspending because integration disrupts operations. Vendors that offer non-intrusive asset discovery and phased migration paths are gaining traction.
*Our updated forecasts treat driver/restraint impacts as directional, not additive. The revised impact forecasts reflect baseline growth, mix effects, and variable interactions.
Cybersecurity Market Segment Analysis
By Offering: Momentum Shifts Toward Platform Consolidation
Solutions retained 70.2% cybersecurity market share in 2024 and are set to expand at 13.1% CAGR as enterprises abandon isolated tools in favor of converged suites that unify cloud, identity, and network defenses. Application, cloud, and identity safeguards post the fastest gains, while network and endpoint controls grow more modestly as XDR overlays displace standalone products. Data protection rises in prominence amid new privacy rules, and integrated risk management embeds compliance workflows directly into security dashboards.
Services generated 29.8% of 2024 revenue, with managed offerings benefitting from the talent shortfall even as automation tempers growth. Advisory engagements remain essential for regulated verticals that require bespoke implementations. Providers that pair consulting with recurring managed detection and response services lock in long-term contracts, underpinning predictable revenue streams and deeper client relationships. The cybersecurity market continues to favour vendors that fuse products and services into seamless outcomes, streamlining procurement for resource-constrained security teams while reducing integration risk.
By Deployment Mode: Cloud Uptake Outpaces On-Premise Control
On-premise deployments still accounted for 60.1% of the cybersecurity market size in 2024, reflecting continued preference for direct oversight in highly regulated sectors such as government and healthcare. Yet the centre of gravity is shifting as cloud-native security accelerates at 16.4% CAGR on promises of elastic scale, faster update cycles, and integrated threat intelligence.
Small and medium enterprises gravitate to fully hosted suites that eliminate infrastructure overhead, whereas large organizations pursue hybrid models that keep sensitive workloads in house while routing less sensitive data to regional clouds to satisfy sovereignty mandates. Providers address compliance concerns through in-region data centres and audit-ready encryption controls, removing historical barriers to adoption. Unified consoles that provide visibility across on-premise, private, and public clouds are emerging as must-have capabilities, propelling demand for platforms that correlate logs from endpoints, identities, and network flows in a single analytic engine.
By End-User Industry: BFSI Holds Lead, Retail Surges
BFSI sustained 26.5% share of the cybersecurity market in 2024 owing to stringent regulations and the high value of financial data. Spending continues to grow as institutions implement zero-trust access, real-time fraud analytics, and quantum-ready cryptography to protect payment rails.
Retail and e-commerce is the fastest-growing vertical, advancing at 15.5% CAGR thanks to omnichannel strategies that expand digital attack surfaces. Breach costs tied to customer data exposure and payment fraud spur investment in tokenisation, application shielding, and API security. Industrial and defense entities invest heavily to secure OT environments, while IT-telecom players safeguard carrier networks that underpin national connectivity.. Manufacturers likewise escalate spending because 25.7% of 2024 cyber incidents targeted production systems, driving deployments of asset-centric anomaly detection that bridges IT and OT zones.

By End-User Enterprise Size: SMEs Lean on Cloud Simplicity
Large enterprises generated 68.3% of revenue in 2024 and continue to channel 12% of IT budgets into security, focusing on AI-driven analytics and managed extended detection and response services to counter sophisticated adversaries.
SMEs contributed 31.7% but will outpace their larger counterparts at 13.6% CAGR. Insurers now demand baseline controls before issuing cyber-policies, motivating smaller firms to adopt cloud platforms that bundle endpoint, email, and identity safeguards with simplified management portals. Lower upfront costs and subscription pricing remove capital-expenditure hurdles, while shared-responsibility models offload much of the operational burden to providers.Shared compliance dashboards that map controls to frameworks such as ISO 27001 and SOC 2 appeal to directors seeking board-level assurance without adding headcount.
Geography Analysis
North America controlled 43.20% of 2025 revenue in the cybersecurity market, underpinned by mature regulations and the presence of major vendors. Regional spending is forecast to surpass USD 137.6 billion by 2027 as Executive Order 14028 obliges extensive zero-trust migration. The United States reported 9,036 cyber incidents in 2023, dwarfing Europe’s 2,557 events and sustaining demand for advanced threat intelligence feeds and managed SOC services. Canada and Mexico contribute to growth through joint public-private programs that harmonise cross-border breach reporting and incident response.
Asia-Pacific is the fastest-growing area at 16.85% CAGR, with state-backed digital-nation plans elevating security to critical-infrastructure status. China, India, Japan, and South Korea allocate multi-year budgets to national cyber strategies, while Australia and New Zealand implement comprehensive resilience frameworks that require mandatory incident disclosure. Regional buyers often leapfrog legacy controls by adopting cloud-native security from the outset, accelerating uptake of identity-centric and AI-driven analytics.
Europe region growth is propelled by GDPR enforcement and the forthcoming NIS2 directive that expands coverage to more sectors. Germany, the United Kingdom, and France headline spending, whereas Central and Eastern European markets grow from a smaller base as they align with EU requirements. Sovereign-cloud initiatives in France and Spain stimulate demand for domestically hosted security stacks, while cross-border data-transfer restrictions accelerate adoption of privacy-enhancing encryption techniques.
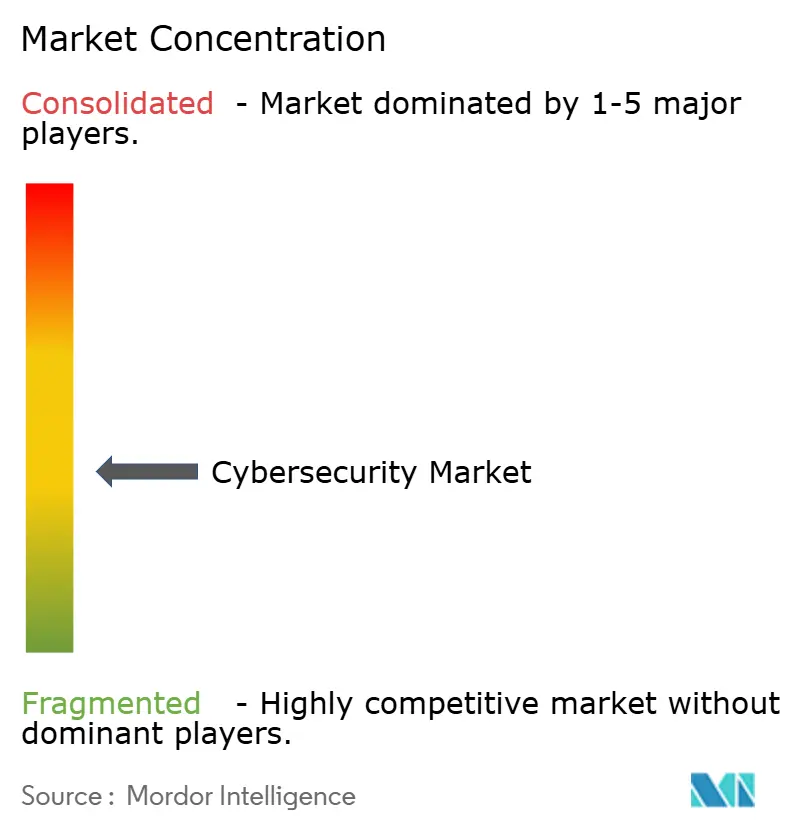
Competitive Landscape
The cybersecurity market remains moderately fragmented, though consolidation is rising as buyers prefer integrated platforms over disconnected point solutions. Google’s USD 23 billion bid for Wiz, Palo Alto Networks’ USD 500 million purchase of IBM’s QRadar unit, and CyberArk’s USD 1.54 billion acquisition of Venafi exemplify the scramble to expand cloud and identity capabilities [3]Douglas W. Hubbard, “Platform Consolidation in Cybersecurity,” journalofcyberpolicy.com.
Emerging companies exploit white space in quantum-ready encryption, OT defense, and AI-powered orchestration. Start-ups that design controls specifically for Kubernetes, serverless workloads, or machine-learning pipelines gain traction among digital-native enterprises. Patent filings for post-quantum key-exchange protocols and reinforcement-learning-based anomaly detection rose 28% year on year, underscoring the sector’s innovation tempo.
Partnerships between cloud service providers and security vendors deepen as hyperscalers embed native threat analytics, compliance tooling, and managed response options directly into their platforms. These alliances accelerate go-to-market cycles for smaller vendors and furnish hyperscalers with differentiated security postures that appeal to regulated customers.
Cybersecurity Industry Leaders
IBM Corporation
Microsoft Corporation
Cisco Systems, Inc.
Palo Alto Networks, Inc.
Fortinet, Inc.
- *Disclaimer: Major Players sorted in no particular order


Recent Industry Developments
- July 2025: Accenture and Microsoft committed joint funding to build generative-AI cyber tools that cut tool sprawl and reduce operating costs.
- July 2025: Invicti unveiled a next-generation application security platform with AI-enhanced dynamic testing and full-spectrum vulnerability visibility.
- May 2025: Radware opened new cloud security centres in Chennai, Mumbai, and Nairobi, expanding global mitigation capacity to 15 Tbps.
- April 2025: CrowdStrike added AI model scanning and Shadow AI detection to its Falcon platform, broadening unified protection across hybrid and multi-cloud environments.
Global Cybersecurity Market Report Scope
The cybersecurity market is defined based on the revenues generated from the solutions and services used in various end-user industries globally. The analysis is based on the market insights captured through secondary research and the primaries. The market also covers the major factors impacting its growth in terms of drivers and restraints. The study tracks the key market parameters, underlying growth influencers, and major vendors operating in the industry, which supports the market estimations and growth rates over the forecast period.
The cybersecurity market is segmented by offerings (solutions [application security, cloud security, data security, identity access management, infrastructure protection, integrated risk management, network security, and other solution types] and services [professional services and managed services]), by deployment (On-premise, and cloud), and by end-user vertical (IT and telecommunication, BFSI, retail and e-commerce, oil gas and energy, manufacturing, government, and defense, and other end-user industries), geography (North America [United States and Canada], Europe [United Kingdom, Germany, France, Italy, Spain, Greece, Rest of Europe], AsiaPacific [China, India, Japan, Australia, Southeast Asia [Indonesia, Philippines, Malaysia, Singapore, Rest of Southeast Asia], Rest of Asia Pacific], Latin America [Brazil, Argentina, Mexico, Rest of Latin America], lastly, Middle East and Africa [Saudi Arabia, GCC [United Arab Emirates, Others], South Africa, Rest of the Middle East and Africa]). The market sizes and forecasts are provided in terms of value in (USD) for all the above segments.
| Solutions | Application Security |
| Cloud Security | |
| Data Security | |
| Identity and Access Management | |
| Infrastructure Protection | |
| Integrated Risk Management | |
| Network Security | |
| End-point Security | |
| Services | Professional Services |
| Managed Services |
| Cloud |
| On-Premise |
| BFSI |
| Healthcare |
| IT and Telecom |
| Industrial and Defense |
| Retail and E-commerce |
| Energy and Utilities |
| Manufacturing |
| Others |
| Large Enterprises |
| Small and Medium Enterprises (SMEs) |
| North America | United States | |
| Canada | ||
| Mexico | ||
| South America | Brazil | |
| Argentina | ||
| Rest of South America | ||
| Europe | Germany | |
| United Kingdom | ||
| France | ||
| Italy | ||
| Spain | ||
| Russia | ||
| Rest of Europe | ||
| Asia-Pacific | China | |
| Japan | ||
| India | ||
| South Korea | ||
| Australia and New Zealand | ||
| Rest of Asia-Pacific | ||
| Middle East and Africa | Middle East | Saudi Arabia |
| United Arab Emirates | ||
| Turkey | ||
| Rest of Middle East | ||
| Africa | South Africa | |
| Nigeria | ||
| Egypt | ||
| Rest of Africa | ||
| By Offering | Solutions | Application Security | |
| Cloud Security | |||
| Data Security | |||
| Identity and Access Management | |||
| Infrastructure Protection | |||
| Integrated Risk Management | |||
| Network Security | |||
| End-point Security | |||
| Services | Professional Services | ||
| Managed Services | |||
| By Deployment Mode | Cloud | ||
| On-Premise | |||
| By End-user Industry | BFSI | ||
| Healthcare | |||
| IT and Telecom | |||
| Industrial and Defense | |||
| Retail and E-commerce | |||
| Energy and Utilities | |||
| Manufacturing | |||
| Others | |||
| By End-user Enterprise Size | Large Enterprises | ||
| Small and Medium Enterprises (SMEs) | |||
| By Geography | North America | United States | |
| Canada | |||
| Mexico | |||
| South America | Brazil | ||
| Argentina | |||
| Rest of South America | |||
| Europe | Germany | ||
| United Kingdom | |||
| France | |||
| Italy | |||
| Spain | |||
| Russia | |||
| Rest of Europe | |||
| Asia-Pacific | China | ||
| Japan | |||
| India | |||
| South Korea | |||
| Australia and New Zealand | |||
| Rest of Asia-Pacific | |||
| Middle East and Africa | Middle East | Saudi Arabia | |
| United Arab Emirates | |||
| Turkey | |||
| Rest of Middle East | |||
| Africa | South Africa | ||
| Nigeria | |||
| Egypt | |||
| Rest of Africa | |||


Key Questions Answered in the Report
What is the current size of the cybersecurity market?
The cybersecurity market size is USD 264.43 billion in 2026 and is forecast to reach USD 471.88 billion by 2031.
Which region is growing the fastest?
Asia-Pacific is projected to record a 16.85% CAGR between 2026 and 2031, the highest among all regions.
Which deployment mode is expanding most quickly?
Cloud-based security is the fastest-growing mode, expected to compound at 15.95% through 2031 as enterprises seek scalable protection.
Why is zero-trust architecture gaining momentum?
Government mandates, rising credential-based attacks, and hybrid work models are driving organizations to shift from perimeter defenses to identity-centric zero-trust frameworks.
Page last updated on: