Asia-Pacific Cybersecurity Market Analysis by Mordor Intelligence
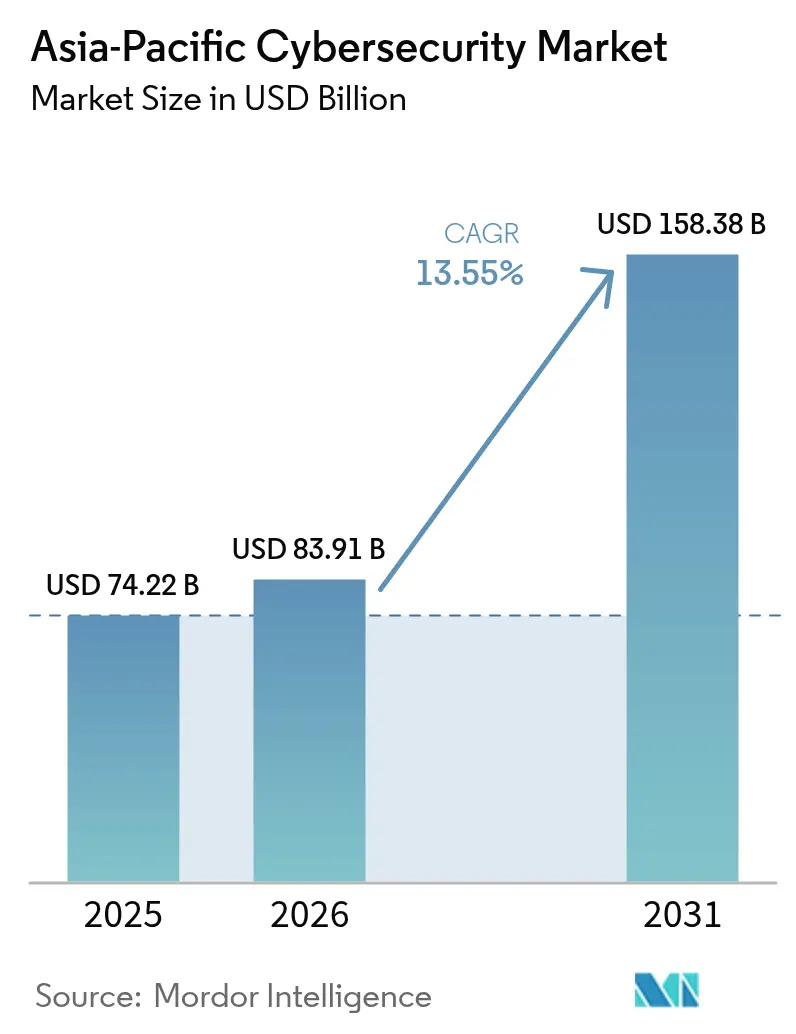
The Asia-Pacific cybersecurity market size is projected to expand from USD 74.22 billion in 2025 and USD 83.91 billion in 2026 to USD 158.38 billion by 2031, registering a CAGR of 13.55% between 2026 and 2031. The rapid rise in data-sovereignty mandates, proliferation of 5G networks, and a stubborn talent shortage are reshaping enterprise investment priorities. Telecommunications carriers are hardening their cloud-native cores, while industrial firms are diverting budgets toward safeguarding operational technology assets. Multinational vendors face intensifying competition from regional champions that leverage domestic-content rules and localized support. Meanwhile, managed security providers benefit from enterprises that lack in-house expertise yet must comply with newly enforced breach-notification laws.
Key Report Takeaways
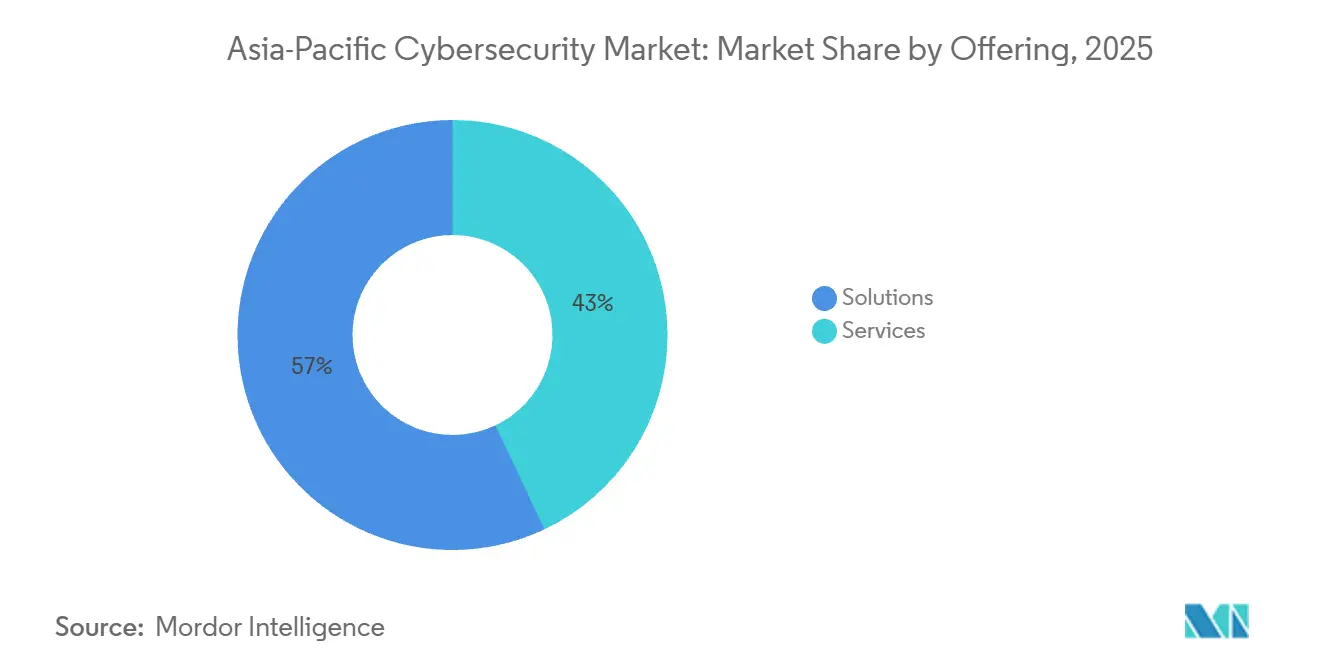
- By offering, solutions held 57.04% of the Asia-Pacific cybersecurity market share in 2025, while services are forecast to grow at the fastest 14.63% CAGR through 2031.
- By deployment mode, on-premises architectures commanded 61.88% of market share in 2025, whereas cloud deployments are advancing at a 14.75% CAGR through 2031.
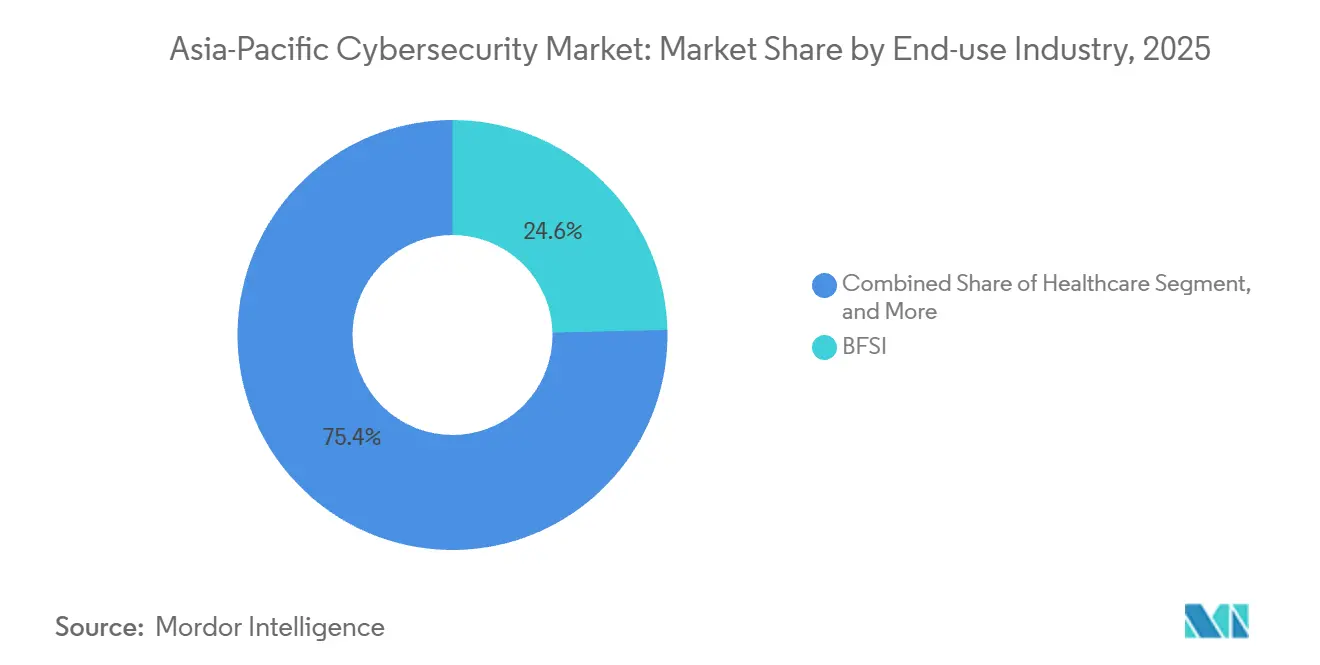
- By end-use industry, banking, financial services, and insurance led the Asia-Pacific cybersecurity market with 24.62% of the market size in 2025, while healthcare is projected to expand at the highest 14.36% CAGR through 2031.
- By enterprise size, large enterprises captured a 66.69% share in 2025, whereas small and medium enterprises will register the quickest 14.82% CAGR to 2031.
- By country, China dominated with 44.27% regional share in 2025, whereas India is expected to post the strongest 15.02% CAGR between 2026 and 2031.
Note: Market size and forecast figures in this report are generated using Mordor Intelligence’s proprietary estimation framework, updated with the latest available data and insights as of 2026.
Asia-Pacific Cybersecurity Market Trends and Insights
Drivers Impact Analysis*
| Driver | (~) % Impact on CAGR Forecast | Geographic Relevance | Impact Timeline |
|---|---|---|---|
| Government Data-Sovereignty Mandates Accelerating Domestic Cybersecurity Spend | +2.8% | China, India, Indonesia, Vietnam, wider ASEAN | Medium term (2-4 years) |
| 5G Roll-Outs Creating New Network Threat Surfaces for Telecommunications Providers | +2.3% | South Korea, Japan, China, Australia, urban ASEAN hubs | Short term (≤ 2 years) |
| Surge in Digital-Payments and E-Commerce Fraud Prompting Security Investments | +2.1% | India, ASEAN, China tier-2 cities | Short term (≤ 2 years) |
| Escalating State-Sponsored Attacks on Critical Infrastructure Stimulating OT Security | +1.9% | Australia, Japan, South Korea, Taiwan | Medium term (2-4 years) |
| SME Cloud-Migration Wave Necessitating Cloud Workload Protection | +1.7% | Singapore, Japan, Australia, India metro regions | Medium term (2-4 years) |
| Persistent AI-Driven Deepfake Fraud Expanding Identity-Centric Security Demand | +1.5% | Hong Kong, Singapore, Japan, South Korea | Long term (≥ 4 years) |
| Source: Mordor Intelligence | |||
Government Data-Sovereignty Mandates Accelerating Domestic Cybersecurity Spend
Stringent data-localization statutes in China, India, Indonesia, and Vietnam compel critical-information-infrastructure operators to store user and transactional data in country. These rules push enterprises toward locally hosted security appliances and spur demand for domestic cloud regions. Cisco, Fortinet, and Palo Alto Networks responded by opening new data-center clusters in Mumbai, Jakarta, and Hanoi during 2025 to maintain compliance.[1]National People’s Congress of China, “Data Security Law Amendments,” npc.gov.cn
5G Roll-Outs Creating New Network Threat Surfaces for Telecommunications Providers
Software-defined 5G cores, network slicing, and distributed edge nodes enlarge attack windows that legacy perimeter defenses cannot monitor. SK Telecom blocked more than 1.2 million DDoS attempts on slice management interfaces in 2025, demonstrating the immediacy of threats. Carriers now embed micro-segmentation and automated anomaly detection into radio access networks, lifting spending on carrier-grade firewalls and analytics.[2]Ministry of Science and ICT South Korea, “5G Infrastructure Statistics,” msit.go.kr
Surge in Digital-Payments and E-Commerce Fraud Prompting Security Investments
UPI transactions in India topped 16 billion in December 2025, driving a parallel spike in credential-phishing campaigns. The Reserve Bank of India mandated that payment aggregators deploy real-time risk scoring and suspicious-activity reporting. This energized demand for AI-powered fraud management tools across India, Indonesia, and Thailand.[3]Reserve Bank of India, “Master Direction on Payment Aggregators and Payment Gateways,” rbi.org.in The increasing adoption of digital payment systems has further highlighted the need for robust cybersecurity measures.
Escalating State-Sponsored Attacks on Critical Infrastructure Stimulating OT Security
Operational technology networks in power grids and semiconductor fabs experienced disruptive breaches in 2025. These incidents prompted governments to introduce mandatory segmentation, continuous monitoring, and quarterly audits. Taiwan Semiconductor Manufacturing Company allocated USD 50 million to roll out OT-specific detection platforms, highlighting the sizable budgets now flowing into this once-overlooked niche.
Restraints Impact Analysis*
| Restraint | (~) % Impact on CAGR Forecast | Geographic Relevance | Impact Timeline |
|---|---|---|---|
| Cybersecurity Talent Shortage | -1.4% | India, Vietnam, Indonesia, Philippines | Medium term (2-4 years) |
| Fragmented Regional Compliance Regimes | -1.1% | ASEAN, India, China provincial regulations | Long term (≥ 4 years) |
| High Price Sensitivity Among SMEs | -0.9% | Indonesia, Vietnam, Philippines, India tier-2 and tier-3 | Short term (≤ 2 years) |
| Export-Control Disruptions on Hardware | -0.7% | China, Hong Kong, Macau | Medium term (2-4 years) |
| Source: Mordor Intelligence | |||
Acute Cybersecurity Talent Shortage Inflating Service Costs in Emerging Economies
Asia-Pacific lacked 2.16 million qualified practitioners in 2025. This shortage inflated wages 40% above 2023 levels and forced enterprises to outsource incident response to managed service providers. The scarcity remains acute in India and Vietnam, where universities cannot graduate specialists fast enough to satisfy regulatory mandates. This talent gap has created significant challenges for organizations striving to meet compliance requirements. Additionally, the reliance on managed service providers has increased operational costs for businesses in the region.
Fragmented Regional Compliance Regimes Complicating Solution Standardization
Conflicting breach-notification and data-residency deadlines across ASEAN nations force vendors to maintain multiple SKUs and inflate certification costs. Enterprises operating in both Singapore and Malaysia juggle six-hour and 72-hour reporting windows, respectively, stretching security-operations resources and delaying purchasing decisions. Additionally, the lack of harmonized cybersecurity regulations across the region creates operational inefficiencies, compelling companies to allocate significant resources to compliance management. This fragmented regulatory landscape further complicates cross-border operations, increasing the demand for specialized legal and technical expertise.
*Our updated forecasts treat driver/restraint impacts as directional, not additive. The revised impact forecasts reflect baseline growth, mix effects, and variable interactions.
Segment Analysis
By Offering: Services Capture Growth Momentum
Services represented 42.96% share in 2025, yet the services slice of the Asia-Pacific cybersecurity market size is forecast to expand at 14.63% CAGR to 2031, outpacing solutions. Demand for 24/7 monitoring, incident response, and compliance audits drives multiyear managed-security agreements among banks and telcos. Rising wage premiums for certified analysts reinforce outsourcing decisions that funnel new revenue to Tata Consultancy Services, Infosys, and NTT.
Solutions still account for the largest absolute revenue at 57.04% of 2025 spend, with application, cloud, and identity security modules leading incremental sales. Vendors embed zero-trust principles and container-security functions to secure DevOps pipelines, but hardware refresh cycles are lengthening as enterprises wait for export-control clarity. Feature convergence sees next-generation firewalls bundling endpoint Detection and response modules, lowering stand-alone appliance demand yet elevating average selling prices per platform.
By Deployment Mode: Cloud-Native Architectures Accelerate
Cloud deployments absorbed 38.12% share in 2025 and will expand at 14.75% CAGR, steadily eroding on-premise dominance. SME buyers gravitate toward subscription-based offerings that bypass capital outlays, while regulators in Singapore and Australia now accept certified public-cloud services for sensitive workloads. The Asia-Pacific cybersecurity market share held by cloud platforms is poised to widen as hyperscalers establish more regional availability zones that comply with local residency rules.
Conversely, on-premise systems retained 61.88% share in 2025, anchored by large banks, defense ministries, and state-owned utilities within China, Japan, and South Korea that prefer air-gapped environments. Hybrid SIEM deployments gain traction, forwarding logs from branch appliances to central cloud analytics for faster threat correlation. This coexistence enables gradual migration paths and preserves legacy investments.
By End-Use Industry: Healthcare Fastest, BFSI Largest
Banking, financial services, and insurance captured 24.62% of 2025 regional spending, making it the largest slice of the Asia-Pacific cybersecurity market. Strict capital adequacy and fraud-prevention regulations oblige continuous upgrades to identity verification, transaction monitoring, and encryption. Additionally, the increasing adoption of digital banking and mobile payment platforms has heightened the need for robust cybersecurity measures to protect sensitive customer data and prevent financial fraud.
Healthcare is projected to lead growth at 14.36% CAGR as ransomware attacks cripple hospital networks, prompting ministries of health in Singapore and South Korea to impose quarterly drills and mandate next-generation antivirus. Investments focus on segmentation between medical-device networks and administrative systems, immutable backups, and endpoint detection that prevents lateral movement. Furthermore, the growing reliance on telemedicine and electronic health records has amplified the demand for advanced cybersecurity solutions to safeguard patient information and ensure uninterrupted healthcare services.

By Enterprise Size: SMEs Narrow the Gap
Large enterprises held 66.69% of market share in 2025 due to expansive attack surfaces and dedicated SOC budgets. They adopt automation and AI-driven correlation engines that integrate 30+ security feeds, ensuring comprehensive threat detection and response. Costly compliance failures further incentivize the adoption of advanced tooling, as enterprises prioritize safeguarding sensitive data and meeting regulatory requirements. Additionally, the increasing complexity of cyber threats has driven large organizations to invest heavily in robust cybersecurity frameworks.
Small and medium enterprises, however, will record a 14.82% CAGR to 2031, lifted by affordable cloud security suites priced per user and national subsidy programs. Singapore’s Cybersecurity Tooling Assistance grants and India’s Startup incentives lower acquisition barriers, allowing SMEs to deploy endpoint security and email-phishing defenses previously reserved for larger peers. The growing adoption of digital transformation among SMEs has further amplified the need for cost-effective cybersecurity solutions. Moreover, the rise in targeted attacks on smaller businesses has heightened awareness, prompting these enterprises to prioritize cybersecurity investments.
Geography Analysis
China contributed 44.27% of the Asia-Pacific cybersecurity market in 2025 thanks to compulsory localization and preferential procurement for domestic vendors. Huawei, Sangfor, and Venustech win telecom and government contracts where imported hardware faces export-control scrutiny. Enforcement of the Data Security Law’s expanded critical-infrastructure scope drives recurring audits and boosts domestic appliance demand.
India will post the fastest 15.02% CAGR through 2031 as digital-payment fraud and a swelling fintech ecosystem force rapid adoption of real-time monitoring, behavioral biometrics, and data-loss-prevention. The increasing sophistication of cyber threats further drives the demand for advanced security solutions across industries. Local integrators bundle cloud-security services into digital-transformation projects, while reserve-bank directives accelerate enterprise procurement cycles. These initiatives are fostering a robust cybersecurity infrastructure, ensuring businesses can adapt to evolving regulatory and technological landscapes.
Japan, South Korea, Australia, and New Zealand represent mature, compliance-led demand where large enterprises refresh aging perimeter defenses and industrial firms retrofit OT zones. ASEAN remains heterogeneous; Singapore commands the highest per-capita spend, whereas Indonesia and Vietnam contribute faster percentage growth from smaller bases despite price sensitivity among SMEs. Rest-of-Asia-Pacific markets such as Pakistan and Bangladesh form early-stage opportunities tied to public-sector digitization.
Competitive Landscape
The market is moderately fragmented. Palo Alto Networks, Fortinet, and Cisco consolidate point products into unified platforms, appealing to resource-constrained security teams. Domestic champions such as Huawei in China, NEC in Japan, and AhnLab in South Korea benefit from local trust, language support, and national procurement preferences.
Managed security services are the fastest-scaling channel as enterprises lacking expert staff outsource detection and response. Tata Consultancy Services and NTT secure multiyear contracts anchored in offshore SOCs, while Accenture and Deloitte expand consulting for zero-trust roadmaps. Emerging vendors such as Darktrace and SentinelOne differentiate through machine-learning analytics and autonomous response, reducing alert fatigue.
Export-control limitations on advanced semiconductors extend refresh intervals for high-throughput firewalls, nudging buyers toward software-defined alternatives. Vendors race to patent behavioral analytics, with Palo Alto Networks boosting R&D to USD 1.8 billion in 2025. Compliance certifications ISO 27001, SOC 2, MTCS serve as table stakes in procurement, especially where regulators audit vendor controls.
Asia-Pacific Cybersecurity Industry Leaders
Cisco Systems, Inc.
IBM Corporation
Huawei Technologies Co., Ltd.
Palo Alto Networks, Inc.
Check Point Software Technologies Ltd.
- *Disclaimer: Major Players sorted in no particular order


Recent Industry Developments
- February 2026: Palo Alto Networks partnered with Tata Consultancy Services to deliver managed Prisma Cloud services across India, Southeast Asia, and Australia.
- January 2026: CrowdStrike acquired Bionic for USD 350 million, integrating agentless runtime protection into the Falcon platform.
- December 2025: Fortinet opened a USD 53 million security operations center in Sydney to support critical-infrastructure clients.
- November 2025: Huawei unveiled HiSec 6.0, an AI-driven threat-hunting framework integrated with the vendor’s 5G core equipment.
Asia-Pacific Cybersecurity Market Report Scope
IT advancements, communication technologies, and smart energy grids are transforming the landscapes of nearly every country's essential infrastructure and commercial networks. Rapidly changing technology, however, brings with it rapidly advancing hazards. Cybersecurity solutions assist a company in monitoring, detecting, reporting, and countering cyber threats, which include internet-based attempts to damage or disrupt information systems and hack crucial data using spyware and malware, as well as phishing to protect data confidentiality. The study's market size is based on end-user spending on cybersecurity systems and services.
The Asia-Pacific Cybersecurity Market Report is Segmented by Offering (Solutions, and Services), Deployment Mode (On-Premise, Cloud), End-use Industry (IT and Telecom, BFSI, Healthcare, Industrial Manufacturing, Retail and E-commerce, Energy and Utilities, Aerospace, Military and Defense, and Other End-use Industries), End-User Enterprise Size (Large Enterprises, and Small and Medium Enterprises), and Country (China, Japan, India, South Korea, ASEAN, Australia, New Zealand, and Rest of Asia-Pacific). The Market Forecasts are Provided in Terms of Value (USD).
| Solutions | Application Security |
| Cloud Security | |
| Data Security | |
| Identity and Access Management | |
| Infrastructure Protection | |
| Integrated Risk Management | |
| Network Security | |
| Endpoint Security | |
| Services | Professional Services |
| Managed Services |
| On-Premise |
| Cloud |
| IT and Telecom |
| BFSI |
| Healthcare |
| Industrial Manufacturing |
| Retail and E-commerce |
| Energy and Utilities |
| Aerospace, Military and Defense |
| Other End-use Industries |
| Large Enterprises |
| Small and Medium Enterprises (SMEs) |
| China |
| Japan |
| India |
| South Korea |
| ASEAN |
| Australia |
| New Zealand |
| Rest of Asia-Pacific |
| By Offering | Solutions | Application Security |
| Cloud Security | ||
| Data Security | ||
| Identity and Access Management | ||
| Infrastructure Protection | ||
| Integrated Risk Management | ||
| Network Security | ||
| Endpoint Security | ||
| Services | Professional Services | |
| Managed Services | ||
| By Deployment Mode | On-Premise | |
| Cloud | ||
| By End-use Industry | IT and Telecom | |
| BFSI | ||
| Healthcare | ||
| Industrial Manufacturing | ||
| Retail and E-commerce | ||
| Energy and Utilities | ||
| Aerospace, Military and Defense | ||
| Other End-use Industries | ||
| By End-User Enterprise Size | Large Enterprises | |
| Small and Medium Enterprises (SMEs) | ||
| By Country | China | |
| Japan | ||
| India | ||
| South Korea | ||
| ASEAN | ||
| Australia | ||
| New Zealand | ||
| Rest of Asia-Pacific | ||


Key Questions Answered in the Report
What is the projected value of Asia-Pacific cybersecurity solutions and services in 2031?
The Asia-Pacific cybersecurity market size is forecast to reach USD 158.38 billion by 2031.
Which country is expected to grow fastest through 2031?
India is projected to register the highest 15.02% CAGR through 2031, outpacing all other regional markets.
Why are managed security services gaining traction?
Acute talent shortages and stricter compliance rules push enterprises to outsource 24/7 monitoring and incident response to managed security providers.
Which industry vertical will lead spending growth?
Healthcare is set to expand at a 14.36% CAGR as hospitals harden defenses against ransomware and data-breach risks.
How will 5G adoption influence cybersecurity budgets?
Edge-heavy 5G architectures enlarge attack surfaces, compelling carriers to embed micro-segmentation, analytics, and API security, adding 2.3 percentage points to regional CAGR.
What deployment model will outpace others by 2031?
Cloud-based security is projected to grow at 14.75% CAGR, narrowing the gap with on-premise architectures as public-cloud regions meet data-residency mandates.
Page last updated on: